
ATS Institute of Technology
www.atsinstitute.edu
School Catalog
Chicago
Fall 2023 Catalog
Including Spring 2024 Addendum
Date Published: 08/29/2023
Updated with Spring 2024 Addendum 1/2/2024
Certified as true and correct in content and policy.
25 East Washington, Suite 200
Chicago, IL 60602
Phone 312-300-0980
Fax 312-277-2500

3
| Page
FOREWORD
WELCOME TO OUR SCHOOL!
You have taken the first big step in building a bright future for yourself.
ATS Institute of Technology wants to be the school that helps you achieve your professional goals. Our school understands the needs
of mature students, and we are sensitive to the obligations you have at home or work. To help you fit classes into your already busy
life, we have designed a convenient schedule of classes. We are always open to suggestions and available to answer your questions.
Our system of professional education is proven by many generations of graduates to achieve the highest levels of learning. Our
teaching methods provide for a dynamic exchange of information among faculty members and administrators, ensuring ongoing
enrichment of the curriculum.
We offer to our students’ specific knowledge and critical professional skills desired by today’s employers. Our educational program
is routinely updated to reflect the rapidly changing information and current and future needs of the job market.

4
| Page
Table of Contents
General Information ............................................................................................................. 1
About ATS ............................................................................................................................ 1
Mission 1
Accreditation, Approvals and Authorizations 1
The Facility and Instructional Equipment 2
Hours of Operation 2
Admissions Policies ............................................................................................................... 2
Admission and Registration 2
Americans with Disabilities Act 4
Equal Opportunity Statement 4
Readmission Policy 4
Academic Policies and Procedures ......................................................................................... 5
Transferability of credits, advanced placement and experiential learning 5
Course Grading and Quality Points 5
Program Progression Policy 6
Graduation Requirements 6
Comprehensive Exit Examination 6
NCLEX-PN Exam Eligibility 7
Repeating Courses 7
Cause for Academic Dismissal 7
Academic Definitions 7
Add/Drop Period 8
Attendance Policy 8
Academic Monitoring Program 9
Withdrawal 9
Leave of Absence 11
Return from Leave Policy 11
Student Services .................................................................................................................. 11
Honors and Awards ............................................................................................................. 13
Student Policies ................................................................................................................... 13

5
| Page
Discipline Policy 14
Statement of Liability 17
Computer and Internet Use Policies 17
Student Identification 19
Identity Verification and Privacy Protection 19
Professional Dress Code 19
Administrative Policies ........................................................................................................ 20
Student Grievance and Appeal Procedure 20
Annual Security Report / Clery Act / Campus Security 20
Emergency Preparedness 20
CDC Universal Precautions to Decrease Transmission of Disease 20
Violation or Suspected Violations of Federal Copyright Law 21
Academic Freedom 21
Academic Honesty and Integrity 21
Title IX Compliance 22
Privacy of Student Records 22
Directory Information 23
Drugs and Alcohol Abuse Prevention Policy 23
Program Costs & Financial Aid ........................................................................................... 24
Definitions related to Federal Financial Aid 24
Standards of Satisfactory Academic Progress (SAP) 25
Student Financial Aid Sources 27
Veteran Student Benefits 28
Scholarships 28
Financial Procedures and Policies 29
Return of Title IV Funds (R2T4) 31
Practical Nursing Program .................................................................................................. 34
Practical Nursing Program Information 34
Appendix A: Academic Calendar Fall 2023 – Fall 2024 ....................................................... 39
Appendix B: Faculty and Administration ............................................................................. 42
Appendix C: Tuition and Fees ............................................................................................. 44
Appendix D: TEAS Policy................................................................................................... 46
Appendix E: Readmission - No Exit Appeal Policy ............................................................... 47

6
| Page
Appendix F: Documentation for Clinical ............................................................................. 48
Appendix G: Exit Examination Score Determination ........................................................... 51
Appendix H: Local and National Community Resources ...................................................... 52
Appendix I: Institutional Disclosures Report ....................................................................... 53
Appendix J: Minimum Computer System Requirements Policy ............................................. 56
Appendix K: Standardized Testing Progression Policy .......................................................... 57
Appendix M: Entrance Exam and Placement:...................................................................... 58
Entrance Exam 58
Course Placement 58
Appendix N: Readmission Guidelines .................................................................................. 59
Appendix O: Repeating Course Guidelines........................................................................... 60
Appendix P: Indiana Resident Refund Policy ....................................................................... 61
Appendix Q: Civility Code of Conduct .................................................................................. 62
Appendix R: ATS Exam Guidelines ..................................................................................... 64
Appendix S: ATS Clinical Expectations ............................................................................... 65
Spring 2024 Addendum Pages 67 – 83
Updated Policies:
• Acceptance of Credits on Transfer
• Course Grading and Quality Points
• Program Progression Policy
• Nursing Clinical Attendance
• Make-up Policy
• Extenuating Circumstances
• Academic Monitoring
• Violation of the Code of Conducts
• Computer and Internet Use Policies
• Professional Dress Code
• Payment Options
• Financial Procedures and Policies
• ATS Clinical Expectations
• Return from Leave Policy
• Corrective Action, Behavioral Violations, and 3-step Violations Write-up updated to Student
Corrective Action and Disciplinary Policy
• Appendix C: Tuition and Fees
• Appendix L: Academic Monitoring Guidelines – NEW
• Institutional Disclosures Report

7
| Page

1
| Page
General Information
The primary role of ATS Institute of Technology as an academic
institution is to deliver exceptional education and service to its
students. A consistent focus on delivery of quality education
supports the mission and requires the School to plan ahead but also
respond to current market demands. Current student
demographics represent diverse ethnic and racial backgrounds.
Students who enter school are from recent high school graduates
to at an older age or changing their careers. Experienced nurse
educators as well as recent clinical professionals represent the
faculty at the School. The educational experience at the School
values and reflects the diverse student population. The School has
strived to gain a reputable name in the local communities and to
continue its excellence.
ATS policies have been formulated in the best interests of students
and the School. The School reserves the right to implement
changes to policies. However, changes to policies for program
completion will apply to students in the incoming cohort. When a
change is made to a policy that affects students, they will be
notified by ATS email with a link to the newly published Catalog
and/or Addendum.
Ownership
ATS, owned and operated by MDT School of Health Sciences, Inc
(MDT), Yelena Bykov (CEO) and Leonard Bykov (President).
MDT is a privately held corporation that provides career
education.
About ATS
Historically ATS Institute of Technology was founded as a
computer school in 1997. The first Practical Nursing class was
enrolled in 2006 in Ohio and then the Chicago location opened in
2011 for the Practical Nursing program. The school is
incorporated in the State of Ohio and registered in the State of
Illinois. ATS is an academic nursing institution with professional
faculty, administrative expertise, modern equipment, current
materials and teaching methods, and a metropolitan campus
environment which provides the foundation for learning
experience. The Practical Nursing Program stresses practical
application and provides hands-on experience necessary for the
students to succeed in a professional career. Day and evening
classes are offered to accommodate the challenging and complex
lives of students.
Mission
The mission of the school is to create and provide a high-quality
educational experience to each individual student seeking to
establish a successful career. The School is committed to offering
health care programs designed to satisfy local and regional
demands and equip students with a wide range of academic
knowledge.
Vision and Goals
Through innovation, the school will be the school that people
choose for exceptional education and exemplary graduates’
performance.
Core Values
To pursue our vision within an education environment that
promotes integrity, respect, fairness, quality performance,
accountability, and dedication to education.
The educational experience at the school is aimed at the full
development of the potential each student brings to school.
Administrative expertise, a professional faculty, modern
equipment, current materials and teaching methods, and an
environment designed for learning contribute to the achievement
of our mission. Our program stresses practical application and
provides hands-on experience necessary for the students to
succeed in their professional career.
Strategic Initiatives and Goals
In its five-year strategic plan, the school defined the following
goals:
1) Education Quality
a) Graduate exceptional nurses who will serve global
health care communities.
b) Strengthen and develop organizational quality that
promote an excellent learning environment.
c) Monitor student success from admission to graduation
through teaching, advisement, and mentoring.
d) Provide ongoing and systematic program evaluation
focusing on student performance and achievement of
program learning outcomes.
2) Dedicated Faculty and Staff
a) Create a school-wide culture that embraces high faculty
satisfaction and loyalty to the School.
b) Strengthen the faculty development program and
mentoring new faculty.
c) Exceptional Service
d) Create a school-wide culture of exceptional student-
centered needs services.
e) Facilitate interaction between faculty and students.
f) Offer advanced computing facilities with updated
software and internet access.
g) Develop continuous improvement strategies with
measurable outcomes
3) Growth
a) Strengthen and build relations with community and
health care providers in the Chicago area that will
advance the mission of the School.
b) Develop strong mutually supportive and beneficial
relations with clinical affiliates.
Accreditation, Approvals and Authorizations
Accreditation
Institutionally Accredited by the Accrediting Bureau of Health
Education Schools (ABHES). 7777 Leesburg Pike, Suite 314N,
Falls Church, VA 22043, (703) 917-9503
Approvals
● Approved by the U.S. Department of Education (for Title IV
Federal Aid Programs) https://studentaid.gov/help-
center/contact

2
| Page
● Approved by the Private Business and Vocational Schools
Division of the Illinois State Board of Higher Education. 1
North Old State Capitol Plaza, Suite 333, Springfield, Illinois
62701-1377
Program Approvals
The Practical Nursing Program is approved by the Illinois Board
of Nursing. James R. Thompson Center, 100 West Randolph
Street, Suite 9-300, Chicago, Illinois 60601
The Facility and Instructional Equipment
The School offers a professional atmosphere that is conducive to
learning. The school operates in Chicago, IL. All clinicals are
offered at sites located in the Greater Chicago area. Students who
reside in Indiana will need to commute to their assigned site in
Illinois. No exceptions will be made.
Our facilities are equipped with spacious classrooms, computer
labs, nursing tech labs, tutoring centers, administrative offices, and
a student lounge. Our equipment is well maintained and constantly
updated to reflect current standards. The onsite administrator
handles day-to-day issues and overseas students' services.
Faculty and students have access to various electronic data systems
for retrieval of reference material from medical, nursing, and
science sources via computer.
Hours of Operation
School Main Office Hours: Monday – Friday 8am – 5pm
Class Time
Day Track Hours: Monday – Friday: 8:00am – 5:00pm
Evening Track Hours: Monday – Friday 4pm – 10pm &
Saturdays/Sundays 8am – 5pm
Students may be assigned day or evening clinical/lab rotations
during the week or weekend, regardless of Day or Evening track.
Clinical hours may vary depending on the course and availability
of clinical sites and may be at any time from 6:30 am – 12:00
(Midnight). This includes weekdays and weekends, regardless of
Day or Evening track.
Admissions Policies
Admission and Registration
General Information for Entrance
The School encourages applicants to schedule an entrance exam
with the admissions department. The entrance exam establishes
the level of education needed by the individual to successfully start
the program.
Only those applicants who have an informed interest in a program
of study and who are dedicated to finding employment in the
related field upon completion of the program should consider
registering for a program. It is the responsibility of the applicant
to ensure that work schedules or other commitments do not conflict
with the student class/clinical hours. Students must be able to
commute to the assigned clinical sites within Greater Chicago
areas.
Admission Requirements
1) Achievement of the minimum required score on the entrance
exam
2) Possess a diploma from an accredited high school or its
equivalent.
3) Valid State issued ID - for IL or IN
4) A cleared record with the Health Care Worker Registry in
Illinois or Indiana State Nurse Aide Registry. Any student
whose record displays administrative findings of abuse,
neglect, or misappropriations of property must present
documentation from current employer or state waiver.
(Waivers will be handled on a case-by-case basis.)
ATS Institute of Technology reserves the right to deny admission
previously accepted if any of the items listed above are not
successfully completed or found to be falsely represented.
Students are required to attend a mandatory orientation session.
Students receive an Enrollment Agreement after attending the
orientation session.
All prospective students are highly encouraged to review the
School Catalog prior to signing an Enrollment Agreement.
Once the applicant has received the Enrollment agreement, the
applicant must:
1) Sign the enrollment agreement and other required
documentation.
2) Complete Background check and drug testing within 7 days
of the start of the semester.
3) Complete documentation for clinical experience based on
your program plan. (See “Appendix F: Documentation for
Clinical”
High School Requirements
Applicants must possess a high school diploma or its equivalent.
All applicants must provide evidence of a high school diploma or
its equivalent to the School prior to the commencement of the first
day of the student’s scheduled start date. Evidence of high school
graduation or its equivalent must include the applicant’s name and
graduation date as well as the name and location of the high school
attended including, city, state, and graduation year. The School
will verify that the high school or program was approved by the
applicable governing or state authority, if approval is required by
applicable law.
High school documentation from a country other than the United
States must be translated and certified to be at least the equivalent
of a U.S. high school diploma by an agency that is a member of the
National Association of Credential Evaluation Services (NACES)
or Association of International Credential Evaluators (AICE).
Please note that some agencies have more specific requirements
and accept only original documentation sent directly from the
educational institution.

3
| Page
The equivalent to a high school diploma includes GED®,
HiSET™, TASC™, or other approved high school equivalency
certificate.
An applicant who graduated from high school in a homeschool
setting must provide documentation signed by the applicant’s
parent or guardian that lists the secondary school courses
completed by the applicant and that certifies the successful
completion of secondary school education in a home school
setting. Such documentation must include all information that ATS
requires, in addition to the parent or guardian’s signed attestation
that the homeschool was approved by the applicable governing or
state authority if approval is required by applicable law. If the state
where the applicant was homeschooled requires by law that
homeschooled students obtain a secondary school completion
credential (other than a high school diploma or its recognized
equivalent), the applicant must submit a copy of that credential.
Students who do not possess a high school diploma or its
equivalent may not apply for admission. Should we be unable to
verify a student’s education or determine that the student’s
education does not meet the requirements, the student’s enrollment
will be canceled. Any paid tuition will be returned to the student.
Determining Student’s Physical Location
During the enrollment process, students complete the Enrollment
Agreement. The Enrollment agreement contains the students'
physical address. Student’s physical location will be determined at
the time of enrollment through two methods: 1) address on the
Enrollment Agreement, and 2) a copy of a government issued
identification card. Students are required to notify the School if
they have a change in physical address while enrolled at the
School.
The Minimum Technical Requirements
Disclosure
Distance delivery coursework at ATS will require minimum
technical resources in order for students to participate and
complete assignments virtually through various online
technologies. See Appendix J: Minimum Computer System
Requirements Policy.
Entrance Exam and Course Placement
Prospective students are required to pass the entrance exam with
the required score determined by the school faculty and
administration to proceed with the admissions process. Students
will be placed in courses based on the entrance exam results. See
Appendix M: Entrance Exam and Course Placement.
Background Checks and Convictions
A background check must be submitted within the first 7 days in a
student’s first semester of enrollment. Failure to submit the
background check within the first 7 days, will cancel a student’s
enrollment.
ATS may cancel or terminate a student’s enrollment if the student
meets any one or more of the following criteria:
1) The individual has been convicted of or pleaded guilty to any
crime identified as a considering factor in determining a
Refusal to Issue a Nurse License Based on Criminal History
Record of the Nurse Practice Act in the Illinois
Administrative Code.
2) The individual has been convicted of a crime that involved
any of the following noted below:
a. Required to register under the Sex Offender
Registration Act.
b. Involved in involuntary sexual servitude of a minor.
c. Involved in misdemeanor criminal battery against any
patient in the course of patient care or treatment.
The Admissions Department designated staff will contact students
with positive background check results. Depending upon the
severity or type of incident, students will be advised that clinical
agencies have the right to deny students clinical placement.
Please see the following link for the IL State Board of Nursing
application in regards to licensure and criminal convictions. Click
on the Applicants FAQs dropdown for a PDF with more
information: https://idfpr.illinois.gov/About/FAQ.asp
Students are required to report any crimes committed while
enrolled in the Practical Nursing program at the School. In the
event of known noncompliance to this request, students may be
immediately dismissed from the program.
Any misrepresentation or omission of facts requested on the
application (including disclosure of convictions) is cause for
disqualification of the application process or for dismissal from
ATS Institute of Technology, if enrolled.
Drug Testing
A standardized drug screen must be submitted within the first 7
days in a student’s first semester of enrollment. Failure to submit
the drug screen within the first 7 days, will cancel a student’s
enrollment. See Drug Testing Policy.
Medical Compliance
Students are required to have up to date medical records and CPR
in accordance with the requirements below. Students are
responsible for keeping all immunizations, PPD testing, physical
exam, medical insurance, and CPR current. Students must update
any medical document with an expiration date to ensure that they
are current and on file in the Nursing Department Office for
students to be placed in the clinical setting.
Students beginning in the developmental semester must have all
medical documentation completed and accepted by week 12 of the
developmental semester. Students who do not meet the medical
compliance requirements by the stated deadline, will not be
enrolled in the Fundamentals course in the following semester.
Students beginning in the nursing semester must have all medical
documentation completed and accepted by the end of the second
week of the semester of acceptance. Students who do not meet the
medical compliance requirements by the stated deadline will be
unenrolled from the Fundamentals course. See Appendix F:
Documentation for Clinical.

