ATICC 1
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records
are made on a daily basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in
this analysis.
Purpose
The Auto Theft Intelligence Coordination Center (ATICC) has
prepared the following assessment regarding the occurrence of
motor vehicle theft in Colorado, during the period of January 1,
2019 through December 31, 2019.
Data used in this report is sourced from the Colorado Stolen
Vehicle Database Repository administered by the ATICC. The
repository contains records of all stolen and recovered vehicles
entered and removed from the Colorado Crime Information
Center (CCIC).
Key Findings
The Colorado Stolen Vehicle Database Repository captured a total of 20,271 motor vehicle thefts
statewide during 2019.
Compared to the 20,952 thefts that were reported during 2018, Colorado experienced a 3.3%
decrease in motor vehicle thefts during 2019.
66% of stolen vehicles were reported in the Denver Metro area, 20% in Southern area, 9% in
Northern area, 2% in the Western area, 2% in the South West area, and 1% in the Eastern area.
17,047 stolen vehicles were recovered in 2019, which equates to an 88% vehicle recovery rate;
The completion of information in the ATICC supplemental continues to be an area of concern.
ATICC staff will coordinate communications and/or training opportunities for the appropriate
data entry personnel.
The top five vehicles stolen statewide in 2019 were (in ranking order): Honda Civic, Honda
Accord, Dodge/RAM RAM*; Ford F250 and Chevrolet Silverado. (*As of 2009, RAM became a
“make” under FIAT management. Dodge remained the “make” for the passenger style vehicles
while RAM became the “make” for the pickup/truck style vehicles. As an initial standard, ATICC
and CMATT analysts currently combine all pickup/truck styles under DODGE/RAM “make”. A
more standard model will be sought moving forward.
Although mostly accurate, the ATICC continues to strive to improve collection standards and
account for gaps that exist. Reporting standards in 2019 are similar to 2018 through the ATICC
database. However, the ATICC database results should not be directly compared to the 2019 FBI
Crime in the US Report due to different collection methods.

ATICC 2
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records
are made on a daily basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in
this analysis.
Contents
Purpose ......................................................................................................................................................... 1
Key Findings .................................................................................................................................................. 1
General Observations ................................................................................................................................... 3
Colorado Auto Theft Hot Spots ..................................................................................................................... 4
Statistics ........................................................................................................................................................ 5
Puffer Vehicles .............................................................................................................................................. 7
Auto Theft Impact ......................................................................................................................................... 7
Call to Action ................................................................................................................................................. 9
Appendix A – Stolen Vehicle Data Validation Processes and Reliability ....................................................... 9
ATICC 3
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records
are made on a daily basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in
this analysis.
General Observations
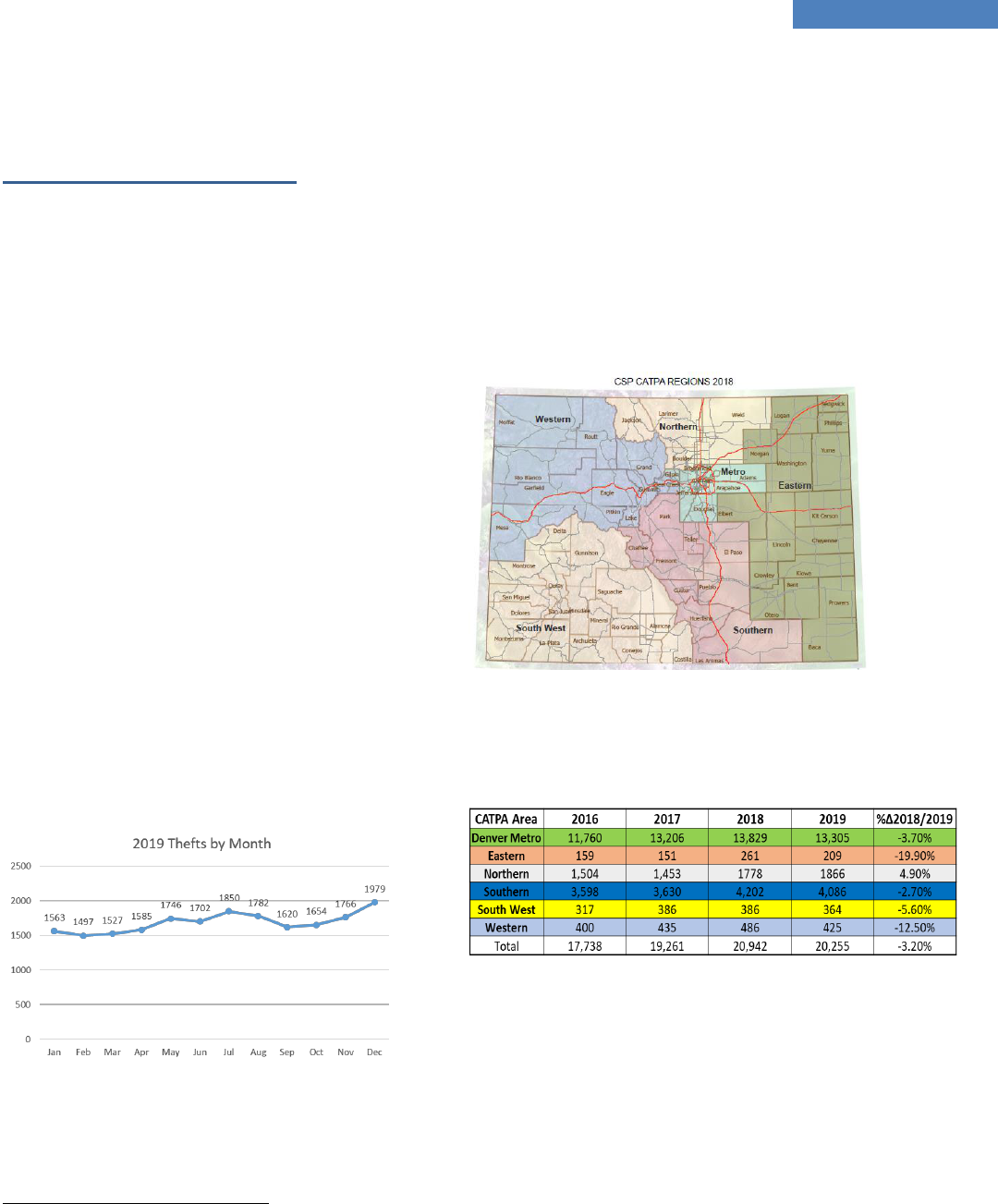
Auto theft had continued on a gradual rise since 2012.