4
| Page
Americans with Disabilities Act
ATS Institute of Technology complies with Section 504 of the
Rehabilitation Act of 1973 and the Americans with Disabilities
Act of 1990 and does not discriminate on the basis of disability.
Inquiries or concerns regarding this policy or assistance with
accommodation requests can be brought to the attention of the
Director of Nursing/ Title IX Coordinator: p: 312-300-0980; e-
mail: lfalbo@atsinstitute.edu. A copy of this policy can also be
found at www.atsinstitute.edu.
Students Seeking Reasonable Accommodations
In accordance with Section 504 of the Rehabilitation Act and the
Americans with Disabilities Act (ADA) as amended, the School
abides by the regulation that “no otherwise handicapped
individual” shall be excluded from participation in the programs
and services offered by the School “solely by reason of the
handicap.” A student is eligible for consideration for
accommodations and/or auxiliary aids and services if the student
has a disability and the Director of Nursing has met with the
student and determined that the functional limitations of the
disability require such accommodation, auxiliary aids and/or
services.
A student with a disability who cannot wear a mask, or cannot
safely wear a mask, because of a disability as defined by the
Americans with Disabilities may request accommodations to the
masking requirements.
A student with a disability who requires some modification in the
student educational program must do the following:
1) Students should submit written requests with supporting
documentation at least four weeks prior to the beginning of
the first day of classes or as soon as practical.
2) Provide appropriate documentation of the disability to the
Director of Nursing.
3) Meet with the Nursing Programs Administrator to review the
request and appropriate/reasonable accommodations.
4) Agree to appropriate accommodations as it will be written in
the Letter of Accommodation(s).
5) The Nursing Programs Administrator will inform faculty
and staff about accommodations to be made for the student.
The accommodations may be affected by the timeliness of the
student request and the nature of the accommodation requests.
ADA does not require institutions to provide accommodations that
result in an undue burden or fundamentally alter the nature of the
course or relevant academic program. To request reasonable
accommodation, please contact the Director of Nursing at 312-
300-0980 or [email protected]
Equal Opportunity Statement
ATS Institute of Technology is an educational institution that is
committed to supporting the diversity of its employees and
students. ATS is dedicated to a policy of equal opportunity and
nondiscrimination based on gender, age, race, national origin,
sexual orientation, gender identity or expression, veteran status,
political affiliation or belief, religion, disability, or any other
characteristic protected by state, local, or federal law, in an
educational program and activities, admission of students and
conditions of employment. Prohibited sex discrimination covers
sexual harassment and sexual violence.
Admissions Deferment
During the first two weeks of a semester, new students may request
to defer their admission to the following semester. The student
must attend the following semester to be considered "deferred". If
the student does not attend the following semester, their status will
be changed to "canceled" and they are responsible for the
cancellation policy.
Cancellation
New students who cancel their enrollment during the first two
weeks of the semester will have a "canceled" status. The student is
required to submit a new admission application to attend a future
semester and is obligated to any non-refundable 3
rd
party service
fees used through ATS institute.
Readmission Policy
A former student may apply for readmission to his or her program
of study. Generally, a student will not be considered for
readmission more than one time unless there are exceptional
extenuating circumstances, such as military deployment. The
applicant for readmission must satisfactorily demonstrate that the
barriers that prevented the student from successfully completing
his or her program during the previous enrollment have been
resolved, and that there is a reasonable probability that he or she
can complete the program of study within the maximum time
frame.
The readmission process takes approximately 30 days to complete
as the applicant is required to submit an application, Enrollment
Appeal, complete standardized and skills testing (as applicable),
complete all current admissions requirements (including
background check, drug testing, and medical compliance), and to
meet with the Enrollment Appeals Committee. The decision by the
Enrollment Appeals Committee is final.
Students will be readmitted subject to meeting the policies and
program requirements as outlined in the Student catalog in effect
for the cohort they will be placed in. A new enrollment agreement
must be signed prior to the beginning of the semester.
A former student who is subject to any of the following is not
eligible to apply for Readmission:
● Students who were dismissed for violating the Academic
Dishonesty Policy and/or the Code of Conduct.
● Students not in good standing with school financial
obligations.
● Students dismissed for academic performance.
Detailed steps to apply for readmission See Appendix P:
Readmission Guidelines.
Program Completion / No Exit Exam
Students who completed the program and were dismissed because
they did not take/pass the exit exam in the prescribed time must
follow the Readmission-No Exit policy. See Readmission - No Exit
Policy.
5
| Page
Important: Students who are readmitting under this policy refer
to Comprehensive Exit Examination for the number of
opportunities to take the ATI Comprehensive Predictor.
Academic Policies and Procedures
Transferability of credits, advanced
placement and experiential learning
Acceptance of Credits on Transfer
ATS Institute of Technology may grant credits earned for previous
education courses from institutions located in the United States or
its territories. Transfer of credits from other institutions accredited
by an agency recognized by the U.S. Education Department (ED)
or the Council for Higher Education Accreditation (CHEA),
including military training.
Students must provide official, sealed (unopened) copies of School
transcript(s) for all transferable credits two weeks prior to the
beginning of the first semester. In addition, students must provide
the catalog description of the courses requested for transfer.
The Admissions Department processes transfer credits using the
following guidelines. Course/credits must be compatible with the
course/credits equivalent at ATS. To satisfy the competency,
courses requested for transfer must satisfy the following:
● Anatomy & Physiology with Medical Terminology will be
considered for transfer if completed with a grade representing
80% on the transcript grade scale or higher within the last 5
years. Syllabi must be provided for review. If the course did
not include Medical Terminology, the student will be
required to pass Medical Terminology coursework assigned
by ATS.
● English, Math, and nursing courses are not accepted for
transfer.
The student will be informed if the transfer is approved within one
week after documentation has been submitted to ATS.
Credits from another institution accepted by ATS shall be counted
as both credits attempted and completed for calculation of pace and
maximum time frame. Grades associated with these credits are not
included in calculating cumulative grade point average.
Advanced Placement and Experiential Learning
ATS does not accept advanced placement or credit for experiential
learning or life experience. Credit for experiential learning or life
experience will only be considered for acceptance as part of the
academic evaluation for veteran students.
Transferability of Credits and Credentials Earned
at Our Institution
The transferability of credits you earn at ATS Institute of
Technology is at the complete discretion of an institution to which
you may seek to transfer. Acceptance of the certificate of
completion you earn for completing your program is also at the
complete discretion of the institution you may seek to transfer.
If the credits or credential that you earn at this institution are not
accepted at the institution to which you seek to transfer, you may
be required to repeat some or all your coursework at that
institution. For this reason, you should make certain that your
attendance at this institution will meet your educational goals.
This may include contacting an institution to which you may seek
to transfer after attending ATS Institute of Technology to
determine if your credits, clock hours, or diploma will transfer.
ATS Institute of Technology has not entered into any articulation
or transfer agreements with any School or university.
Course Grading and Quality Points
Grades are earned and awarded in each course and are recorded on
the student’s permanent record at the end of each academic term.
Evaluation of student achievement will be made in relation to the
attainment of the specific objectives (outcomes) of the course. At
the beginning of a course the instructor will explain these
objectives (outcomes) and the basis upon which grades are
determined.
There is no rounding up or rounding down of any course grade.
Grades are assigned in accordance with the following scale:
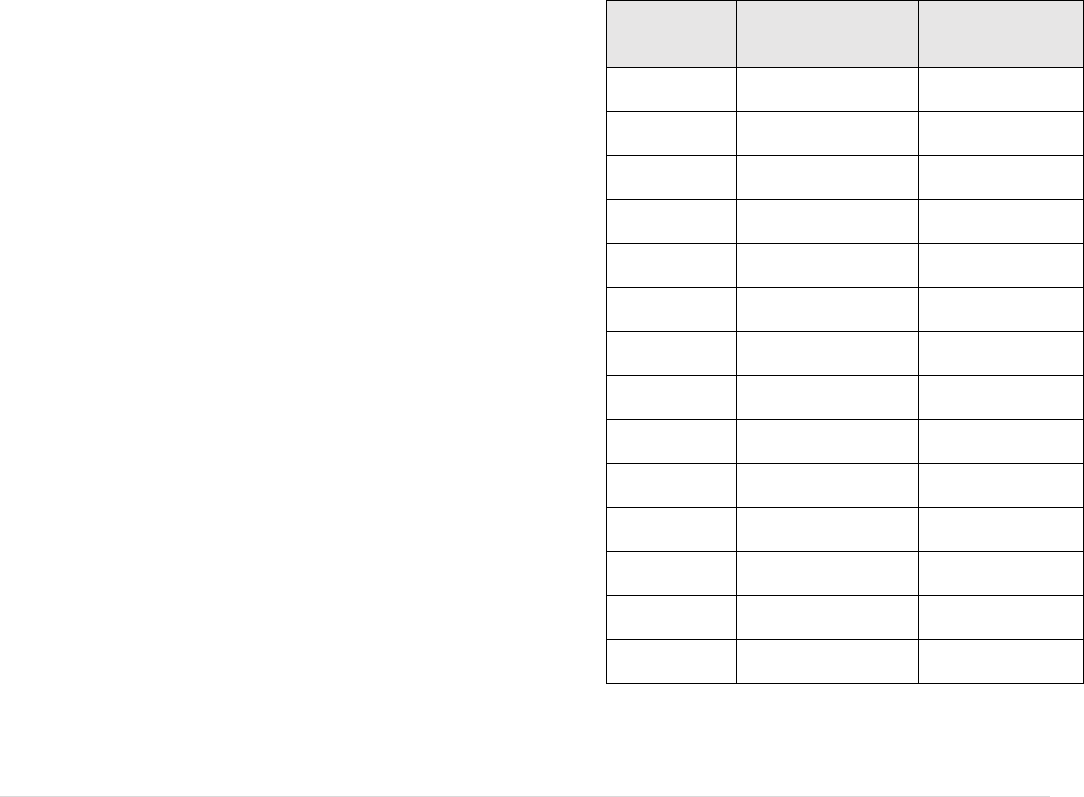
Grades
Numerical
Equivalent
Quality
Points
A
98-100%
4.0
A-
95-97.99%
3.7
B+
92-94.99%
3.3
B
88-91.99%
3.0
B-
85-87.99%
2.7
C+
82-84.99%
2.3
C
78-81.99%
2.0
D
69-77.99%
1.0 - not pass
F
Below 69%
0.0
I
Incomplete
0.0
P
Pass
0.0
W
Withdraw
0.0
WF
Withdraw Fail
0.0
NG
No Grade
0.0
I - Incomplete
Only students who experience unforeseeable emergencies and
have supporting documents and are in good class standing at the

6
| Page
end of the semester may qualify for receiving an “I” grade. A
student receiving a grade of “I” needs to correct any deficiencies
no later than the start of the following semester. An incomplete
grade not corrected within the prescribed period will result in an
“F” for the class, requiring the student to repeat the course.
W - Withdraw
A student will receive a “W” if he or she withdraws by the end of
the published withdrawal date regardless of the student’s academic
status in the course at the time of the withdrawal. Courses, which
are marked with a “W,” are not included in calculation of the GPA.
WF - Withdraw Fail
This grade is equal to the “F” and is calculated for GPA.
Cause for WF Grade.
1) Referral from instructor due to non-engagement.
2) Any withdrawal after the published withdrawal date.
3) Faculty withdrew a student due to inability to pass the course
mathematically.
4) The clinical or lab component of the course failed before
completion of the semester.
NG - No Grade
This grade indicates a non-punitive grade and is assigned at the
discretion of the registrar for a course(s) in which the student has
completed a major portion of the course and is in a good academic
standing but has been unable to complete course requirements
under extenuating circumstances. A grade of NG has a maximum
of one semester. Failure to complete course requirements will
revert to a grade of “F”. SAP will be recalculated at the time of the
grade change.
Program Progression Policy
To progress, the student must achieve the following:
● Students must receive a 78% or higher in both testing and
non-testing scores to successfully pass the course. Therefore,
if the overall grade is passing, but either testing or non-testing
is not at 78%, the student grade will be recorded as a “D”.
Failure of any component associated with the course such as
lab or clinical experience will result in the student receiving
an “F” and failing the whole course.
● Students in Math and Nursing Seminar courses must receive
an 80% or higher in both testing and non-testing scores to
successfully pass the course.
● Students in a Pass/Fail course must complete the
requirements determined within the course syllabi to
successfully pass the course.
● Clinical evaluations will reflect individual strengths and
needs of the students. A main consideration is safe nursing
practice. Carelessness, unsafe practice, and unprofessional
behavior, and no call/no show attendance may constitute a
failure at any time during the clinical rotation resulting in the
failure of the course.
● Meet the Standardized Testing Progression. Students that
score below an indicated proficiency level on Standardized
Testing are subject to the Standardized Testing Progression
Policy. See Appendix F: Standardized Testing Progression
Policy.
● For students who require developmental coursework: In
order to be placed in nursing classes, students must
successfully complete all developmental coursework, achieve
a 1250 score on Lexile level reading, complete the practice
assessment with required remediation, and pass the TEAS test
with the required benchmark. See Appendix D: TEAS Policy
Note: If a student fails a course and/or fails Standardized Testing
Progression, they have failed to progress and must now meet the
policies and program requirements as outlined in the student
catalog in effect for the cohort they will be placed in.
Any student that fails a course will be placed on Academic Warning
or Academic Probation and will receive a letter of their status by
email which will detail the Academic Warning/Probation
requirements.
All requests and appeals must be accompanied by supporting
documentation that explains the circumstances which affected their
academic performance, and how the circumstance has been
resolved so it will not have any future effect on the student’s
Academic Progress. See Appendix: O Repeat Courses Guidelines
Graduation Requirements
To qualify for graduation, students must meet the course and credit
requirements specified for their curriculum: students must have at
least a 2.0 cumulative grade point average and pass a
comprehensive exit examination. Students must fulfill all of their
ATS financial obligations.
Comprehensive Exit Examination
The ATI Comprehensive Predictor is a standardized test that
assesses the student’s preparedness for the NCLEX PN national
examination. The ATI Comprehensive Predictor examination is
administered to all students who have successfully completed all
curriculum courses. Students must reach the established
benchmark to satisfy exit requirements. The benchmark must be
met no more than one semester after successful completion of the
Seminar course. The college reserves the right to change the
provider and students will be notified in writing of the change at
the beginning of the semester that the change occurs. See Appendix
G: Exit Examination Score Determination for benchmark.
If the student does not successfully meet the required benchmark
on the first attempt, the student is expected to follow and complete
an individualized plan set forth by the faculty for any additional
attempts to meet the benchmark.
While there are no guaranteed number of attempts allowed,
students will not be allowed more than 2 attempts in a semester.
There are a maximum of 3 exit examination attempts. This
includes any previous attempts in previous semesters including
previous enrollments.
The following instances will be cause for dismissal from the
program:
1) If the student fails to follow the individualized plan as
prescribed by the faculty and/or nursing coach
2) If the student fails to meet the benchmark after two attempts.
3) If the ATI Comprehensive Predictor benchmark score is not
met by the semester following successful completion of the
Seminar course.

7
| Page
Students that do not take the assessments authentically will follow
the Academic Dishonesty Policy for disciplinary action.
If the student is dismissed from the program, they may reapply
under the Readmission Policy – No Exit. In this case, the student
will have only one opportunity to take and pass the ATI
Comprehensive Predictor.
NCLEX-PN Exam Eligibility
Students will be eligible to apply for the NCLEX-PN examination
after successful completion of the following: graduation
requirements and recommendation by the Nursing Programs
Administrator.
Final Step for board of nursing application signature
A student must submit a completed “End of Program Checklist”
within one semester from completion of the last nursing course.
If a student submits a completed End of Program Checklist after
the deadline mentioned above, the student must:
1) Show evidence of having taken a formal NCLEX-PN
preparation class within the last four weeks prior to checklist
submission.
2) Take and pass a standardized NCLEX-PN test chosen by
ATS.
3) Then the Application to the board can be signed.
ATS offers placement assistance, but cannot, in any way guarantee
employment after the student has successfully completed the
program of study because of training received.
Repeating Courses
A student may repeat a course only once to change a failing grade
to a passing grade. A student may repeat up to two failed nursing
courses over the course of the program. Students must repeat
Nursing Seminar concurrently when the student repeats any failed
last semester course. Students must repeat Critical Thinking
concurrently when the student repeats the Nursing Care of the
Adult 1 course. Any time a student repeats a course, the last
attempt is the grade that will count for progression. However, all
attempts of the course will count toward the cumulative GPA
calculations. A student repeating a clinical nursing course must
repeat the theory, clinical, and laboratory components of the
course.
A student who failed any developmental courses during the first
semester may repeat each developmental course once.
Developmental courses cannot be taken for more than one
academic year (three semesters) and/or 30 financial aid credits.
Registration to repeat courses is not automatic, See Appendix: O
Repeat Courses Guidelines
(See SAP policy to see how repeated classes affect Standards of
Satisfactory Academic Progress.)
Cause for Academic Dismissal
1. Failure of the same course or its equivalent twice
2. Three or more failed Nursing and/or Biology courses,
including courses taken in previous enrollment.
3. Failure to progress per Standardized Testing Progression.
4. Failure to meet the Comprehensive Exit Examination
Requirements. See the Comprehensive Exit Examination
Policy.
Cause for Disciplinary Dismissal
See Discipline Policy.
Academic Definitions
Semester Credit Hour Definition
Coursework is measured in terms of semester credit hours. 1
semester credit hour equals one of the following:
● 15 contact hours of lecture
● 30 contact hours of labs/seminars
● 45 contact hours of clinical time
Recognized Outside Clock Hours
Outside preparation is in addition to regular classroom activities
and is required to complete the course. The type of outside
preparation will vary by course and may take the form of
homework assignments, projects, reading, and required research.
The amount of time spent for outside preparation will vary
according to individual student abilities and complexity of the
assignments. Students are responsible for reading all study
materials issued by their instructors and must turn in homework
assignments at the designated time. Students can responsibly
expect to spend 7.5 hours of outside preparation for every semester
credit of lecture and lab scheduled in a course. Outside preparation
hours for each course can be found on the respective course syllabi.
Course Numbering Definitions
Courses are numbered according to the following scheme:
● Courses starting with “0” are developmental, remedial, or
supporting courses. These are not published on the student
transcript and do not have credits assigned to them.
● Roman numerals (I, II, etc.) after course titles indicate
segments of a multi-course sequence.
● The numbers 1, 2, etc after course titles indicate segments of
a multi-course sequence.
Sequence of Courses
The nursing and science courses are sequential, and successful
completion is a prerequisite for progressing to the next level.
Course Delivery
Residential Delivery
All courses are taken at the School or at the clinical facilities
located in Illinois.
Blended Delivery
Blended delivery includes online live sessions, asynchronous
sessions, in person campus sessions, and on site clinical
components. All in person campus and on site clinical sessions
are located in Illinois. Blended education courses are delivered
through the ATS learning management system (LMS).

8
| Page
Personal desktop or laptop computer with internet access is
required. See Minimum Computer System Requirements policy.
Add/Drop Period
Official course adjustments can be made during the first two weeks
of the semester only. Only students attending the current semester
may add courses.
● During the first week of classes, a student can add a course
with instructor approval.
● During the first two weeks of the semester, a student can
request to drop a course without penalty. The student must
complete a course drop request with the Registrar.
● Dropping Corequisite Courses: If a student drops
a course that is a co-requisite to another course that
the student is taking, the student will have to drop
the co-requisite course also.
● If a student drops courses after the expiration of the two-
week add/drop period, the student is financially responsible
for the tuition cost of all the courses for which the student
was registered as of the last day of the second week.
● If a student needs to drop ALL courses during the Add/Drop
period, for which the student is registered, the student may
request a leave of absence (LOA) or withdraw from the
program. Request for LOA or withdrawal is made to the
Registrar Office. See Leave of Absence, Program
Withdrawal Policy
Any changes to an assigned schedule may affect the amount of
federal and school/financial aid a student may receive. Students
receiving federal financial aid must notify the Financial Aid Office
regarding any changes to their enrollment status.
Students may be responsible for charges incurred. See Refund
Policy.
Attendance Policy
Each student is expected to attend every class, lab, and clinical day
for which the student is scheduled. Students must complete all
required academic activities in each session.
Students are responsible for work missed during an absence for
any cause. If missing coursework jeopardizes progress in a course,
the student’s instructor may submit a warning to the student. The
student will need to meet with the retention specialist to discuss
and follow up with a plan in order to complete coursework. If a
student continues missing coursework after the warning and
meeting with the retention specialist, the instructor may drop such
a student from the course; and any drop initiated by an instructor
for a student’s lack of engagement past the drop date is recorded
on the student’s permanent record with a grade of “WF”.
Breaches of professionalism, including signing in for others,
signing in without physically attending, or signing in and leaving
(without permission) before completion of class, and/or class
activities required are violations of the School Academic Honesty
and Integrity policy.
ATS has a zero-tolerance policy regarding academic dishonesty in
any form and students in breach will be subject to the
corresponding penalties such as failure of the course or immediate
dismissal.
Safe Online Class Attendance. Attending online classes while
driving or working is prohibited. Students are to attend classes,
including virtual course meetings, in a safe, conducive to learning
environment. If a student is found driving or working while
attending their class, they may be dismissed from the class session.
Nursing Clinical Attendance
Attendance at all clinical sessions is mandatory. Any absence in
clinical may result in failure of the course. No call, no show
absence(s) may result in failure of the course.
Tardiness Students are expected to arrive at all sessions at least
10 min prior to scheduled start time and complete the entire
session.
Arriving more than 10 minutes late will result in an absence and
the student will be sent home for the day.
Any unforeseen tardiness must be reported to instructors before
scheduled start time.
Absences: Absences due to extenuating circumstances, See Make-
Up Policy.
Policy on Severe Weather
In the event of inclement weather, the Nursing Programs
Administrator will decide whether to close the school due to
hazardous conditions. In-person sessions may be moved to an
online session as notified. Online sessions will meet as scheduled.
Any additional changes will be communicated to students by LMS
announcements.
If the school is closed, clinical experiences are still required as
scheduled. Notification of any clinical changes will be made by
school email/LMS. Absences due to weather are not excused.
Notification of clinical absence because of weather MUST
ALWAYS be reported to the clinical facility, the clinical
instructor/teaching assistant and to the school.
The method of communication for school closure will be provided
to students in advance. See school website for the updates.
Make-Up Policy
Students are expected to arrive 10 minutes prior to exams and
clinical experiences.
To avoid disruption during these times, students will not be
allowed entrance after the start of the exam or clinical. Students
who are absent or arrive late for exams or clinical may be allowed
a make-up if an extenuating circumstance has occurred and faculty
are notified in advance when possible.
The instructor of the course will have the final decision for an
exam or clinical makeup due to extenuating circumstances. Only
one make-up is allowed, per course.

9
| Page
Failure to notify faculty in advance can result in a “no call, no
show” and the student will not be allowed a makeup. All requests
for makeup must be initiated by the student with the faculty as soon
as possible and the make-up must occur within the timeframe
given.
Exam Make-up
Once an exam make-up is scheduled, it cannot be canceled and
rescheduled unless another extenuating circumstance has
occurred, and faculty are notified in advance or no less than 24
hours of rescheduled exam time. Make-up in these situations must
occur within the time approved by faculty.
A grade of zero shall be given in the event a student does not attend
a make-up exam or rescheduled make up exam, there is no
exception, and this is not appealable.
Clinical Make-up
It is important to note that makeup is not guaranteed. In the event
a makeup is provided, the date and time will be determined at the
end of the semester by the Director of Nursing. Clinical make-ups
will not be rescheduled.
Extenuating Circumstances
To qualify for an extenuating circumstance, students must notify
faculty prior to but no later than 48 hours from the exam/clinical
time, via the Emergency Absence form located in the LMS.
1) Illness with dated and signed statement from health care
provider on letterhead.
2) Required testing/hearings from governmental agencies with
required documentation.
3) Recovery from an accident with a signed statement from the
appropriate agency.
4) Required court attendance with copy of court summons.
5) Death in the immediate family such as
spouse/parent/sibling/dependent with death notice or funeral
home document.
6) National Guard or Reserve weekend drill or annual training
with documentation and/or orders.
Routine doctor visits, childcare issues, work issues, and others not
listed here may not be considered extenuating circumstances.
Final exams will not be given after final exam week.
Exam Retakes: Under no circumstances will previously taken
exams be repeated.
Academic Monitoring Program
The goal of the Academic Monitoring Program is to promote
student academic success and retention in the Practical Nursing
program. The program is designed to provide guidance and
support to students experiencing academic difficulties in one or
more courses, having a history of not meeting Standardized Testing
Progression benchmark, readmitted to the program or having
received a grade below “C” the previous semester.
Students may be assigned to the Academic Monitoring Program at
the semester start or during the semester. Students on Academic
Monitoring may have a reduced course load. It is important to note
that if a student is referred to academic monitoring they will be
required to meet with their instructor and/or nursing coach. If this
is not met the student may be dismissed.
A student may be assigned to the Academic Monitoring program
at any time during the semester for reasons that may include but
are not limited to:
● Receives a grade below 78% (80% in any Math or Seminar
course) on two consecutive tests anytime during the
semester.
● Performs below a satisfactory level in clinical and lab.
● Attendance issues including tardiness and absences.
● Concern of the instructor regarding student performance
● Any personal issues that may be contributing to students'
performance.
● Students will also need to meet with the retention specialist
If the student is assigned to the Academic Monitoring Program,
the student will be notified by the instructor of the course and/or
the Retention Specialist.
Academic Monitoring requires the student to:
● Participate in Focused Learning Seminar (FLS)
● Complete the Individualized Learning Plans (ILP) created
with them by the nursing coach
● Meet with Nursing Coaches and/or instructors for one on one
session as scheduled on the ILP.
● Meet with the retention specialist
Note:
● Students are allowed to reschedule the individual
session/tutoring one time without penalty, provided that
notice is at least 24 hours in advance.
● Missing a session/tutoring due to a no call no show (NCNS)
will result in all pre-scheduled sessions being removed from
the Coach/Instructor’s calendar.
Students who fail to meet the ILP provided to them and follow up
with the nursing coach and retention specialist will automatically
fail the course corresponding to the ILP that may lead to dismissal
from the program.
Withdrawal
When a student withdraws from all classes, regardless of the
withdrawal reason (i.e. course, emergency leave), the student’s
Financial Aid package will be re-evaluated based on the
withdrawal date. For Federal Direct Loan purposes, the student
will be considered withdrawn and the grace period will begin as of
the withdrawal date. The student account shall be reviewed with
the Bursar’s Office.
Course Withdrawal
Any student who wishes to officially withdraw from a course must
obtain, complete, and return an official form from the Registrar
Office. Withdrawing from a course may extend your date of
graduation. Additionally, you may need to take the course in a later
semester if it is not readily available. Students receiving federal
10
| Page
financial aid must notify the Financial Aid Office regarding any
changes to their enrollment status.
No more than one withdrawal with “W” grade per course, or its
equivalent, is permitted. Courses, which are marked with a “W”,
are not included in calculation of the GPA but are included in the
calculation of hours attempted (PACE) and towards meeting the
Maximum Time Frame requirements.
Students with more than 2 withdrawals, or a withdrawal and course
failure in the program will be required to meet with the Enrollment
Committee and must adhere to the plan of study created for them
at that time.
A student who withdraws from all courses in a semester may
request to remain enrolled in the program by submitting the
withdrawal Semester Courses Form within 3 days of the
withdrawal to the Registrar’s office. The student will be notified if
their request is approved or denied via ATS email. Students
approved are required to complete the Return from Leave
requirements.
Students denied or who do not complete the Withdrawal Semester
Courses Form, will be withdrawn from the program.
Emergency Leave
The Emergency Leave may be requested in circumstances that are
considered unforeseen situations or events beyond the student’s
control which directly and negatively affect academic
performance. Emergency leave is approved on a case-by-case
basis by the Director of Nursing or designee. An Emergency Leave
provides an opportunity for a student to withdraw from all courses
up to the end of week 10 of the semester.
NOTE: If you do not plan to return or your situation will not allow
you to return within 6 months, you will need to request a
withdrawal from the program.
An emergency leave withdraws students from all classes.
Emergency Leave from an individual course is not permitted. A
student is allowed one Emergency Leave throughout the program.
Below is a list of possible circumstances and the suggested
documentation needed to substantiate the Emergency Leave.
Please note, the following list is not exhaustive. Students may
provide circumstances and documentation not mentioned below
to be considered for Emergency Leave. Additionally, providing
a circumstance with supporting documentation from the list
below does not guarantee an approval of Emergency Leave.
All Emergency Leave Requests must be submitted within 10
days after the last date of attendance.
Acceptable documentation will be on official letterhead and
obtained through an objective third party. Objective third parties
include, but are not limited to: counselors, doctors, lawyers,
social workers, religious leaders, state/government agencies, etc.
NOTE: Special permission to receive an emergency leave after
any of these deadlines must be granted by the Director of Nursing
or designee.
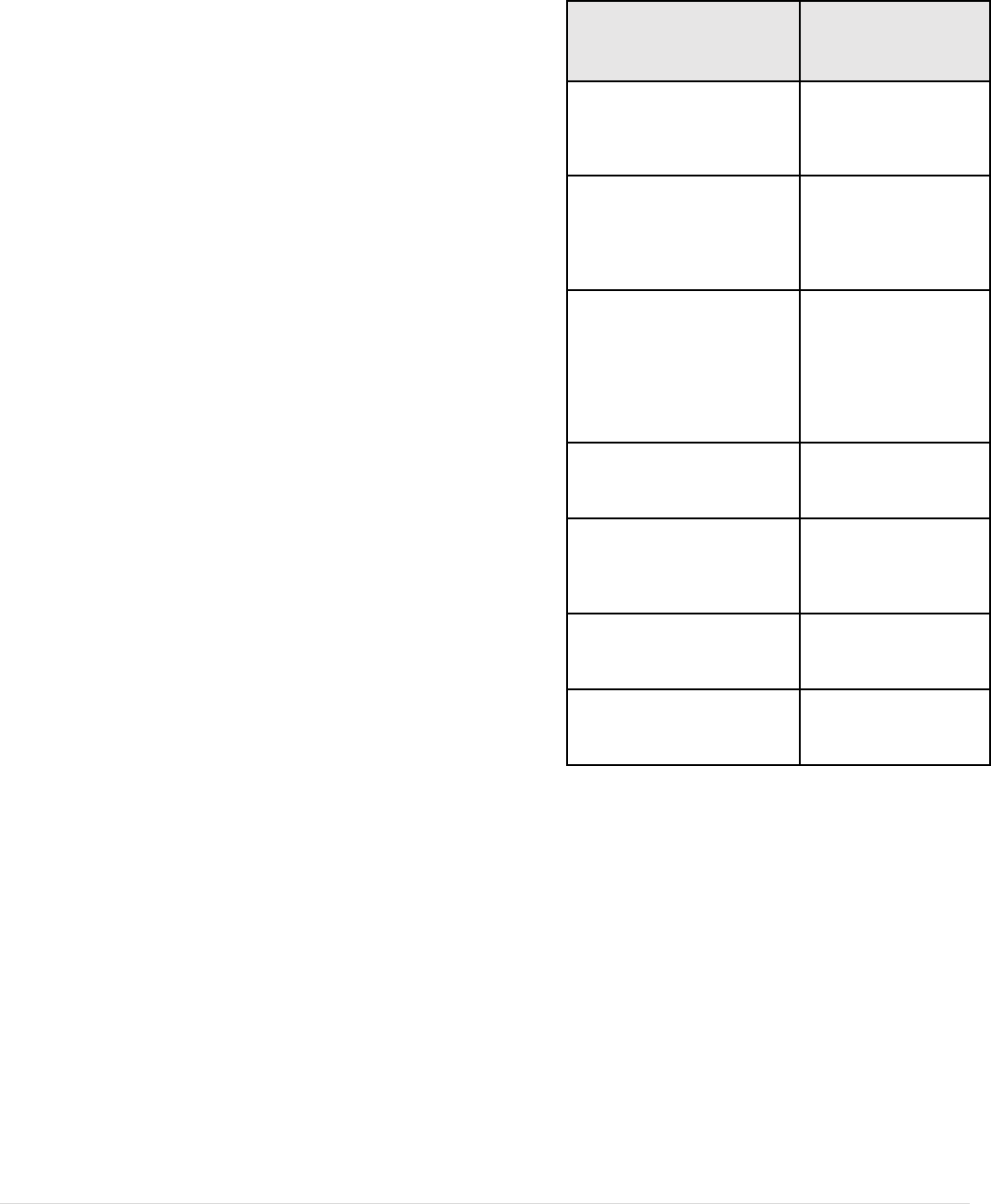
Possible Circumstances
Suggested
Documentation
Death of a legal dependent or
immediate family member such
as a spouse/parent/sibling
Death certificate,
obituary
A crime which may or may not
result in medical care such as a
sexual assault, stalking
incident, dating or domestic
violence incident.
Court documents,
restraining
orders, police records
An ongoing medical issue that
incapacitates or will
incapacitate the student from
attending course sessions that
exceeds the maximum allowed
absences as outlined in the
attendance policy
Hospital
documentation,
doctor’s
documentation that
shows medical
situations that are
ongoing or acute.
Medical reasons for pregnant or
postpartum
Supporting
documentation from a
healthcare provider
Medical issue of family
member in which the student
has to become a part-time or
full-time caretaker
Supporting
documentation from a
healthcare provider
and/or attorney
Sudden or consistent lack of
transportation issue
Auto documentation,
route cancellation
documentation
Significant cost of living
increase
Rental/mortgage/ lease
documentation.
Emergency leave is NOT intended to and will not be granted to:
● Serve as a solution to unsatisfactory progress or other
academic or behavioral concern
● Assist a student in avoiding disciplinary actions related to
potential misconduct
● Assist a student who reports lack of knowledge or
misunderstanding of the refund deadline or policy.
● Remove charges from a student account.
Once approved, the student will receive a W for all courses in the
semester in which they will be approved for an emergency leave.
The student will be expected to return within 6 months. If the
student does NOT return within the specified deadline the student
will be required to complete the entire re-admission process.
Program Withdrawal
When withdrawing from the program a withdrawal form must be
completed by the student and signed by the student, registrar, and
financial aid. Program withdrawal may affect your Financial Aid