In 2019, Colorado experienced a 3.3% decrease in
auto theft from the previous year.
In 2019, there was an average of 1,689 vehicles stolen
every month in Colorado. This is a monthly decrease
of approximately 57 less stolen vehicles per month
than experienced in 2018 (1746). There was an
average of 390 vehicles reported stolen every week,
and an average of 56 vehicle thefts every day in the
state.
Using the F.B.I.'s average dollar loss per stolen
vehicle reported in 2019 ($8,407)
1
, Colorado
experienced $170,418,297 loss. Compared to 2018,
there was an additional $6,649,977 of loss in 2019
(The value assessed by the FBI increased since the
last reported value). This value is not considered an
average vehicle value but a value based on the
economic survival loss related to the vehicle's theft
from the time it was stolen until it was recovered.
In 2019, mid-summer through early fall showed a
decrease rate of theft pattern. However, from late fall
through the end of the year there was an increase
theft pattern ending with 1979 thefts reported in
December.
1
https://ucr.fbi.gov
The US Census Bureau estimated the population of
Colorado in 2019 was 5,758,736.
2
On average
Colorado has observed a population growth of 79,663
per year for the last five years. With this in mind,
there was an annual average of 352 vehicle thefts per
100,000 people. This is a decrease of 22 vehicles per
capita compared to 2018 (374).
Colorado is divided into six different areas pertaining
to auto theft and auto theft task forces. The Denver
Metro and Southern areas accounted for an 86%
majority of reported vehicle thefts.
2
https://www.census.gov/
ATICC 4
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records
are made on a daily basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in
this analysis.
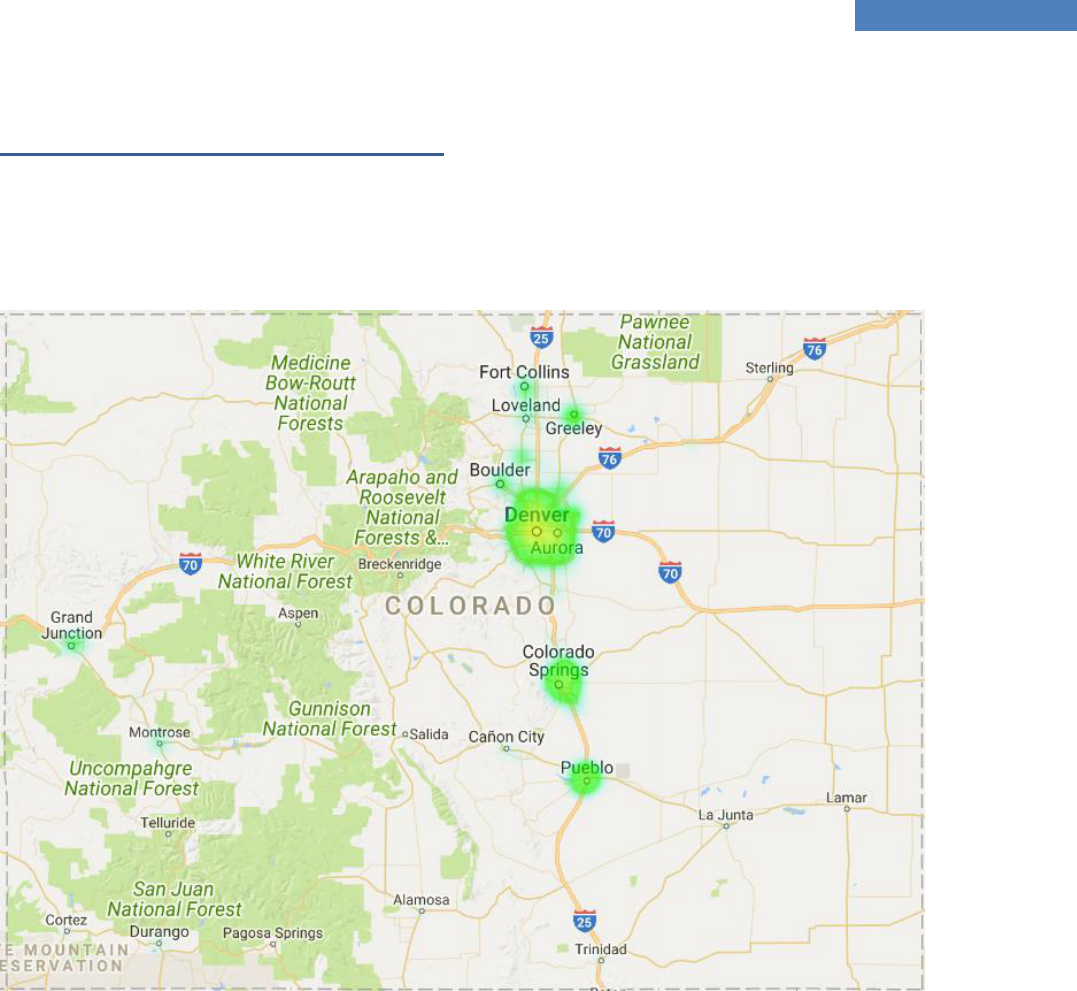
Colorado Auto Theft Hot Spots
In 2019 the hot spots for auto theft occurred in and around larger cities. As seen in the heat map below, these
include: Boulder, Canon City, Colorado Springs, Denver Metro, Fort Collins, Grand Junction, Greeley, La Junta,
Lafayette/Erie, Loveland, Montrose, Pueblo, and Sterling.
ATICC 5
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records
are made on a daily basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in
this analysis.
Statistics
The following reporting agencies reported three or
more vehicle thefts per week. These communities
accounted for 87% of all reported vehicles thefts in
the state. These reporting agencies were located in
or around Denver, Colorado Springs, Pueblo, Fort
Collins, and Greeley.
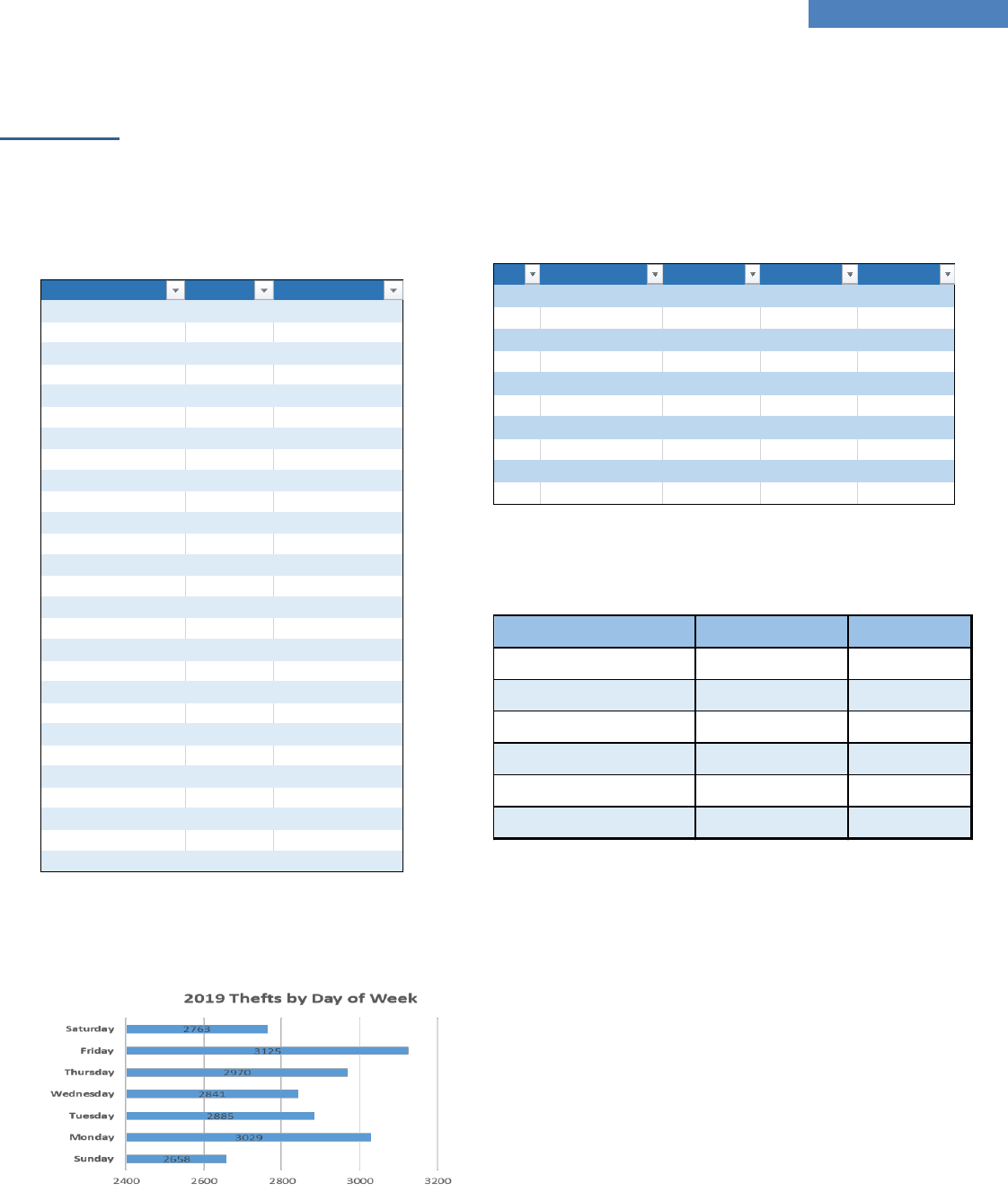
The highest volume of theft days in 2019 was Fridays,
followed by Mondays. Tuesdays and Wednesdays
competed for 3
rd
with approximately 44 thefts
difference.
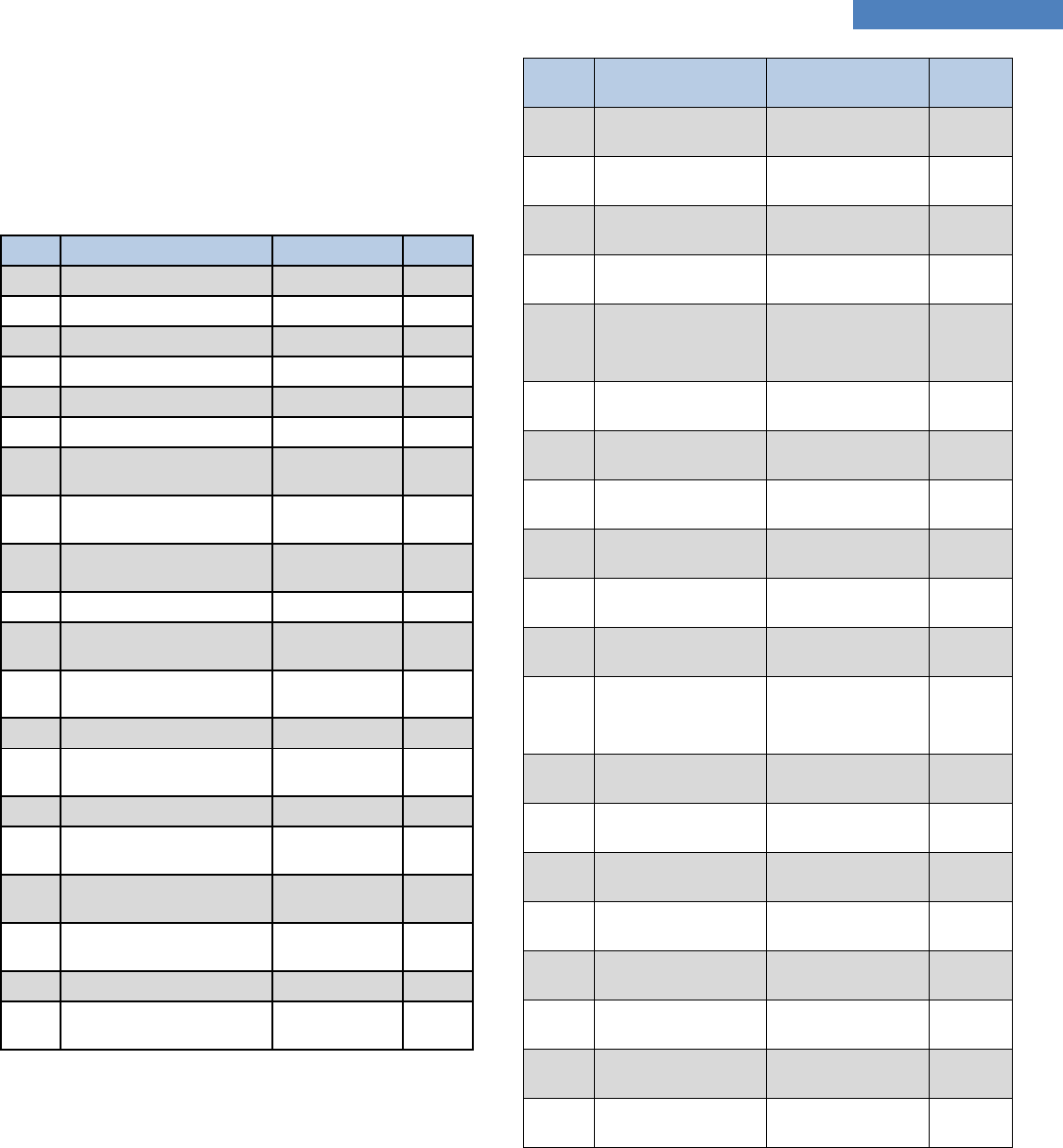
Of the 20,271 vehicles stolen during 2019, 83%
(16,844) of reported stolen vehicles were deemed
“inactive” in 2019. The following is a breakdown of
the reported stolen vehicles by vehicle type.
In 2019 there were 16,844 recovered vehicles where
the vehicle was stolen during 2019. Of these vehicles,
39% of the vehicles were recovered within one week
from the date of theft.
Reporting Agency Theft Weekly Average
Statewide 20,271 390
Denver 5101 98
Colorado Springs 2634 51
Aurora 2182 42
Adams County 818 16
Lakewood 752 14
Pueblo 651 13
Westminster 543 10
Thornton 515 10
Arapahoe County 498 10
El Paso County 376 7
Arvada 355 7
Jefferson County 335 6
Commerce City 319 6
Greeley 308 6
Englewood 273 5
Longmont 264 5
Boulder 253 5
Fort Collins 232 4
Northglenn 202 4
Littleton 195 4
Brighton 178 3
Wheat Ridge 178 3
Grand Junction 158 3
Weld County 140 3
Larimer County 136 3
Douglas County 132 3
Rank Name Active Inactive Count
1 PASSENGER CAR 605 6339 6944
2 SUV 439 4683 5122
3 Pickup Truck 472 3680 4152
4 MOTORCYCLE 732 670 1402
5 Trailer 709 522 1231
6 Van 36 260 296
7 Flatbed 65 39 104
8 Open Body 35 15 50
9 Mult-wheeled Vehicle 33 6 39
10 BUS 2 32 34
Recovery Delay Stolen in 2019 Precentage
Same Day 1473 9%
Same Week 7000 41.55
Same Month 13033 77%
3 Months 223 1%
6 Months 30 0.18%
1 year 0
ATICC 6
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records
are made on a daily basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in
this analysis.
For the 2018 Auto Theft report, we have captured the
top 20 most stolen vehicles by utilizing year, make
and model. In previous year, we just calculated by
make and model. For the 11 of the 20, are a
combination of Honda Civic’s & Accords, the next
type of vehicle is the Ford F-250.