11
| Page
package and funds may be returned to the Government. Thus, you
may have a balance to the school that needs to be paid off.
Leave of Absence
Students may request a Leave of Absence (LOA) in writing prior
to the beginning of the semester in question or during the Add/drop
period. Allowable reasons for an approved LOA include
circumstances covered under the Family and Medical Leave Act
(FMLA), legal obligations, medical, employment requirements,
jury duty or military service. The student must have successfully
completed at least one term to be considered for an LOA.
To proceed with an LOA the student must:
● Obtain a form from the Registrar’s Office.
● Explain the reason for the LOA request
● Sign and date the form
● Submit the form to the registrar
● Monitor the decision. Students will be informed in writing
by email about the decision to grant or deny the LOA.
Requesting an LOA does not guarantee it will be accepted.
Students may be granted one Approved Leave of Absence (LOA)
that should not exceed 180 calendar days in a twelve (12) month
period. The twelve (12) month period begins on the first day of the
student’s leave of absence.
Military Leave
Enrolled students who are called to active military service of the
Armed Forces, are allowed leave, if such members are temporarily
unavailable or must suspend enrollment by reason of serving in the
Armed Forces. Leave time must fall within the Leave of Absence
guidelines (See Leave of Absence Policy). Such students may
receive a refund in accordance with the Refund Policy. See Refund
Policy
Return from Leave Policy
It is the student’s responsibility to complete requirements to return
from leave, this includes:
● Submit an intent to return to the Registrar’s Office
● Meet medical compliance requirements (See appendix F:
Documentation for Clinical)
● Complete any Financial and Financial Aid outstanding
requirements.
● Meet with the Bursar’s office to verify there are no current
account balances
● Review an updated Plan of Study
● All requirements must be completed 30 days prior to the
semester of return.
Students returning from leave will be held to all program
requirements as outlined in the Student Catalog in effect for the
cohort they are returning into.
If a student does not return to the institution at the expiration of an
approved leave, the student’s withdrawal date will be the date the
student requested the leave. In addition, the grace period of loan
repayment is also determined by the withdrawal date.
Student Maternity Policy
If a pregnant student is enrolled in a clinical course and wishes to
remain in the clinical setting, a medical release must be signed by
the student and their health care provider and submitted to the
Nursing Programs Administrator or designee as soon as the student
has a confirmed pregnancy. Once the Director of Nursing has
received and reviewed the signed medical release, a copy of the
document will be sent to the clinical instructor and clinical
coordinator. If the student cannot be accommodated due to their
restrictions they will need to withdraw and may return after the
pregnancy once cleared by their physician. A student will not
receive a passing grade for a clinical course without completing
the clinical component.
Student Services
Orientation
Orientation is held prior to the first day of class for each new start
date to welcome and acclimate new students to ATS.
Representatives from school departments provide information to
help new students transition into their new academic environment
and familiarize them with all resources available to them to help
them succeed in their program.
Students attending in a blended format will receive training on the
navigation of ATS’s learning management system and be provided
with access to an online program to assist them. Blended distance
education students have access to technical support on campus and
virtually through their instructor, the campus IT department, and
the Admission Department.
Student Academic Support Services
The Academic Support Services at the School include academic
support, career counseling, retention specialist and tutoring. The
primary goal for Student Academic Support Services is to
encourage the enrollment and retention of students and to facilitate
the successful completion of their goals in the School.
Academic Support Services:
● Assist students with time management, stress management,
anger management, test taking skills, note taking skills,
communication skills and career development.
● Help students identify social problems and emotional
problems that may interfere with educational and academic
progress.
● Collaborate with the teachers and administration with the
student’s evaluation and student’s academic progress.
● To assist in setting goals, initiating strategic planning, and
implementing curriculum objectives as established by classes
and faculty.
● Provide crisis intervention when conflict arises in the school.
● Assist students with career development and job search
strategies.
● Assist students in adjusting to School with regards to
academic standards and new life experiences.
● Refer students to outside professional health centers when
domestic abuse or family problems are identified.

12
| Page
Tutoring
Tutoring is available for all students. All tutoring is at no additional
cost to students. Students who are looking for further assistance
with their learning materials or are experiencing difficulty
understanding the learning material should contact the instructor
and/or Nursing Coaches to schedule tutoring. These sessions must
be scheduled outside of normal classroom instruction hours.
Students may be referred to receive tutoring if they are having
difficulty in the course or receiving a 78% or less on their exams.
One on one tutoring is available with faculty and coaches by
appointment within the Learning Management System (LMS). The
following will apply for students who need to reschedule or cancel
their meeting with their tutor:
● Students are allowed to reschedule the individual
session/tutoring, provided that notice is at least 24 hours in
advance and per availability. Students with extensive
cancellations will result in all pre-scheduled sessions being
removed from the Coach/Instructor’s calendar.
● Missing a session/tutoring due to a no call no show (NCNS)
will result in all pre-scheduled sessions being removed from
the Coach/Instructor’s calendar.
Group tutoring and Focused Learning Seminar (FLS) are also
offered to help students with course content. Group tutoring
sessions are announced in the LMS. The FLS schedule will be
posted in the LMS.
Licensure Exam Preparation
At the end of identified nursing courses, students are given a
standardized test for the nursing course that they are completing.
Students then receive remediation recommendations to assist them
in preparing for the licensure exam.
Career Services
The following placement services are provided: requests from
companies, organizations, agencies, job fairs, open houses are
posted on the ATS website, accessible to current and graduate
students to access. The curriculum includes resume writing and
job interview skills. No guarantee is given to any student that he
or she will obtain employment through the efforts of the school
because of training received at the school.
Health Services
The School does not provide on campus health services.
Students who become ill in the classroom/lab setting will be sent
home by the faculty member or transported to the nearest medical
facility by EMS. If the student defers, the student may sign a
release form stating refusal and arrange for their own
transportation.
Students who become ill in the clinical area will be sent home after
reporting to the clinical instructor or transported to the emergency
room if in a hospital or transported by EMS if in a non-hospital
setting.
Procedure for both the classroom and clinical settings:
● The faculty member may send students who arrive for class
ill home when any of the following conditions are present:
o Any sneezing and or coughing accompanied by an
elevated temperature.
o Vomiting.
o (Clinical Only) Any other illness banned by the
clinical agency especially in maternity and
pediatric areas.
● EMS will be called for all students who:
o Faint.
o Complaint of chest pain.
o Vomit blood.
o Suffer any injury requiring sutures.
o Are splashed with any toxic substance, especially
in the eyes.
If a student becomes gravely ill and/or has an emergency illness
that makes them incapacitated or unable to be mobile without
assistance, faculty must call 911 or EMS or the student’s
emergency contact depending on the nature of the illness. Under
no circumstance should faculty or another student transport the
sick student to the emergency room or home. The School staff
should not offer medical treatment.
Student Resources
Students have access to an online library through the Learning
Management System (LMS) and the school website. The online
library provides the students with current materials and
supplements the school’s on-site resources. The Resource Room
holds current textbooks as well as references for the students to use
at school. Laptops are available for students for emergency use
and who meet the criteria for loaner laptops.
Local and National Community Resources
Should a student encounter a personal problem that interferes with
the ability to complete coursework, the student will be aided in
identifying appropriate professional assistance in the student’s
local community but does not offer personal counseling assistance.
See Appendix H: Local and National Community Resources
Parking and Transportation
Parking is available for students who drive to school. Students may
get discounted coupons for the garage at 20 East Randolph. ATS
is located on major bus, trains, and “L” routes, which makes it
easily accessible to those students without a car.
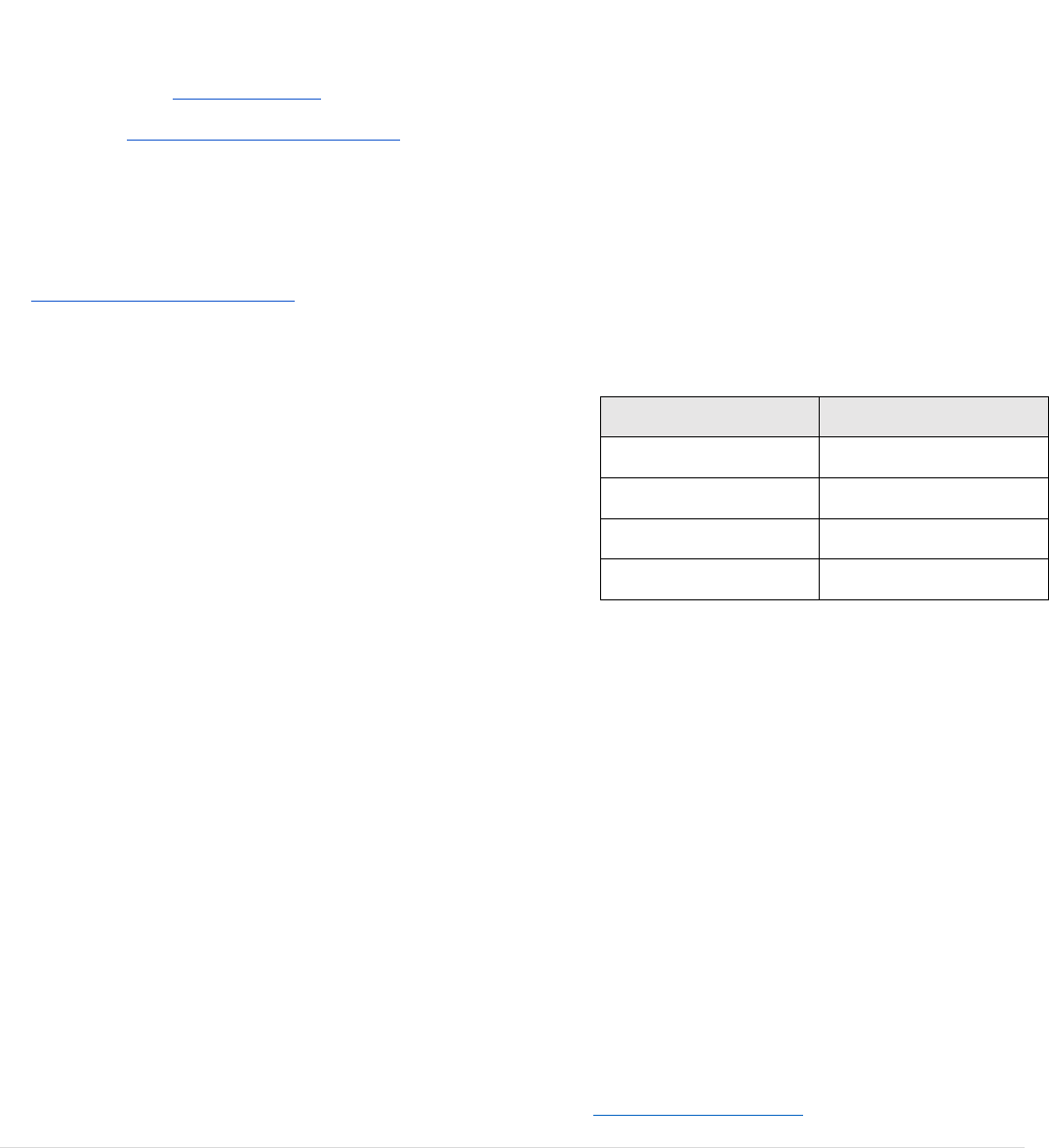
The following transit lines have routes that pass near the building.
ATS cannot guarantee student transportation.
● Bus: 147, 151, 20, 22, 3, 56, 6
● Train: MD-N, MD-W, RI, SSL, UP-N, UP-NW
● Chicago 'L': BLUE LINE, GREEN LINE, PURPLE LINE,
RED LINE
Student Housing
ATS does not provide student housing. ATS does not assume
responsibility for student housing, does not have dormitory
facilities under its control, nor offers student housing assistance.
According to rentdata.org for Chicago, IL rental properties start at
approximately $1161 per month.
13
| Page
Childcare / Children on Campus
Students with childcare concerns should speak with the Registrar
office. Students may not bring their children to the school.
Photo Release
Throughout the year, ATS may take images/photographs and/or
videos of students, faculty, and staff on campus or participating in
school activities. These images/photographs and/or videos may
appear in various ATS publications, including, but not limited to,
the ATS website (www.atsinstitute.edu), graduation programs,
brochures, institutional calendar, social media, or mass media
outlets. The ATS Photo Release “Opt-Out'' Form provides all
persons NOT interested in having their image/photograph and/or
video presence captured and used for marketing, communications,
and PR purposes the opportunity to Opt Out.
By deciding to opt out, you are choosing NOT to participate in the
marketing, communications, and PR opportunities stated above.
Complete the following form if you are interested in opting out.
ATS Photo Release “Opt-Out” Form.
Honors and Awards
Student of the Month Award
Students are nominated to be Student of the Month by an ATS
faculty and/ or staff member. The members of the Student of the
Month Committee then select one student each month. All
students with a good attendance record and passing grades are
eligible for nomination. Students that are nominated exemplify
professionalism, caring for others, leadership, outstanding
academic performance, and are good role models for their fellow
nursing classmates.
Student of the Month nominees will receive:
1) Letter of Acknowledgement
2) Automatic consideration for the Student of the Month Award
Student of the Month winners will receive:
● $15 gift card
● Student of the Month Certificate
● Letter of Acknowledgement
● Automatic nomination for Student of the Semester Award
Student of the Month winners may also list this award under
“Honors” on the student’s resume for future employers to see.
Student of the Semester Award
At the beginning of the new semester, one Student of the Semester
winner is chosen from the previous semester. The Student of the
Semester will be nominated by the faculty and chosen by the
Student of the Month committee.
The Student of the Semester winner will receive:
● $20 gift card
● Letter of Acknowledgement
● Student of the Semester Certificate
Clinical Excellence Award
At the beginning of the new semester, one student will receive a
Clinical Excellence Award from the previous semester. Clinical
students eligible for the Clinical Excellence Award will be
nominated by nursing faculty and chosen by the Student of the
Month committee. Criteria for nomination are modeled after Jean
Watson’s Theory of Human Caring.
The Clinical Excellence Award winner will receive:
● $20 gift card
● Letter of Acknowledgement
● Clinical Excellence Award certificate
President’s List
Special recognition is awarded to students who earn a 3.5 GPA and
perfect attendance during the previous nursing semester in which
they accumulate at least twelve (12) credits. President’s List
students receive a letter of acknowledgement. Students with
behavior violations on file are excluded from consideration.
Graduate with Honors
Students who have earned a cumulative GPA of 3.0 or higher are
eligible for graduation with honors. The honors designation will
appear on the diploma as follows:
GPA
Honor Designation
3.00 – 3.49
Merit
3.5 – 3.79
Cum Laude
3.8 – 3.99
Magna Cum Laude
4.00
Summa Cum Laude
Student Policies
Official Communication with Students
The assigned School email account shall serve as the official
means of communication with all students. Examples of such
communication include but are not limited to notifications from
the School, Program, Financial Aid Office, Bursar office,
Registrar’s Office. Course information (class materials,
assignments, questions, and instructor feedback) will be provided
through the Learning Management System. Students are required
to activate their school email account upon enrollment and are
responsible to routinely check for updates. Faculty and/or staff are
not required to respond to personal emails that are not assigned
school email accounts.
Transcript Request
Students who are actively enrolled may access an unofficial
transcript in their SIS account.
Students and previous students may request a transcript by
completing a Transcript Request via the Parchment website,
https://www.parchment.com/. Transcripts will only be processed

14
| Page
with submitted via Parchment. Each copy costs $10-$20, digital
and printed copies are available.
All outstanding obligations (school and financial) must be met to
complete the Official transcript request. Outstanding obligations
must be cleared with the Bursar’s office to release the transcript.
An unofficial transcript may be released upon request.
Student records are not released to an employer or school without
the signed release by the student.
Smoking, Gum, Eating and Drinking
Smoking is prohibited throughout the School premises. All
students and employees are to refrain from smoking on or around
the school premises and doorways including the parking lot
grounds unless they are inside their vehicles or in the designated
smoking area. Students are not permitted to smoke within 30 feet
of the school building. Students are not permitted to smoke at
clinical sites, this includes vaping.
Any offenses will be subject to the following:
● First violation: written notice.
● Second and subsequent violations: Suspension for one full
day.
● This policy also applies to the clinical area. Students must not
arrive at the clinical site with the smell of smoke on their
uniforms.
Chewing gum is not allowed in the classrooms, labs, or clinical
area.
Except for bottled water, eating and drinking is not allowed at any
time in any classroom, lab, or clinical area.
Cell Phone Policy
Cell phones are not permitted to ring in the classroom, laboratory,
or during a clinical shift and must be on vibrate. Should an
emergency call come through, the student must be mindful of not
disrupting the class when leaving to take the call. Only one
emergency phone call is allowed per class. Use of cell phone in
the classroom other than that stipulated above shall warrant a
Behavioral Violation and will be documented as such. Emergency
calls can be directed to the main school number. Personal
electronic devices, including but not limited to cell phones, smart
watches, and tablets are not allowed during exams.
Discipline Policy
Standards of Professional Conduct
Required Conduct
All students are required to behave responsibly and professionally
and are obliged to behave in a manner compatible with the
philosophy and objectives of the school. A quiet atmosphere would
be appreciated while classes are in session and during midterm and
final exam weeks.
The school recognizes its responsibility to the professional
community and to the consumers of the professional community.
Therefore, any action by a student considered to be unprofessional
shall be deemed cause for disciplinary action and/or dismissal.
Any violation of expected conduct while providing patient care
may result in immediate dismissal.
A student who does not meet the required standard of conduct may
be placed on disciplinary probation, disciplinary suspension, or
disciplinary dismissal from the program. However, any action
taken depends upon the nature of the offense and the merits of the
individual case. The school reserves the right to eliminate any step
in the case of any infraction.
A student in the school is expected to:
● Be concerned and considerate of the welfare of others as well
as self.
● Exercise good judgment in all aspects of personal behavior.
● Respect local ordinances and state and federal statutes.
● Continued inconsiderate or irresponsible behavioral patterns
will be treated as a serious matter by the school.
Civility Code of Conduct
Vision for Civility - Shared Responsibility. It is everyone’s
responsibility in the School of Nursing to have an attitude of
civility and professionalism in fulfillment of the mission,
values, and norms of ATS Institute.
Civility will be openly discussed throughout the program.
Civility in nursing education will prepare students for civility in
nursing practice. Our graduates will be competent to function
effectively within license practical nursing and interprofessional
teams, fostering open communication, mutual respect, and shared
decision- making to achieve quality patient care.
See Appendix Q Civility Code of Conduct
Violations of the Code of Conducts
● Obstruction or disruption of any school activity: If disruption
or insubordination occurs at the school or in clinical, the
student may be suspended for one week. A student may
make up a missed test but cannot exceed the one (1) test limit
per course.
● Damage to property of the institution, a member of the staff,
another student, patient, or visitor.
● Physical abuse or behavior that threatens the safety or health
of any other person.
● Unauthorized access to institutional facilities.
● Abuse and/or misuse of fire safety equipment, including
transmittal of a false alarm of fire or tampering with fire
extinguishers or hoses.
● Any act that results in conviction of a felony.
● Discourteous treatment of patients, visitors, hospital
employees, other students, faculty, or staff.
● Divulging confidential information.
● Harassing or unfairly treating any person because of race,
religion, color, gender, sexual orientation, national origin, or
disability.
● Engaging in sexual harassment or sexual assault.
● Using, selling, possessing, or distributing drugs or other
illegal substances while on clinical or School premises.
● Violation of safety rules.
● Using physical or verbal abuse, profanity, or violence in any
form.
● Fighting, inciting a fight, or disorderly conduct.

15
| Page
● Intoxication or drinking on clinical site property or school
premises.
● Gambling on clinical site property or School premises.
● Theft or embezzlement.
● Carrying and/or concealing weapons.
● Accepting anything of monetary value from anyone who
might benefit from the student services.
Student Code of Conduct While Providing Nursing
Care
● A student shall, in a complete, accurate, and timely manner,
report and document nursing assessments or observations, the
care provided by the student for the patient, and the patient's
response to that care.
● A student shall, in an accurate and timely manner, report to
the appropriate practitioner errors in or deviations from the
current valid order.
● A student shall not falsify any patient record, or any other
document prepared or utilized in the course of, or in
conjunction with, nursing practice. This includes, but is not
limited to, case management documents or reports, time
records or reports, and other documents related to billing for
nursing services.
● A student shall implement measures to promote a safe
environment for each patient.
● A student shall delineate, establish, and maintain professional
boundaries with each patient.
● At all times when a student is providing direct nursing care to
a patient the student shall:
● Provide privacy during examination or treatment and in the
care of personal or bodily needs; and
● Treat each patient with courtesy, respect, and with full
recognition of dignity and individuality.
● A student shall practice within the appropriate scope of
practice.
● A student shall use universal and standard precautions.
A student shall not:
● Engage in behavior that causes or may cause physical, verbal,
mental, or emotional abuse to a patient.
● Engage in behavior toward a patient that may reasonably be
interpreted as physical, verbal, mental, or emotional abuse.
● A student shall not misappropriate a patient's property or:
● Engage in behavior to seek or obtain personal gain at the
patient's expense.
● Engage in behavior that may reasonably be interpreted as
behavior to seek or obtain personal gain at the patient's
expense.
● Engage in behavior that constitutes inappropriate
involvement in the patient's personal relationships; or
● Engage in behavior that may reasonably be interpreted as
inappropriate involvement in the patient's personal
relationships.
For the purpose of this paragraph, the patient is always presumed
incapable of giving free, full, or informed consent to the behaviors
by the student set forth in this paragraph.
A student shall not:
● Engage in sexual conduct with a patient.
● Engage in conduct in the course of practice that may
reasonably be interpreted as sexual.
● Engage in any verbal behavior that is seductive or sexually
demeaning to a patient.
● Engage in verbal behavior that may reasonably be interpreted
as seductive, or sexually demeaning to a patient.
For the purpose of this paragraph, the patient is always presumed
incapable of giving free, full, or informed consent to sexual
activity with the student.
● A student shall not, regardless of whether the contact or
verbal behavior is consensual, engage with a patient other
than the spouse of the student in any of the following:
o Sexual contact.
o Verbal behavior that is sexually demeaning to the
patient or may be reasonably interpreted by the patient
as sexually demeaning.
● A student shall not self-administer or otherwise take into the
body any dangerous drug, in any way not in accordance with
a legal, valid prescription issued for the student or self-
administer or otherwise take into the body any drug that is a
schedule I controlled substance.
● A student shall not habitually or excessively use controlled
substances, other habit-forming drugs, or alcohol or other
chemical substances to an extent that impairs ability to
practice.
● A student shall not have impairment of the ability to practice
according to acceptable and prevailing standards of safe
nursing care because of the use of drugs, alcohol, or other
chemical substances.
● A student shall not have impairment of the ability to practice
according to acceptable and prevailing standards of safe
nursing care because of a physical or mental disability.
● A student shall not assault or cause harm to a patient or
deprive a patient of the means to summon assistance.
● A student shall not misappropriate or attempt to
misappropriate money or anything of value by intentional
misrepresentation or material deception in the course of
practice.
● A student shall not abandon a patient.
● A student shall not have been adjudicated by a probate court
of being mentally ill or mentally incompetent, unless restored
to competency by the court.
● A student shall not aid and abet a person in that person's
practice of nursing without a license, practice as a dialysis
technician without a certificate issued by the board, or
administration of medications as a medication aide without a
certificate issued by the board.
● A student shall not assist suicide.
● A student shall not submit or cause to be submitted any false,
misleading, or deceptive statements, information, or
document to the program, its administrators, and instructors.
● A student shall maintain the confidentiality of patient
information. The student shall communicate patient
information with other members of the health care team for
health care purposes only, shall access patient information
only for purposes of patient care or for otherwise fulfilling the
student's assigned clinical responsibilities, and shall not
disseminate patient information for purposes other than
patient care or for otherwise fulfilling the student's assigned
clinical responsibilities through social media, texting,
emailing or any other form of communication.

16
| Page
● To the maximum extent feasible, identifiable patient health
care information shall not be disclosed by a student unless the
patient has consented to the disclosure of identifiable patient
health care information. A student shall report individually
identifiable patient information without written consent in
limited circumstances only and in accordance with an
authorized law, rule, or other recognized legal authority.
● Student shall not use social media, texting, emailing, or other
forms of communication with, or about a patient, for non-
health care purposes or for purposes other than fulfilling the
student's assigned clinical responsibilities.
Disciplinary Process of Student Misconduct
While Providing Nursing Care
Any student found to be in violation of the expected conduct while
providing nursing care will result in written warning, disciplinary
probation, disciplinary suspension, or disciplinary dismissal from
the program. Any action taken depends upon the nature of the
offense and the merits of the individual case.
Violations of any expectations listed under the Student Clinical
Accountability Expectations Form signed at the beginning of each
nursing course may result in immediate suspension from the
clinical and dismissal from the program without appeal.
Performance of any nursing skill, procedure or passing any
medication without the presence of the clinical instructor and/or
obtaining guidance of the clinical instructor will result in
immediate dismissal from the program without appeal.
Corrective Action
A student found to be in violation of the Code of Required
Conduct, or regulations defined in the student catalog, or other
published or posted institutional regulations will be disciplined
according to the nature of the offense.
Disciplinary actions are entered in the student’s confidential
personal file. The student receives written notice of action taken
that is recorded in the personal file.
The following sanctions represent corrective actions that may be
selected depending on the individual situation:
● Written Warning - A written notice to the student offender
that the student has violated the School rules and that further
violations will result in more severe disciplinary action.
● Restitution - Reimbursement for damage to, or
misappropriation of, the School property.
● Disciplinary Probation - A prescribed period of time in which
any additional violation of policy may result in a disciplinary
suspension/dismissal.
● Disciplinary Suspension - Exclusion of the offending student
from the School, its classes, and other privileges or activities
for a prescribed period in order to give the student time away
from the school to reflect on the problem and to understand
that further conduct infractions will lead to disciplinary
dismissal.
● During the suspension, the student will be marked absent for
the hours missed and will be subject to any consequence (such
as missed assignments) incurred by such absences.
● Disciplinary Dismissal - Permanent termination of student
status effective upon a specified date. A disciplinary
dismissal bars the student from campus and partner facilities.
A student may be immediately dismissed from school for the
following:
● Being under the influence of alcohol and/or illegal drugs
while on the school premises or in clinical. This includes
marijuana.
● Engaging in sexual harassment or sexual assault.
● Falsification of documentation
● Bullying and Harassment
A student will be immediately dismissed from school for the
following:
● Using, selling, possessing, or distributing drugs or other
illegal substance.
● Using physical or verbal abuse or violence in any form.
● Possessing a weapon of any kind on school property.
Any student who wants to dispute the basis for probation or
suspension should make a request to the Appeal Committee in
writing. The decision of the committee will be final.
Behavioral Violations
Behavioral violations will be given for incidents of inappropriate
behavior including, but not limited to, the following:
● Cell/mobile phone use other than outside of the
classroom/laboratory/clinical site.
● Student out of uniform.
● Student speaking out of turn.
● Foul or loud language.
● Failure to follow instructions.
● Excessive tardiness.
● Leaving early from clinical without instructor approval.
● Leaving the classroom (excessive in and out).
3 Step Violations “Write-Up” Policy
1st Write-Up
If a student is written up for the first time the result is a verbal
warning. Instructors will document an incident and it will be kept
on file.
2nd Write-Up
If a student is written-up for the second time the result is the
student will be placed on probation. Instructors will document the
incident to Student Services and a meeting will be scheduled with
the student and the school representative. The incident will be
discussed, a resolution will be made, and expectations will be
brought forth going forward along with consequences if not
followed. Additional violation of policy during the same semester
will result in a dismissal from class.
3rd Write-Up
If a student is written-up for the third time the result is the student
will be dismissed from the class. The instructor will document and
email the incident to the Director of Nursing. It will be reviewed
and discussed by the instructor and a Director of Nursing and a
decision will be made on whether you will be allowed to continue
into the program.

17
| Page
Statement of Liability
Students should be aware that ATS will prosecute students
involved in theft or damage of personal property. For their own
protection students should keep their personal property protected
and vehicles locked. ATS is not responsible for replacement or
reimbursement of stolen, damaged, or missing personal property.
All users of the School computers & internet agree not to hold the
School responsible for any and all claims, losses, damages,
obligations, or liabilities directly or indirectly relating to the use of
the internet or caused thereby or arising there from.
Users assume liability for any misuse of hardware, software, or
equipment residing in computer work areas. The School shall not
be responsible for personal property used to access computers or
networks. The School is not responsible for unauthorized financial
obligations resulting from access to the internet.
Computer and Internet Use Policies
Purpose and Use:
The School workstations are to be used primarily for research and
academic purposes, with the School students, faculty, and staff.
The students will be allowed to print research and academic
papers. The staff reserves the right to terminate an internet session
if its use is not research or curriculum orientated. Moreover, the
staff in charge reserves the right to ask users to end a session and
relinquish the computer to a School student, faculty, or staff
member.
The computer labs are intended primarily for instructional and
testing purposes. Faculty and staff have priority for scheduling
instruction in the labs. If no formal instruction is scheduled, the
School faculty, staff, and students may use the labs. The computer
lab must be vacant 10 minutes before a scheduled class session.
Every effort will be made to inform facility users ahead of time of
such reservations. However, the School reserves the right to close
the facilities to users at short notice to accommodate
instructional/testing needs.
The School reserves the right to monitor computer usage in the
labs to ensure compliance with the School policies.
To protect students’ access to functioning computers and to protect
computer hardware, software, networks, and the proprietary rights
of the School and third parties in commercial software, all students
must assume the following responsibilities of legal and ethical
computer and network use.
Depending on the severity of any violation of this policy,
consequences may include a written or oral reprimand, loss of
computer use privileges, dismissal from the School and/or referral
to the appropriate legal authorities.
● Any currently enrolled student or graduate in good standing
may use the meeting rooms, computer labs, and resource
center computer facilities. Guests are not permitted in the
computer labs or resource center.
● These resources are to be used for school or job-search-
related activities such as research, homework assignments,
and resume preparation. The School reserves the right to limit
or prohibit personal use of computing facilities at any time.
● Students are prohibited from using Internet resources or
computer facilities for the purpose of accessing pornographic
content; for the purpose of sending, receiving, and/or storing
chain mail, advertising, or fraudulent materials; for any
commercial or for-profit activity; for annoying or harassing
other users by such means as broadcasting unsolicited
messages or sending harassing, obscene, or offensive
messages; for sharing or receiving illegally copyrighted
contents and for any purpose which is prohibited by law.
● The computer facilities of the meeting rooms, computer labs,
and resource center may be used for authorized purposes
only. All areas may be used whenever the School is open, and
the rooms are not currently in use. The resource center may
be used anytime. The School reserves the right to close the
meeting rooms, computer labs, or resource room at any time,
with or without advance notice, whenever necessary for
maintenance or other purposes.
● Food or drinks may not be brought into the Lab rooms or
computer labs. NO EXCEPTIONS!
● Students are prohibited from installing, downloading, and/or
running any software, other than that provided by the School,
on school computers, without explicit permission from a
faculty member or administrator.
● Changing any settings or running any diagnostic or utility
programs on any computer or network of the Institution
without specific instruction by a faculty member or
administrator is strictly prohibited. “Settings” include, but are
not limited to, video display settings, mouse settings, printer
settings, network settings, and protocols, etc.
● Students may also choose to save files on a personal USB
flash drive. Saving their own data to any location other than
the student’s personal network storage space or USB flash
drive is prohibited. Attempting to change or delete any data
on the School’s computers or computer network is also
prohibited.
● Although the School makes the best effort to ensure the
integrity of files saved on its network, students are strongly
encouraged to keep a backup of all files saved on a personal
USB flash drive.
● The School is not responsible for any lost or damaged data
saved on its computer network.
● Every student will be assigned an account on the School’s
computer network. Sharing of accounts is strictly prohibited.
Students will be held accountable for all activity occurring on
their accounts. Therefore, all account information including
passwords must be kept confidential.
Use these basic account safety measures:
● Choose hard-to-guess passwords, at least 8 characters with a
letter, number, and symbol. Do not use common names. If
you forget your password, notify administration so that your
password may be reset.
● Never use another student’s account to log on for any reason
(this constitutes academic fraud).
● Never leave computers unattended without logging off.
● Never give passwords to someone else or allow others to use
your account.