We also ran the number list of most stolen vehicles
based solely on Make & Model. We observed similar
results in 2019 as we observed in 2018, that the
Honda Civic & Accord were the most stolen Make &
Models. These two vehicle models account for 7.9%
of all vehicle thefts in 2019. However, this is a
decrease of 19.1% from 2018.
Rank
Make & Model
Class
Thefts
1
1998 Honda Civic
Small Car
125
2
1997 Honda Accord
Mid-size Car
110
3
1996 Honda Accord
Mid-size Car
107
4
2000 Honda Civic
Small Car
100
5
1997 Honda Civic
Small Car
96
6
1999 Honda Civic
Small Car
91
7
2003 Ford F-250
Full-size
Pickup
79
8
2000 Ford F-250
Full-size
Pickup
76
9
2006 Ford F-250
Full-size
Pickup
76
10
1994 Honda Accord
Mid-size Car
70
11
2004 Ford F-250
Full-size
Pickup
70
12
2005 Chevrolet
Silverado
Full-size
Pickup
69
13
1996 Honda Civic
Small Car
68
14
2003 Chevrolet
Silverado
Full-size
Pickup
68
15
1995 Honda Accord
Mid-size Car
65
16
1999 Ford F-250
Full-size
Pickup
65
17
2005 Ford F0250
Full-size
Pickup
59
18
1999 Chevrolet
Silverado
Full-size
Pickup
57
19
1995 Honda Civic
Small Car
56
20
2001 Ford F-250
Full-size
Pickup
56
Rank
Make & Model
Class
Thefts
1
Honda Civic
Small Car
865
2
Honda Accord
Mid-size Car
754
3
Dodge/RAM Ram
Full-size Pickup
653
4
Ford F-250
Full-size Pickup
648
5
Chevrolet
Silverado
Full-size Pickup
625
6
Ford F-150
Full-size Pickup
448
7
Ford F-350
Full-size Pickup
359
8
GMC Sierra
Full-size Pickup
341
9
Subaru Legacy
Mid-size Car
298
10
Subaru Impreza
Small Car
277
11
Honda CR-V
Mid-Size MPV
273
12
Jeep Grand
Cherokee
Mid-Size SUV
265
13
Toyota Camry
Mid-Size Car
242
14
Jeep Cherokee
Mid-Size SUV
229
15
Toyota Corolla
Small Car
215
16
Chevrolet Tahoe
Full-size SUV
209
17
Toyota 4-Runner
Mid-Size SUV
185
18
Nissan Altima
Small Car
176
19
Ford Explorer
Mid-size SUV
174
20
Subaru Forester
Compact SUV
151
ATICC 7
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records
are made on a daily basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in
this analysis.