18
| Page
● If you suspect that your account has been used by someone
else, notify Administration immediately.
● Use shared resources considerately. Do not monopolize
systems, overload networks with excessive data, or stream or
waste computer time, disk space, paper, or other resources.
Leave the work area clean and in order for the next person
when finished.
● Do not assume information stored on the School’s computer
facilities to be private. Any and all information saved on
Institution computer facilities may be accessed or deleted at
any time by school representatives.
● All computer files, disks, USB flash drives, etc. belong to
somebody. Assume them to be private and confidential unless
the owner has given explicit permission to make them
available to others. If in doubt, ask first.
● Staff, faculty, and students are strictly prohibited from
copying commercial or otherwise copyrighted software and
code, whether for use on or off-campus (except as specifically
permitted by the author or manufacturer) or engaging in any
other activity that may violate copyright, patent, or
trademark. (Consult the IT Specialist or the appropriate
software license agreement should you have any questions.)
● It is the school’s policy to comply with all copyright laws. All
faculty, staff, students, and members of the campus
community are expected to be aware of and follow these
requirements. Copyright law information can be found at
www.copyright.gov.
● Students are prohibited from accessing data or programs for
any reason without the owner’s explicit permission.
● Students are prohibited from downloading, installing,
creating, modifying, or transmitting any computer program or
instruction intended to gain unauthorized access to, or make
unauthorized use of, any computer facilities or software.
● Students are prohibited from using the School’s network,
intranet, learning management system, or computer facilities
with the intent to compromise other computers or networks,
to commit crimes, or to engage in other unethical acts. The
School will take necessary steps to preserve the security of its
computer resources.
Students will be billed for the cost of any damage to computer
hardware or the cost of reconfiguration of any software, or for any
other costs incurred by the institution because of a violation of
these rules.
Report any violation of this Computer Use Policy to the
administration immediately.
Wireless Access
The school is pleased to make wireless internet access available to
students throughout the campus. The following rules and policies
apply to wireless internet access. Use of wireless internet access
demonstrates your agreement to be bound by these rules and
policies.
1) Users are responsible for configuring their own equipment.
The School does not guarantee technical support for
establishing or maintaining a connection or equipment to
maintain a wireless connection.
2) The School is not responsible for any personal information
that is compromised, or for any damage caused to hardware
or software resulting from the use of the wireless Internet
connection for any reason whatsoever.
3) All users are responsible for maintaining their own virus
protection on their computers or wireless devices.
4) The transmission or receiving of child pornography or
sexually explicit graphics or material is strictly prohibited.
5) Users are prohibited from misrepresenting themselves as
another user; attempting to modify or gain unauthorized
access to files, passwords or data belonging to others, or
damaging or alternating others software or hardware.
6) It is prohibited to download copyrighted material in violation
of U.S. Copyright Law (Title 17, U.S. Code).
7) Use of laptops during class, without the permission of the
instructor, is prohibited.
8) Anyone violating these rules is subject to having the right to
use the wireless internet access terminated.
DISCLAIMER: The school is providing wireless connectivity in
this facility as a supplementary information service and offers no
guarantees or representations that any use of the wireless
connection is in any way secure or that any privacy can be
protected. Your transmissions may be viewed or intercepted by
third parties. Use of this wireless connection is entirely at the risk
of the user and the School is not responsible for any loss of
information that may arise from the use of the wireless connection.
Furthermore, the School is not responsible for any loss, injury or
damage resulting from the use of the wireless connection.
Instructions on how to access the wireless connection may be
picked up at the IT office or with the Administrative Assistant.
Social Media – Acceptable Use
Communications on social media must be always respectful and in
accordance with this policy. Use of social media must not infringe
on the rights or privacy of other students or staff, and students must
not make ill-considered comments or judgments about other
students, staff, or third parties. Students must take particular care
when communications through social media can identify them as
a student of ATS Institute of Technology to members of staff, other
students, or other individuals.
The following non-exhaustive list may, according to the
circumstances and be of an unacceptable nature and should never
be posted. Violation of any of these may result in dismissal.
Confidential information (which may include research not yet in
the public domain, information about fellow students or staff or
personnel matters, non-public or not yet approved documents or
information).
● Details of complaints and/or legal proceedings/potential legal
proceedings involving the school.
● Personal information about another individual, including
contact information, without their express permission.
● Students may not post obscenities, slurs, or personal attacks
that can damage the reputation of the Institution and its
representatives. Curriculum, Brightspace/D2L, or email
screenshot on any social media is strictly forbidden.
● Comments posted using fake accounts or using another
person's name without their consent.
● Material, including images, that is threatening, harassing,
discriminatory, illegal, obscene, indecent, defamatory, or
hostile towards any individual or entity.
● Any other posting that constitutes a criminal offense.

19
| Page
● Anything which may bring the School into disrepute or
compromise the safety or reputation of colleagues, former
colleagues, students, staff, and those connected with the
School.
The School has ways for students to raise any dissatisfaction or
concerns that they may have. (See Student Grievance and Appeal
Procedure).
Student Identification
All students must wear their identity badges while on school
property and clinical sites. Students must identify themselves as a
student to any faculty or staff member upon request.
Identity Verification and Privacy Protection
ATS utilizes the following authentication processes to verify
student identity.
Student Account Creation
The process of student account creation at ATS includes collecting
a student’s demographic and academic information for admission
to ATS. The data is stored in a secured server accessible via a
secured encrypted website by authenticated ATS employees.
Once the students are accepted into the program, an ATS student
email account is created using the Google Platform. Once the
accounts are created, the student is notified and must complete
their ATS account enrollment via a 2-step verification process.
ATS then creates a D2L/Brightspace- Learning Management
System (LMS) account using Single Sign On (SSO) and
integration with SAML authentication solutions and sends an
account creation message to the student’s ATS email. The student
then must click on the link within the account creation message
and finish the LMS registration process. Students can only see the
courses they are enrolled in.
Assignments are submitted through Brightspace/D2L that students
can only access by login to their respective Brightspace/D2L
account. The FERPA-compliant assignment tool means the
instructor's feedback can only be viewed by the student.
Student Account deactivation
will expire 365 days after a student graduates. During this grace
period, students are eligible to utilize their ATS email address for
job applications and other official business. Personal business
should be conducted on a student non-ATS email account. Alumni
will be informed ten days prior to their expiration of their ATS
email account. Immediately following successful completion of all
exit requirements, student identification cards and printing rights
are deactivated. The Information Technology department can help
students move their emails and files from the student ATS account
to their backup or storage account prior to the expiration date.
School Notification
Students are required to notify ATS whenever a change in personal
information occurs, such as a change of name, address, or
telephone number. Additionally, any anticipated changes in
attendance or any other item that may have an impact upon
completion of the student’s education should be reported to the
appropriate department at ATS Institute of Technology.
Professional Dress Code
The following guidelines have been established to meet the dress
requirements of the Practical nursing program.
Uniforms
Students are responsible to purchase uniforms and School patches
in order that they can be worn beginning the first day of classes.
Uniforms must be in the style approved by the school.
During Clinical, Classroom and Lab settings students are required
to wear royal blue uniforms with the School patch and ID badge
each day. A white lab coat is suggested for clinical.
For classroom and lab settings: shoes must be all-white nursing or
athletic shoes with an enclosed heel and toe.
Additional supplies may include a stethoscope, watch and any
other supplies requested by the faculty.
Students must wear the designated uniform shirt and uniform pants
whenever functioning in the student role. Plain white socks are to
be worn. Footies/no-show socks are not allowed, ankles must be
covered. The uniforms must be clean and neatly pressed.
No visible tattoos and body piercing (except earrings) are allowed.
Undergarments must not be visible (color or design). White tee
shirts should be plain without any design or words. Solid white
nursing shoes or white leather athletic shoes (without contrasting
colors) must be in good repair and always kept clean and polished.
All shoes must have no higher than a 1” heel and enclosed heel and
toe. Shoelaces are to be white only (refer to document “Care and
Maintenance of School Uniforms” in the Nursing Programs
Administrator’s Office).
One pair of small, ball-shaped pierced earrings may be worn in the
lowest part of the ear lobe (one per ear), if they are pearl, silver or
gold colored. A plain wedding band may be worn. No other
visible adornment is allowed. Neck and ankle jewelry is not
allowed. Hair must be off the collar and secured. Only white,
metal, neutral or tortoise-shell-colored clips are to be used to
secure the hair neatly off the collar. Neutral elastic scrunchies are
also permitted. No additional hair ornaments are allowed.
Students who choose to color their hair must keep to natural colors
only (no pink, blue, purple, etc.). Head coverings are permitted for
religious obligations only and must be white or conservative in
nature.
Students must be clean-shaven and/or have a neatly groomed
mustache/beard. Nails must not extend beyond fingertips.
Acrylic nails or nail polish are not allowed.
Nursing students must always adhere to this dress code. Students
who do not adhere to this dress code will be sent home and it will
be considered an unexcused absence for that day. Any make-up
fees are the responsibility of the student.
The thermostat is set to 72 degrees in the summer and 73 degrees
in the winter. Please dress appropriately.
20
| Page
If students are not in proper attire, they will be given a documented
Behavioral Violation. (see Discipline Policy)
Administrative Policies
Student Grievance and Appeal Procedure
It is the intent of the School to treat all students equitably according
to established School policies. This grievance and appeal
procedure is designed so that due process is followed and
satisfactory solutions can be reached.
Academic Appeals
A student may contest matters that affect academic standing. If
necessary, students may submit a written appeal. The Appeals
Committee will review facts related to the case and make a final
determination. Students may not submit an appeal for policy
change or academic dishonesty.
Students with an academic appeal in process must attend classes
as scheduled while the process is taking place according to their
schedule until further notice.
Appeals must be submitted within 5 days from the time the issue
occurred.
Final Grade appeals must be submitted within 5 days from when
the grade was posted in the student information system (SIS). This
applies only to the most recent semester completed.
Grievances
A grievance is defined as any situation or action personally
affecting a student that was a result of a violation, mishandling, or
misapplication of any specific provision stated in policy, rule,
statute, or regulation of the school.
Requests for reconsideration of decisions that affect a student’s
academic status in keeping with standing policies are not
grievances and should be handled through the appeals process.
Grievances must be submitted within two weeks of the occurrence
in question.
Grievance Steps:
● Meet with the person(s) directly involved and attempt to
resolve the problem.
● If there is no reasonable resolution, the student may proceed
with a grievance submission without fear of retribution.
● Grievances will only be accepted through the Grievance
Form on the school’s website: Grievance Form Link. Only
grievances submitted by the grievance link will be accepted.
● The grievance is reviewed and investigated by the
Program Administrator or Designee.
● The student may be contacted for further information or
details regarding the grievance.
● The student will be notified in writing (via ATS email)
confirming their grievance was received and
investigated.
Grievances that are not resolved on an institutional level may be
taken to the Accrediting Bureau of Health Education Schools
and/or the Illinois State Board of Higher Education.
Accrediting Bureau of Health Education Schools (ABHES)
7777 Leesburg Pike, Suite 314 North
Falls Church, Virginia 22043
(703) 917-9503
Private Business and Vocational Schools Division of the Illinois
Board of Higher Education
1 N. Old State Capitol Plaza, Suite 333
Springfield, IL 62701-1404
IBHE online complaint link and phone number:
http://complaints.ibhe.org/
(217) 782-2551
School Incidents
Students are requested to report any improper activity that they
observe on campus, online, or at clinical sites. This may include
theft, abuse of property or person, injury, or any unusual
occurrence. An online, Incident Report Form is available at the
ATS website, a printed copy is also available at the front desk.
Annual Security Report / Clery Act / Campus
Security
The ATS Annual Security Report contains information regarding
crimes reported to the US Education Department and security
policies of ATS Institute of Technology. This information is
updated annually, and a notice is sent to students and employees
of the report’s availability. A paper copy of this report is also
available upon request. The Annual Security Report can be viewed
at www.atsinstitute.edu.
Emergency Preparedness
Please see the “Emergency Preparedness Plan” which is located on
the school website,www.atsinstitute.edu. Periodic fire drills are
held. Directions for evacuation of the building are posted in each
classroom. Students are requested to evacuate in a quick and
orderly fashion if the evacuation alarm is heard.
CDC Universal Precautions to Decrease
Transmission of Disease
Health care students are at risk of contracting transmittable
diseases during patient care. Upon admission into the student’s
program, all students are required to abide by the Center of Disease
Control’s (CDC) Universal Precautions in order to decrease
transmission of disease. It is the student’s responsibility to become
thoroughly familiar with CDC Guidelines and to practice Standard
Precautions in all clinical/laboratory settings. Students are
required to comply with all Standard Precautions.
Standard precautions include:
● Hand hygiene.
● Personal protective equipment.
● Respiratory hygiene and cough etiquette.
● Cleaning and disinfection of devices and environmental
surfaces.
● Safe injection practices.
21
| Page
● Medication storage and handling.
Individuals may choose to wear face coverings and are supported
if they choose to do so. The School reserves the right to require
students to wear face coverings.
Attention to pregnant students: Infectious diseases have the
potential for hazardous effects on the developing fetus. Pregnant
students should consult their healthcare provider for safety
recommendations.
The School will continue to monitor CDC guidelines and update
policies and procedures based on the CDC recommendations.
Violation or Suspected Violations of Federal
Copyright Law
Copyright infringement is the act of exercising without permission
or legal authority, one or more of the exclusive rights granted to
the copyright owner under Section 106 of the Copyright Act (Title
17 of the United States Code). These rights include the right to
reproduce or distribute copyrighted work. In the file sharing
context, downloading, or uploading substantial parts of a
copyrighted work without authority constitutes an infringement.
Penalties for infringement may be civil and/or criminal including
fines and/or imprisonment. Additional information can be found at
www.copyright.gov.
Academic Freedom
ATS Institute of Technology endorses the American Association
of University Professors 1940 Statement of Principles on
Academic Freedom, and the College respects academic freedom
for faculty and students as well as freedom in their personal lives
for all individuals in the campus community.
Academic Honesty and Integrity
The School promotes the exchange of knowledge in an
environment that encourages intellectual honesty. Students must
maintain high standards of academic conduct.
A student's conduct must not interfere with the learning process of
any other student, the faculty/instructor, or the progress of the
class. Violation of the academic honesty and integrity standards
may include any and all types of academic fraud,
misrepresentation or cheating, and engaging in any online acts that
violate the End User Licensing Agreement.
Academic Fraud
Academic Fraud is any type of cheating or misrepresentation that
occurs in relation to any academic or attendance related
component.
Academic Fraud violations will result in the following:
First offense, students will need to meet with the retention
specialist and/or nursing coach to discuss. Second offense is a
dismissal.
● Plagiarism: The adoption or reproduction of code, ideas,
words, or statements of another person or author without
due acknowledgment.
o All parties to plagiarism are considered equally
guilty. If a student shares the student coursework
with another student and it is plagiarized, that
student is considered as guilty as the plagiarizer;
since that student enabled the plagiarism to take
place. Under no circumstances should a student
make the student coursework available to another
student unless the instructor gives explicit
permission for this to happen.
o Using charts, illustrations, images, figures,
equations, etc., without citing the source.
o Using an academic exercise (in whole or in part)
purchased or copied from a ghostwriter or
paper/essay mill.
o Copyright infringement or piracy, including the
use, alteration, or duplication of media, software,
code, or information when expressly prohibited or
where copyright exists or is implied.
Zero on assignment/test/academic work for first offense, any
multiple offenses are grounds for dismissal.
● Fabrication: The falsification of data, information, or
citations in any academic situation.
● Deception: Providing false information to a representative of
the School concerning an assignment, mock interview, or
class—e.g., giving a false excuse for missing a deadline
or falsely claiming to have submitted work.
● Collusion: Knowingly assisting, attempting to assist, or
receiving assistance from another student or students to
commit academic misconduct, or conspiring with any
other person in or outside of the University to commit
misconduct.
● Cheating: Any attempt to give or obtain assistance in any
class assignment(s) (like an examination) without due
acknowledgment.
Failure of the course
● Sabotage: Acting to prevent others from completing their
work.
● Destruction, Theft, Obstruction, Interference : Seeking to
gain unfair academic advantage by destroying, damaging,
or stealing equipment or products of any academic
exercise; or obstructing or interfering with an instructor's
materials or another student's academic work.
● Excessive signing in without physically attending or signing
in and leaving (without permission) before completion of
class, and/or class activities required may result course
failure.
Immediate Dismissal
● Falsifying Records and Official Documents: Forging
signatures or falsifying information on official academic
documents such as forms, petitions, signing into courses
under a false name/identity, letters of permission, or any
other official internal or external document.
When the faculty of record (or designee) identifies that an act of
possible misconduct has occurred, the instructor investigates the
occurrence. If the instructor concludes there is a violation of the
Academic Honesty and Integrity policy, the incident is reported to
the Academic Integrity Committee.
22
| Page
Investigation: Students are entitled to a full investigation. The
faculty/instructor will alert the Academic Integrity Committee and
Program Administrator who will investigate the policy violation
claim. Once the claim has been verified or unsubstantiated, the
parties involved will be informed in writing, via ATS email.
Compromised Test Policy
If an instructor thinks that a test has been compromised by any
factor at any point in time during the semester, that instructor has
the right to retest the entire class of students with a comparable
testing method. This includes standardized testing.
Title IX Compliance
The School’s Title IX Coordinator is responsible for the school’s
overall compliance with Title IX, including response to reports of
sexual misconduct affecting the campus community which include
sex and gender discrimination, sexual harassment, sexual assault,
and violence, stalking, domestic or dating violence and retaliation.
Examples of what constitutes sexual misconduct can be found in
greater detail online Title IX or a paper copy can be obtained from
the Title IX Coordinator.
Questions regarding the application of Title IX and the school’s
compliance with it should be directed to the Title IX coordinator.
The Title IX Coordinator is the Director of Nursing 312-300-0980
or [email protected] Students who wish to make a report of
sexual misconduct should follow published grievance procedures
available online www.atsinstitute.edu or a paper copy can be
obtained from the Title IX Coordinator.
Sexual Crimes and Prevention
ATS Institute of Technology is fully committed to complying with
Section 485(f) of the Higher Education Act of 1965 (Clery Act),
as amended by the Violence Against Women Reauthorization Act
(VAWA). Sexual offenses, including crimes of harassment,
assault, dating violence, domestic violence, and stalking are
prohibited. The policy regarding sexual crime prevention
programs and the procedures to be followed if such an offense
occurs is delivered annually to each enrolled student and employee
and can be provided upon request. ATS Institute of Technology
has a zero-tolerance policy for crimes of dating violence, domestic
violence, sexual assault, and stalking. This policy is also located at
www.atsinstitute.edu.
Student/Employee Fraternization
Employees of ATS Institute of Technology are prohibited, under
any circumstances, to date or engage in any fraternization or undue
familiarity with students, regardless of the student’s age and/or
regardless of whether the student may have consented to such
conduct. Further, employees may not entertain students or
socialize with students outside of the School environment.
Similarly, any action or comment by an employee which invites
romantic or sexual involvement with a student is considered highly
unethical, in violation of School policy, and may result in
disciplinary action by the School.
Inappropriate employee behavior includes, but is not limited to:
flirting; making suggestive comments; dating; requests for sexual
activity; physical displays of affection; giving inappropriate
personal gifts; frequent personal communication with a student
(via phone, e-mail, letters, notes, text messaging, social networks,
etc.) unrelated to course work or official School matters; giving or
accepting rides; giving or offering housing; selling or buying
anything even of nominal value; providing alcohol or drugs to
students; inappropriate touching; and engaging in sexual contact
and/or sexual relations.
We also expect that our students will behave in a professional
manner towards faculty and staff and will follow the same
guidelines as are presented here for employees. If a student
witnesses or hears of a School employee’s participation in an
inappropriate relationship with a student, we ask that the incident
be reported to the CEO, Program Administrator, or the Operations
Manager, immediately.
Privacy of Student Records
The Family Educational Rights and Privacy Act (FERPA) affords
eligible students certain rights with respect to their education
records. (An “eligible student” under FERPA is a student who is
18 years or older or who attends a postsecondary institution.)
These rights include:
1) The right to inspect and review the student’s educational
records within 45 days after the day ATS Institute of
Technology School receives a request for access. A student
should submit to the Registrar, a written request that
identifies the record(s) the student wishes to inspect. The
Registrar will make arrangements for access and notify the
student of the time and place where the records may be
inspected.
2) The right to request the amendment of the student’s
education records that the student believes is inaccurate,
misleading, or otherwise in violation of the student’s privacy
rights under FERPA. A student who wishes to ask the school
to amend a record should write to the school official
responsible for the record, clearly identify the part of the
record the student wants to be changed and specify why it
should be changed. If the School decides not to amend the
record as requested, the school will notify the student in
writing of the decision and the student’s right to a hearing
regarding the request for amendment. Additional
information regarding the hearing procedures will be
provided to the student when notified of the right to a
hearing.
3) The right to provide written consent before the school
discloses personally identifiable information (PII) from the
student’s records, except to the extent that FERPA
authorizes disclosure without consent. The school discloses
education records without a student’s prior written consent
under the FERPA exception for disclosure to school officials
with legitimate educational interests.
A school official is employed by the School in an administrative,
supervisory, academic, or support staff position (including law
enforcement unit personnel, regulatory entities, officials
designated by the Department of Education and health staff); or
serving on an official committee, such as a disciplinary or
grievance committee. A school official also may include an
outside contractor who is under the direct control of the School
with respect to the use and maintenance of PII from education
records, such as an attorney, auditor, or collection agent. A school
official has a legitimate educational interest if the official needs to
review an education record to fulfill the student professional
responsibilities for the School.

23
| Page
Upon request, the school also discloses education records without
consent to officials of another school in which the student seeks or
intends to enroll. ATS Institute of Technology will make
reasonable attempts to notify each student of these disclosures.
The right to file a complaint with the U. S. Department of
Education concerning alleged failures by ATS Institute of
Technology School to comply with the requirements of FERPA.
The name and address of the Office that administers FERPA is:
Family Policy Compliance
Office U. S. Department of Education
400 Maryland Avenue, SW Washington, DC 20202
Directory Information
FERPA permits the disclosure of education records, without the
consent of the student, if the disclosure meets certain conditions
found in the FERPA regulations. Except for disclosures to school
officials, disclosures related to some judicial orders or lawfully
issued subpoenas, disclosures of directory information, and
disclosures to the student, FERPA regulations require the
institution to record the disclosure.
Eligible students have a right to inspect and review the record of
disclosures. A postsecondary institution may disclose education
records without obtaining prior written consent of the student in
the following instances:
● To other school officials, including teachers, within the
school whom the school has determined to have legitimate
educational interests. This includes contractors, consultants,
volunteers, or other parties to whom the school has
outsourced institutional services or functions.
● To officials of another school where the student seeks or
intends to enroll, or where the student is already enrolled if
the disclosure is for purposes related to the student’s
enrollment or transfer.
● To authorized representatives of the U. S. Comptroller
General, the U. S. Attorney General, the U.S. Secretary of
Education, or State and local educational authorities, such as
a State postsecondary authority that is responsible for
supervising the school’s State-supported education
programs. Disclosures under this provision may be made, in
connection with an audit or evaluation of Federal- or State-
supported education programs, or for the enforcement of or
compliance with Federal legal requirements that relate to
those programs. These entities may make further disclosures
to outside entities that are designated by them as their
authorized representatives to conduct any audit, evaluation,
or enforcement of compliance activity on their behalf.
Disclosures may also be made in connection with financial
aid for which the student has applied or which the student
has received if the information is necessary to determine
eligibility for the aid, determine the amount of the aid,
determine the conditions of the aid, or enforce the terms and
conditions of the aid.
● To organizations conducting studies for, or on behalf of, the
school, in order to: (a) develop, validate, or administer
predictive tests; (b) administer student aid programs; or (c)
improve instruction.
● To accrediting organizations to carry out their accrediting
functions.
● To comply with a judicial order or lawfully issued subpoena.
● To appropriate officials in connection with a health or safety
emergency.
● Information the school has designated as “directory
information” may be released at the school’s discretion. The
School has defined directory information as the student’s
name, address, phone number, e-mail address (personal and
ATS assigned), birth date, enrollment status/grade level, date
of graduation and honors received, photos, major field of
study, dates of attendance, participation in officially
recognized activities and sports, most recent institution
attended, and student identification. If a student does not
want the student directory information to be released to third
parties without the student’s consent, the student must
present such a request in writing to the School within 45 days
of the student’s enrollment or by such a later date as the
institution may specify. Under no circumstance may the
student use this right to opt-out to prevent the institution
from disclosing that student’s name, electronic identifier, or
institutional e-mail address in a class in which the student is
enrolled.
● To a victim of an alleged perpetrator of a crime of violence
or a non-forcible sex offense. The disclosure may only
include the final results of the disciplinary proceeding with
respect to that alleged crime or offense, regardless of the
finding.
● To the general public, the final results of a disciplinary
proceeding if the school determines the student is an alleged
perpetrator of a crime of violence or non-forcible sex offense
and the student has committed a violation of the school’s
rules or policies with respect to the allegation made against
him or her.
● To parents of a student regarding the student’s violation of
any Federal, State, or local law, or of any rule or policy of
the school governing the use or possession of alcohol or a
controlled substance if the school determines the student
committed a disciplinary violation and the student is under
the age of twenty-one.
No information will be released to any person(s) on the telephone
or via email.
Drugs and Alcohol Abuse Prevention Policy
ATS is committed to a safe, healthy, and productive environment
for all students and employees free from the effects of substance
abuse. All new students and employees are provided the access to
ATS Drug and Alcohol Abuse Prevention Policy upon enrollment/
employment. This policy is also distributed annually to all active
students and employees. The policy in its entirety can be provided
by paper copy upon request, or at www.atsinstitute.edu.
The purpose of this policy is to inform students/employees about
the guidelines related to any unlawful use, manufacture,
distribution, or possession of controlled or illegal substances or
alcohol. Aside from seriously affecting the physical and
psychological integrity of the user, substance abuse may
significantly affect the ability of students to administer safe care to
patients entrusted to them in a clinical health care setting.
Drug Testing Policy
A positive drug screen of any substance tested (federal illegal
substance, or controlled substance without a prescription) or noted