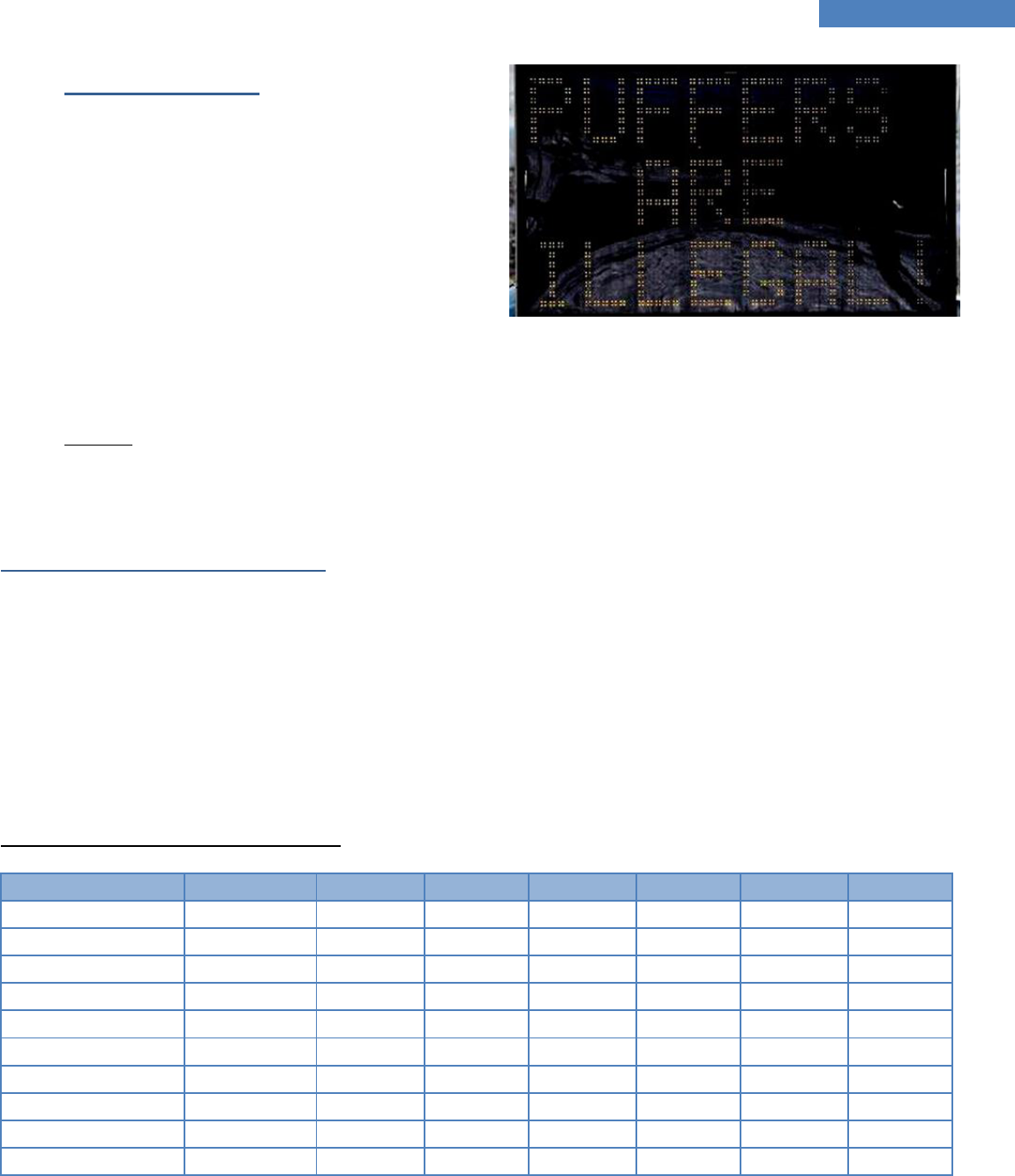
Puffer Vehicles
Puffer data was not obtained this year for the annual
report, based on the lack of standardization in
reporting across the state. To obtain an exact number
is currently inaccurate, based on the many options
that are in the system to choose from, and for the fact
that some of the options that were chosen may not
have been a true puffer. The Stolen Vehicle Database
Repository can not be searched to identify a vehicle
theft where, at the time of theft, the vehicle was
unattended and left running, keys in the ignition, keys
in the car, keys in the ignition and vehicle running,
puffer, etc. Additionally, the numbers that can be
entered into the system will not include victims of
vehicle theft who do not report they left their vehicle
unattended and running. Lastly, the ATICC database
does not require law enforcement reporting of a
puffer event.
Auto Theft Victim Impact
Auto theft is considered a property crime; however, stolen vehicles are often used to commit other crimes. Drug use
connected with auto theft is very common in Colorado. There is a financial impact on the victim as well as potential danger
associated with a recovered stolen vehicle. Victims are encouraged to check their cars for damage, illegal drugs, drug
paraphernalia, and other contraband. The victim should carefully vacuum the vehicle and wipe down the interior surfaces
with a disinfectant. If the vehicle was stolen with the key and they key was not recovered, a new ignition switch should
be installed. Locks on the victim’s home, office, and other buildings should be changed if the thief had access to their
keys. Garage door codes should be changed and enhanced security measures should be taken at home, since the thief
knows where the victim lives.
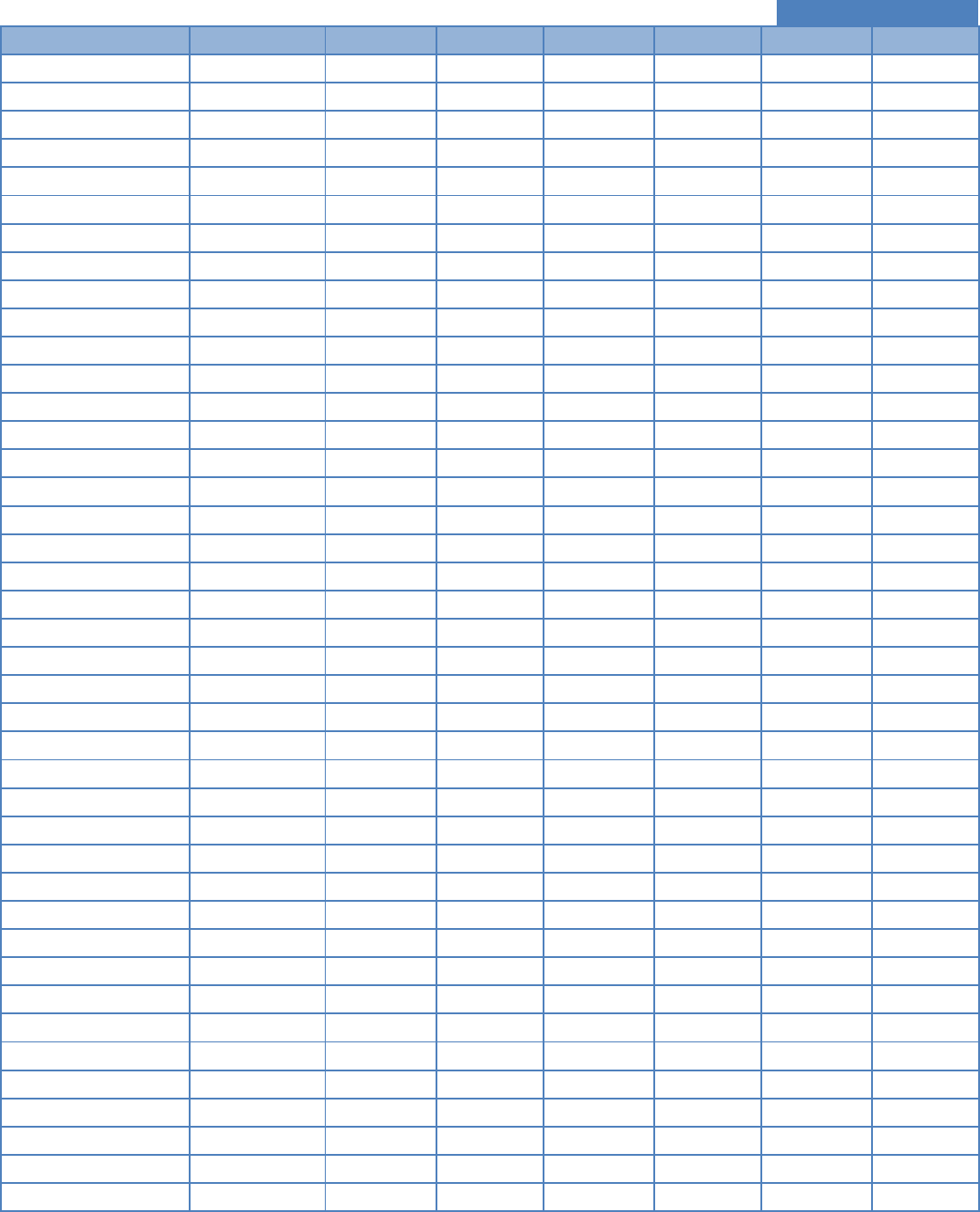
Auto Theft Volume by County
County
CATPA Area
2017 Thefts
% ∆ ’16-‘17
2018 Thefts
% ∆ ’17-‘18
2019 Thefts
% ∆ ’18-‘19
Adams County
Denver Metro
3,039
-31.70%
3,118
2.60%
4,888
56.76%
Alamosa County
South West
34
25.90%
41
20.60%
39
-4.87%
Arapahoe County
Denver Metro
2,843
192.20%
3,009
5.80%
1,180
-60.78%
Archuleta County
South West
11
266.70%
12
9%
25
108%
Baca County
Eastern
1
-
3
200%
2
-33%
Bent County
Eastern
10
11.10%
14
40%
13
-7%
Boulder County
Northern
470
18.10%
667
41.90%
676
1.30%
Broomfield County
Denver Metro
144
10.80%
128
-11.10%
124
-3.12%
Chaffee County
Southern
22
-33.30%
25
13.60%
18
-28.00%
Cheyenne County
Eastern
2
200%
4
100%
0
-100%
ATICC 8
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records are made on a daily
basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in this analysis.
County
CATPA Area
2017 Thefts
% ∆ ’16-‘17
2018 Thefts
% ∆ ’17-‘18
2019 Thefts
% ∆ ’18-‘19
Clear Creek County
Western
21
18.70%
17
-19%
12
-29%
Conejos County
South West
9
80%
15
66.70%
10
-33.33%
Costilla County
South West
12
140%
28
133.30%
19
-32.14%
Crowley County
Eastern
0
-100%
4
400%
6
50%
Custer County
Southern
3
50%
1
-66.70%
5
400.00%
Delta County
South West
43
-15.70%
45
4.70%
50
11.11%
Denver County
Denver Metro
4,700
11.60%
4,733
0.70%
5,114
8.04%
Dolores County
South West
2
-33.30%
3
50%
3
0%
Douglas County
Denver Metro
268
9.80%
378
41%
303
-20%
Eagle County
Western
27
12.50%
31
14.80%
26
-16.12%
El Paso County
Southern
2,249
2.70%
2,869
27.60%
3,115
8.57%
Elbert County
Denver Metro
10
-23.10%
14
40%
17
21%
Fremont County
Southern
62
-6.10%
78
25.80%
85
8.97%
Garfield County
Western
69
6.20%
82
18.80%
60
-26.82%
Gilpin County
Denver Metro
18
20%
13
-27.80%
11
-15.38%
Grand County
Western
17
-22.70%
10
-41.20%
11
10.00%
Gunnison County
South West
20
150%
13
-35%
11
-15%
Hinsdale County
South West
0
-
0
-
0
0%
Huerfano County
Southern
15
-16.70%
10
-33.30%
23
130.00%
Jackson County
Northern
1
-66.70%
1
-
3
200%
Jefferson County
Denver Metro
1,969
7.10%
2,043
3.80%
1,707
-16.44%
Kiowa County
Eastern
4
300%
0
-400%
0
0%
Kit Carson County
Eastern
7
-36.40%
9
28.60%
7
-22.22%
La Plata County
South West
77
20.30%
67
-13%
69
3%
Lake County
Western
5
-37.50%
6
20%
3
-50%
Larimer County
Northern
419
7.40%
367
-12.40%
499
35.96%
Las Animas County
Southern
29
-
23
-20.70%
28
21.73%
Lincoln County
Denver Metro
7
-12.50%
9
28.60%
7
-22.22%
Logan County
Eastern
24
-38.50%
37
54.20%
25
-32.43%
Mesa County
Western
243
7.10%
252
3.70%
255
1.19%
Mineral County
South West
0
-
0
-
1
100%
Moffat County
Western
17
112.50%
7
-58.80%
11
57.14%
Montezuma County
South West
33
37.5
34
3%
28
-18%
Montrose County
South West
121
36%
87
-28.10%
57
-34.48%
Morgan County
Eastern
41
13.90%
59
44%
44
-25%
Otero County
Eastern
37
8.80%
63
70.30%
40
-36.50%
Ouray County
South West
5
25%
2
-60%
4
100%
Park County
Southern
9
-43.80%
11
22.20%
3
-72.72%
Phillips County
Eastern
1
-
4
300%
2
-50%
Pitkin County
Western
13
-13.30%
13
-
8
-38.46
Prowers County
Eastern
9
-10%
13
44.40%
7
46.15%
ATICC 9
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records are made on a daily
basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in this analysis.
County
CATPA Area
2017 Thefts
% ∆ ’16-‘17
2018 Thefts
% ∆ ’17-‘18
2019 Thefts
% ∆ ’18-‘19
Pueblo County
Southern
1,216
-1%
1,065
-12.40%
792
-25.63%
Rio Blanco County
Western
3
200%
5
66.70%
2
-86.66%
Rio Grande County
South West
11
-42.10%
14
27.30%
12
-14.28%
Routt County
Western
10
150%
9
-10%
12
33%
Saguache County
South West
5
-
4
-20%
17
325%
San Juan County
South West
1
100%
0
-100%
3
300%
San Miguel County
South West
2
-
3
50%
1
-67%
Sedgwick County
Eastern
4
400%
4
-
-100
Summit County
Western
20
-25.90%
40
100%
29
-28%
Teller County
Southern
17
13.30%
15
-11.80%
23
53.33%
Washington County
Eastern
4
-
2
-50%
11
4509%
Weld County
Northern
560
-21.50%
705
25.90%
662
-6.09%
Yuma County
Eastern
7
75%
14
100%
16
14%
Total
19,488
8%
21,324
9.40%
20,230
-5.13%
Call to Action
The ATICC along with the CATPA funded Auto Theft Task Forces need to continue working collaboratively to improve
collection and reporting standards of auto theft data. ATICC is also reaching out to all Agency dispatcher/records unit to
give update training on entering data into the ATICC Mask database. A distance learning-type platform is being
discussed with CSP Training Academy personnel.
Appendix A – Stolen Vehicle Data Validation Processes and Reliability
The Stolen Vehicle Database Repository is the best solution we have to compile a review of statewide auto theft data. It
is believed that this data could be significantly more useful with statewide agencies participating to complete the ATICC
Supplemental. The ATICC Supplemental is accessed through the Colorado Crime Information Center and enables the
ability to collect additional data for a motor vehicle theft event. This supplemental reporting includes additional identifiers
related to suspects, modus operandi, victims and the vehicle condition when the vehicle was stolen and when it was
recovered. Lastly, ATICC encourages using CCIC stolen vehicle entries compliant with the data standards as outlined in
the National Crime Information Center (NCIC) /CCIC User’s Manual.
Process 1: Origination of Data
Since January 2010, the CATPA has funded a project for the collection, analysis and dissemination of auto theft incidence
occurring within Colorado. This project funded the ATICC, operated and managed by the Colorado State Patrol. ATICC
was funded to provide reliable, timely, and accurate information/intelligence pertaining to the incidence of auto theft.
ATICC has acquired stolen vehicle records for conducting analysis and study of vehicle thefts reported to the Colorado
Crime Information Center (CCIC). These stolen vehicle records are classified as law enforcement sensitive and are
compliant with the FBI Criminal Justice Information Services Security Policy. ATICC uses the stolen vehicle records, as
entered into CCIC, for administrative, strategic and tactical analytical products. In July 2012, ATICC successfully
implemented an information technology system to database stolen vehicles reported into CCIC. This database, called the
Stolen Vehicle Database Repository (SVDR), affords the ability to capture vehicles that are reported stolen and those that
are cleared, located and/or recovered. This report is exclusive to information obtained from the SVDR.

ATICC 10
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records are made on a daily
basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in this analysis.
Data used in this report is inclusive of vehicles stolen that are reported to the Colorado Crime Information Center with a
date of theft range of January 01, 2019 to December 31, 2019. Stolen vehicles included in this report include vehicles
entered into CCIC as a “stolen vehicle” message. The actual number of auto thefts in Colorado is likely higher than
reported, as some incidences of auto theft may not be reported to law enforcement, law enforcement agencies may not
have entered other stolen vehicles into CCIC due to a stolen vehicle recovery occurring prior to completing the
jurisdiction’s reporting and processing procedures, and other stolen vehicles may have been reported as a carjacking
and/or a felony crime involved stolen vehicle incident. Information contained in the Stolen Vehicle Database Repository
is considered dynamic, as modifications, changes and amendments to the stolen vehicle records are made on a daily basis.
Process 2: CCIC Data Validation
Stolen vehicle records entered into CCIC undergo validation standards established by National Crime Information Center
and CCIC.
Process 3: Data Range
Stolen vehicles were obtained by a query of the SVDR for thefts occurring from January 01, 2019 through December 31,
2019, and this data was pulled on January 14, 2020.
Process 4: Deduplication of the 2019 Dataset
The dataset was reviewed for duplicate records, based on unique record identifier, vehicle identification number, case
number, and license plate number, to ensure a single vehicle theft record is not counted more than one time.
Process 5: Test Records
The 2019 database was examined to identify “test records”, which were not records of actual stolen vehicles, but records
entered as tests in the system. These records were not used in this report.
Process 6: Identification of Removed Vehicles
Records that were removed during the year were not identified as to why the stolen vehicle was inactive from CCIC. ATICC
has identified user errors and misuse of message keys where vehicles are removed from CCIC that may not have been
actually “recovered.” However, ATICC does not have the technological advantage to ensure the appropriate message keys
to validate the purpose of the inactivation, e.g., cancellation, locate or clear (recovery). Briefly stated, removals from the
CCIC database occur from three messages conducted by CCIC authorized users from the Originating Agency who
performed the initial entry. These three CCIC message keys are a “clear”, “locate” and “cancel” of the record. The “clear”
(CV) and “locate” (LV) message is performed when a vehicle has been located and is subsequently removed from the
CCIC/NCIC database. Accordingly, a “clear” is supposed to be performed by the agency that entered the vehicle and then
subsequently recovered it. The “locate” is supposed to be performed when an agency, other than the one who originally
entered the vehicle into CCIC, has located the vehicle. The “cancel” (XV) record is supposed to be performed when an
agency discovers the vehicle was not stolen, yet was originally recorded into CCIC as stolen, and thus needs to be cancelled.
Current data processes/practices within the CCIC system treats the CV, LV and XV message the same, regardless of the
technical definitions. When reviewing the SVDR records for the purpose of removal from CCIC, it was observed that CCIC
Users inappropriately utilize the XV (Cancellation) message key in lieu of the CV (Clear) or LV (Locate). This causes
additional analytical concern as each XV message key had to be examined as to whether or not the vehicle was truly
cancelled or recovered. The process of using a Cancel message key should invoke cases where a previously stolen vehicle
entry was discovered not to have been stolen (e.g., joyriding, mistaken vehicle identity, etc.). However, based on law
enforcement experience of ATICC personnel, the comparative records of “true” XV messages affecting the overall analysis
are minimal. In other words, ATICC believes some of the identified cancellations were a result of stolen vehicles being
recovered. In accordance with NCIC policy and law enforcement practice, an official police report of a stolen vehicle must
be made prior to the CCIC entry. The result of the aforementioned is that ATICC treated the message keys of “inactive,”
“cancel,” “clear,” and “locate” as inactivity in the stolen vehicle database, thus inferring each message key was a recovery.

ATICC 11
(UNCLASSIFIED)
Disclaimer: Information contained in the Stolen Vehicle Database Repository is considered multifarious; modifications to records are made on a daily
basis. Stolen vehicle records were screened for accuracy and normalized for standardization prior to use in this analysis.
Process 7: Identifying Re-Entered Entries
As discussed in last year’s Annual Report, several law enforcement agencies have engaged in a practice to re-enter a stolen
vehicle in CCIC/NCIC in order to maintain an alert on the vehicle in the event the vehicle is checked through the system.
Qualitative screening involved searching the miscellaneous field for key words and notations, and the stolen vehicle case
number indicating re-entry from previous purging.
Process 8: Normalizing the Dataset
The SVDR populates a list of common terminologies to normalize the dataset, including the common name of the reporting
agency, vehicle identifiers based on the vehicle identification number (using VinLink lookup), theft/recovery areas in
accordance with the designated CATPA area map, and county assignments based on the assigned CCIC originating
reporting agency identifier. As part of using the key indexing charts, many fields of the database underwent cleaning and
scrubbing to ensure normalization of key words and terms (e.g., Denver PD vs. Denver vs. Denver City vs. Den vs. Denver
CO vs. Denver, CO vs. Denver, Colorado vs. Denver Colorado, etc.).
Process 9: Cleaning the Dataset with Investigatory Tools
Current CCIC policies mandates for a stolen vehicle file to be accepted into the CCIC database, where limited primary fields
of information are required. These primary fields of information include, but all are not all are necessarily required: the
date of theft, case number, originating agency identifier number, vehicle make, and vehicle identifier (license plate, vehicle
identification number, owner applied number or production number). Unfortunately, for analytical purposes, other key
information is not required for entry by the CCIC authorized user. Examples include the vehicle model and style. To add
further challenges to cleaning the dataset, when key analytical data is entered, it is oftentimes inaccurate due to a lack of
data standardization. For example, when the style of the vehicle is entered, it is oftentimes incorrect as the style field
does not match the vehicle make and model (i.e., pickups may be entered as passenger cars; SUVs as pickups; scooters as
motorcycles, etc.). The most significant value added to the data analysis was information obtained from VinLink®. This
tool provided 47 various identifiers for each vehicle possessing a valid VIN entry in the database.
Process 10: Reliability Note
Based on the above notations, it is obvious the database used to compile this report has limitations and justifies the
direction that ATICC is moving in acquiring completion of the ATICC Supplemental. The ATICC Supplemental provides the
ability to analyze additional information involving the vehicle theft event and its recovery, such as the suspect information,
their location, how a vehicle was stolen (e.g., puffing, forcible entry, etc.), the condition of a vehicle upon recovery, and
any associated crimes involving the particular vehicle theft and its recovery. Unfortunately, the dataset is unable to
provide valid analysis of these identifiers as few agencies used the ATICC Supplemental within the CCIC stolen vehicle file
upon the report of theft and/or the vehicle recovery event.
With regards to the accuracy and reliability of the CCIC data used in this report:
1) There is no other uniform statewide reporting system for auto theft other than CCIC stolen vehicle file,
2) The CCIC entries were not intended to provide a records management system for analysis of auto theft,
3) There is established criteria and validation of entries made into the SVDR that many individual law enforcement
records management systems do not possess (e.g., VinLink, CJIS validation standards, etc.) and
4) It is recommended to keep in mind the actual numbers are likely higher than portrayed, but it is believed this
report provides the best picture of auto theft experienced in Colorado.