24
| Page
impairment may result in suspension for the remainder of the
semester and a referral to counseling.
Students must complete counseling requirements and submit to an
additional drug screen prior to returning to the program of study.
Failure to attend counseling requirements and/or an additional
positive drug screen may be cause for dismissal from the student’s
program of study.
Any additional positive drug screen or noted impairment after
completing counseling requirements will be an immediate
dismissal from the program.
Students may also be selected for random drug testing at any time
and specifically when being under the influence is suspected.
Reasons to suspect substance use include, but are not limited to:
1. Noticeable change in behavior
2. Slurred speech
3. Smell of ethanol on breath
4. Smell of marijuana on person
No students under the influence of alcohol or other drugs will be
allowed to attend class, remain at the School facility, or attend
clinical. Students taking controlled medications that are prescribed
for a legitimate reason must provide documentation for it from the
health care provider within five days (federal illegal substances do
not apply). Failure to comply with this will indicate a positive
finding for the drug screening with possible dismissal from the
program.
Failure or refusal to comply with any aspect of the substance abuse
guidelines may impact academic progression. Examples of
noncompliance include, but are not limited to, refusal to submit to
immediate drug and alcohol testing or repeat testing, tampering, or
altering of specimens, attempts to submit the samples of another
person as the student’s own, and failure to appropriately complete
associated program or testing laboratory documents.
Any unlawful possession, use, or distribution of illicit drugs or
alcohol, whether by students or employees, will be reported to the
local police department. The student is responsible for any legal
penalties resulting from the possession or distribution of illicit
drugs including confiscation of personal possessions, fines, and
incarceration.
Students that are dismissed due to failing to complete required
counseling (following a positive drug screen) will not be allowed
to reapply. Students with more than one positive drug/alcohol
testing will be allowed to reapply after successful completion and
documentation of a substance abuse treatment program. Students
dismissed due to refusal to comply with the testing requirements
will not be allowed to reapply to the program. Students dismissed
due to possessing any unlawful drug while on campus will not be
allowed to reapply to the program.
Program Costs & Financial Aid
Students seeking financial assistance to meet the cost of education
are encouraged to contact the Financial Aid Office and the Bursar
Office. A variety of grants, scholarships, and loans are available
for students who qualify based on financial need, enrollment, and
satisfactory academic progress. An Award Notification letter will
be sent to the student indicating the type and the amount of aid
awarded once eligibility is determined.
Financial Aid and Bursar services are available by appointment.
Student Financial Assistance
During a student financial aid appointment, the financial aid
advisor provides the student with a financial estimate that outlines
estimated financial aid based on the student's eligibility. ATS
provides students who are expected to pay out of pocket expenses
with payment plan options. If students have questions about
methods of payment or need to modify their payment
arrangements, they may contact the Bursar's office.
Equal Standards
All students attending ATS must adhere to the same standards.
This includes students receiving Federal Title IV funds and those
not receiving such funds. All students must maintain the same
institutional/program grade, attendance, behavior, admission, and
drug-free requirements. All students have the right to appeal
decisions made by the school.
Definitions related to Federal Financial Aid
Consumer Information
The Higher Education Opportunity Act of 2008 (HEOA) requires
that postsecondary institutions participating in federal student aid
programs disclose information from various administrative areas
to students. Consumer Handbook contains consumer information
and is available on the school website: www.atsinstitute.edu
Payment Periods
Financial Aid will be disbursed at the beginning of each payment
period (PP) that is equivalent to the semester.
Federal Clock Hour to Credit Hour Conversion
Financial Aid Credit for ATS courses is calculated as follows: 30
clock hours = 1 semester credit hour. Recognized outside hours not
included in clock hours for calculating the financial aid credits.
The Practical Nursing program consists of 39.3 financial aid
credits. Students enrolled in Developmental courses may acquire
up to 7.50 additional financial aid credits.
Full-time financial aid status definition
Students who attempt 12 financial aid credit hours per semester
will be qualified as full-time students
Students attempting less than 6 financial aid credits are not eligible
to participate in Title IV Direct loan funding.
Determination of Withdraw Date
Official Withdrawal – the date the student initiates the
withdrawal process.
To initiate the withdrawal process, students may submit the
Withdrawal form, call to the corresponding office, send an email,
25
| Page
submit a written request by mail or orally in person to the Student
Services, Program Administrator, Bursar, or Financial Aid
Office.
A student who contacts the school and only requests information
on aspects of the withdrawal process, such as the potential
consequences of withdrawal, would not be considered a student
who is indicating that he or she plans to withdraw.
Administrative Withdrawal – no official notification from
student
1. If the college administratively withdraws a student, the
withdrawal date will be the date of the event that caused the
school to make that decision to withdraw the student.
2. If the college administratively withdraws a student because
all of the student’s instructors report that the student has
ceased attendance at the end of the second week of the
semester, the withdrawal date will be the end of the second
week.
3. If all student’s instructors report that student attendance
jeopardizes progress in their course and recommends to
withdraw the student from the course, then the withdrawal
date for that student will be the last date a student
participated in an academically related activity.
Unofficial Withdrawal
The last date of an academically related activity in which the
student participated will be used as a Withdrawal date.
Standards of Satisfactory Academic Progress
(SAP)
Satisfactory Academic Progress (SAP) is defined as the successful
progression through an academic program. Every student must
maintain SAP to remain eligible to receive federal financial aid.
For federal financial aid eligibility purposes, SAP will be
evaluated at the end of each semester. These standards of
satisfactory academic progress apply to all students, not just those
receiving federal financial aid.
Minimum Standards
All students are expected to meet the minimum standards of SAP
required for the program of study. SAP is measured in two ways:
1. Quantitative - Rate of Progress (Pace)
A student must maintain the minimum Pace requirements at
specific points throughout the program. The rate of progress
percentage is calculated by dividing the credits earned by the
credits attempted. For the purposes of calculating SAP the clock
to credit conversion formula is used.
2 Qualitative- Cumulative Grade Point Average (CGPA)
Students must meet minimum CGPA requirements at specific
points throughout the program. Only those credits required in the
student’s program of study are used in the CGPA calculation.
For a student to be considered making academic progress, all SAP
standards will be reviewed at the end of each semester, and the
student must be progressing in accordance with the table below.
Credits
Attempted
Rate of Progress
(Pace)
CGPA
(Qualitative)
0-20
66.67%
1.25
21-35.5
66.67%
2.0
36+
66.67%
2.0
Incomplete Grade
Courses, which are marked with a “I” at the end of the semester
are not included in calculation of the GPA but are included in
credit hours attempted and credit hours earned when calculating
SAP. Once the “I” grade is changed, the SAP will be reevaluated.
Withdraw Grade
Courses, which are marked with a “W,” are not included in
calculation of the GPA, but are included in credit hours attempted
and credit hours earned when calculating SAP.
Repeated Courses
Repeated courses will be added to total credit hours attempted and
credit hours earned. The initial grade once a repeated class has
been passed will be included in the CGPA calculation (this will
apply beginning for courses failed in Fall 2022 semester). If
repeating the course, the length of the program must not exceed
150 percent.
Transfer Credit
Transfer credit awarded by the college does not affect the CGPA
for SAP. Transferred credit hours, which count toward the
student’s current diploma program, will be included in credit hours
attempted, credit hours earned, and maximum timeframe.
Readmitted Students
Previous credits which count toward the student’s current program
will be included in credit hours attempted, credit hours earned,
GPA, and maximum timeframe.
Maximum Time Frame
Students are expected to complete their program within 150
percent of the published length of the program (or 1.5 times the
number of financial aid credits in their program). Pace calculations
help assure that students will complete their programs within the
maximum time frame.
At the end of each semester the school will evaluate whether it is
possible for the student to complete the program within the
maximum timeframe. Students fail the maximum timeframe
measure at the point at which it is determined that it is not possible
for them to complete their program within the maximum
timeframe, not at the point they actually reach the maximum
timeframe.
If at the time of the SAP evaluation, the student is not meeting
maximum timeframe/hours standards, s/he is no longer eligible to
receive financial aid assistance and may submit a Financial Aid
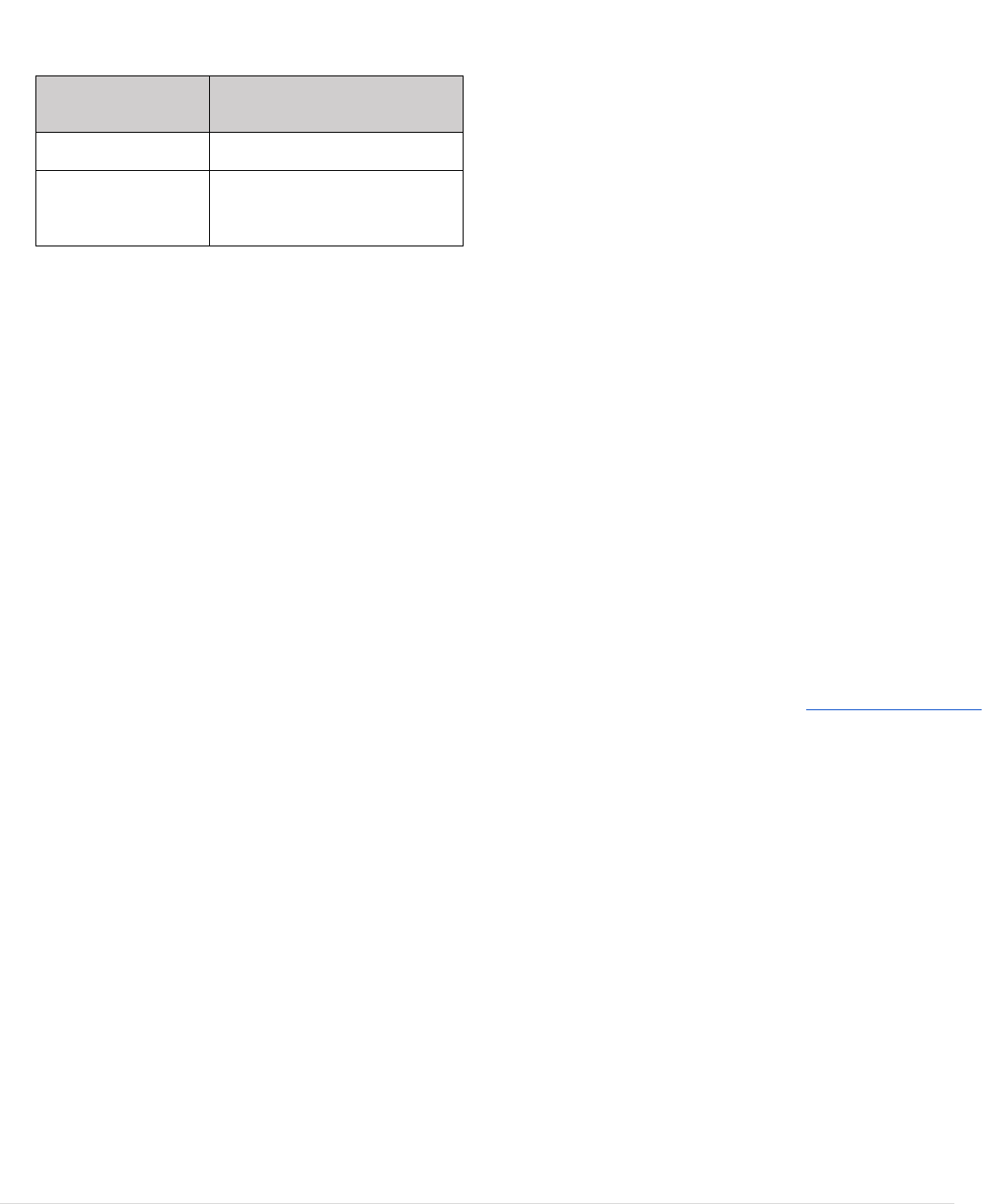
26
| Page
Appeal Process for reconsideration of their eligibility for Title IV
funds.
Program
Maximum Federal Aid
Credits
Practical Nursing (PN)
58.95 = (39.3x1.5)
Practical Nursing (PN)
when developmental
courses taken*
Will be based on number of
credits taken but no more than
70.2 = (46.8x1.5)
Note: Developmental courses will increase the maximum
timeframe for the attempted credits allowed. Developmental or
remedial coursework are counted as attempted and earned for
PACE and Maximum Timeframe.
Warning, Suspension and Probation Periods
Financial Aid Warning
This status is assigned to students who fail to meet minimum Pace,
CGPA, and/or maximum timeframe as stated above and who met
SAP at the prior semester of enrollment. Students will be notified
in writing by email of a Financial Aid Warning Status. While in
Financial Aid Warning the student will remain eligible to receive
federal financial aid for one semester.
If the student meets or exceeds the standards the following
semester, the student will be considered to meet SAP
requirements.
Students on Financial Aid Warning who fail to meet the standards
in the next semester are ineligible for federal financial aid and will
be placed on Financial Aid Suspension. The student may file an
appeal. If approved the student will be placed on Financial Aid
Probation.
Financial Aid Suspension
If a student fails to achieve minimum GPA, Pace, and/or maximum
timeframe standards while on a Financial Aid Warning status, the
student will be placed on Financial Aid Suspension for the
following semester. These students will not be eligible for any
federal financial aid until all requirements for minimum GPA
and/or Pace standards are met. Students will be notified in writing
by e-mail of a Financial Aid Suspension Status.
If the student meets or exceeds the standards the following
semester, the student will be considered to meet SAP
requirements.
Students on Financial Aid Suspension who fail to meet the
standards in the next semester will continue to be ineligible for
federal financial aid and remain on Financial Aid Suspension.
Any student who has been placed on Financial Aid Suspension
may submit a Financial Aid appeal for reconsideration of their
eligibility for Title IV funds, if special or mitigating circumstances
exist.
Financial Aid Probation
This status is assigned to students who were placed on Financial
Aid Suspension and have successfully appealed. During the
probationary period, students are given one semester to
satisfactorily raise their cumulative GPA and/or cumulative earned
credits, as required by SAP policy. While in Financial Aid
Probation the student will remain eligible to receive federal
financial aid for one semester from the date the appeal is approved.
Students will be notified in writing, by email, of a Financial Aid
Probation Status. A student that has progressed to Financial Aid
Probation will be moved to SAP Met if the student proceeds to
meet or exceed the standards in the following semester. Students
on Financial Aid Probation who fail to meet the standards outlined
above in the next semester are ineligible for federal financial aid
and will be moved to Financial Aid Suspension.
If an appeal is approved and it is determined that the student will
require more than one semester to meet progress standards, a
student will be placed on probation with an academic plan. The
student’s progress will be reviewed at the end of each semester of
the academic plan, to determine if the student is meeting the
requirements of the academic plan. The student is eligible to
receive Title IV aid as long as the student continues to meet those
requirements and is reviewed according to the requirements
specified in the academic plan. If a student does not meet the
academic plan, the student may appeal to change their plan. They
must explain what has happened to make the change necessary and
how they will be able to make academic progress. If the appeal is
approved, the student will remain on Financial Aid Probation. If
the appeal is denied, the student will move to Financial Aid
Suspension status.
Students on Financial Aid Probation are required to participate in
any advising and tutoring that are considered to be necessary by
the college.
Financial Aid Appeal Process
All appeals must be submitted on the Financial Aid appeal form.
All appeals must be accompanied by supporting documentation
that explains the circumstances which affected their academic
performance, and how the circumstance has been resolved so it
will not have any future effect on the student’s academic progress.
The decision of the college is final and may not be further
appealed.
Mitigating Circumstances
Mitigating circumstances are considered unforeseen situations or
events beyond the student’s control which directly and negatively
affect academic performance. For Financial Aid appeals, students
are required to provide supporting documentation for mitigating
circumstances. The appeal must also explain how the
circumstances have been resolved so that these circumstances will
not affect future performance.
Below is a list of possible circumstances and the suggested
documentation needed to substantiate the mitigating circumstance.
Please note, the following list is not exhaustive. If a student is
providing circumstances and documentation not mentioned below,
the appeal will be considered just the same. Additionally,
providing a mitigating circumstance with supporting
documentation from the list below does not guarantee an approval.
All appeals are reviewed on a case-by-case basis for legitimacy
and merit.
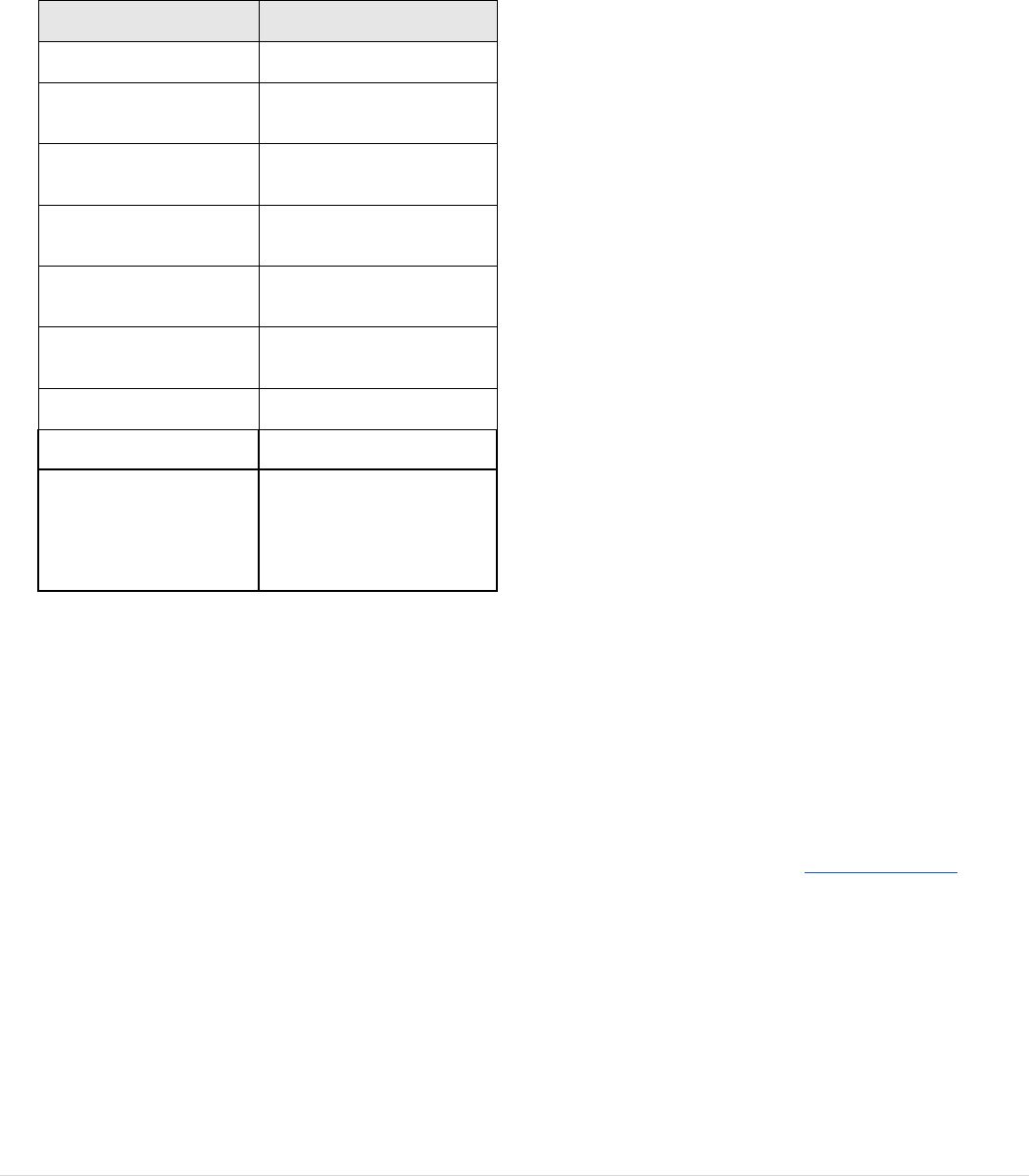
27
| Page
Acceptable documentation will be on official letterhead and
obtained through an objective third party. Objective third parties
include, but are not limited to: counselors, doctors, lawyers, social
workers, religious leaders, state/government agencies, etc.
Possible Circumstances
Suggested Documentation
Death in the family
Death certificate, obituary
Domestic violence
Court documents, restraining
orders, police records
Crime victim
Legal documentation, police
records
Physical and/or mental
illness
Documentation from medical
professional
Imposed employment
changes
Statement from employer
Involuntary call to military
service
Official military orders
Jury duty/court appearance
Court documents
Medical issue of family
member in which the
student has to become a
part-time or full-time
caretaker
Supporting documentation
from a healthcare provider
and/or attorney
To begin the appeal process, the student must submit
● Financial Aid appeal Form,
● a letter from the student,
● and supporting documentation must be submitted for
consideration.
The Financial Aid appeal Form is available on the ATS website.
The Financial Aid Appeal must be submitted within 7 days of the
Financial Aid Suspension notice. Not all appeals are approved, and
deadlines do apply. The Appeals Committee will review appeals
on an individual basis and contact the student via email with the
final decision.
Extended Enrollment Period
A student who has been placed on Financial Aid Suspension is in
an extended enrollment status and is not eligible for additional
financial aid and is responsible for making financial arrangements
with the institution for tuition and fees incurred during the
extended enrollment period. Students attending in an extended
enrollment period will be charged tuition and fees consistent with
stated costs. The credits attempted and earned in this period will
count toward student evaluation for attempted and
earned/completed credits (PACE/Maximum Timeframe).
During the extended enrollment period, students must seek to
correct academic deficiencies by retaking courses they have failed
in order to reestablish satisfactory progress.
Reinstatement of Financial Aid Eligibility
In order to regain financial aid eligibility, a student must
successfully meet all requirements for satisfactory academic
progress. At the completion of the extended enrollment period, the
Financial Aid officer will evaluate student performance in the
following areas:
● Completion of at least 66.67% of the attempted cumulative
hours as calculated and
● Achievement of the cumulative GPA as required by the
College
● Ability to complete a program within a maximum time
frame;
After this determination the student’s award package will be
generated based on funds available at that time. Federal financial
aid will not be given to students retroactively.
Student Financial Aid Sources
Federal Application for Federal Student Aid
(FAFSA)
The FAFSA is a federal government application used to determine
a student’s eligibility for federal financial aid. The FAFSA asks
for general information about the student (and parent or spouse)
including financial and tax information.
The form can be completed as early as October 1 for the upcoming
academic year. The FAFSA must be completed each year the
student intends to receive federal financial aid.
Federal Pell Grant Program
The Federal Pell Grant is given with no repayment expected. This
program is designed to provide a “floor” upon which other
financial aid programs are built. Any student wishing to receive a
Federal Pell Grant at this institution must meet the eligibility
requirements established by the U.S. Department of Education.
The amount of the award depends upon the determination of the
student’s eligibility, the student enrollment status, cost of
attendance, and a payment schedule issued by the U.S. Department
of Education.
To receive a Federal Pell Grant a student must complete the Free
Application for Federal Student Aid (FAFSA). The FAFSA may
be completed on-line at: https://studentaid.gov, or a paper
application may be used. FAFSA forms are available in the
Financial Aid Office, from high-school counselors, or other public
places such as a library.
Federal Supplemental Educational Opportunity
Grant (FSEOG)
Each year the school makes a limited number of awards to students
through the FSEOG program. These funds are reserved for
students who qualify based upon exceptional financial need. The
financial aid advisor determines who will receive an FSEOG and
the amount awarded, based on need, not to exceed the program

28
| Page
maximum. Please consult your financial aid advisor for more
information on FSEOG.
Federal Direct Subsidized Loan
A Federal Direct Subsidized Loan is awarded based on need The
federal government pays the interest while the borrower is in
school, during the grace period and during authorized periods of
deferment. Repayment will begin six months after the borrower
ceases to be enrolled in the program. . A student may be eligible to
request a maximum of $3,500 per year.
Federal Direct Unsubsidized Loan
A Federal Direct Unsubsidized Loan is not awarded based on need.
The borrower is charged interest from the time the loan is
disbursed until it is paid in full. In addition, until repayment begins
and during authorized periods of deferment, the borrower has the
option to pay the interest or allow the interest to accumulate.
Repayment will begin six months after the borrower ceases to be
enrolled in the program.
A dependent student may be eligible to request $5,500 (less any
subsidized eligibility) in their first year and $6,500 (less any
subsidized eligibility) in their second year.
An independent student may be eligible to request $9,500 less any
subsidized eligibility in their first year and $10,500 less any
subsidized eligibility in their second year.
Federal Parent Loan to Undergraduate Student
(PLUS)
A Federal Parent PLUS loan is not based on need. Approval for
this loan is determined by the Department of Education and is
based on the parent’s credit score. Parents may be eligible to
request up to the cost of attendance, minus any other aid received
by the student. Repayment will begin approximately sixty days
after the final loan disbursement is made. The maximum
repayment period is ten years. The FAFSA application is not
required to apply for a Parent PLUS loan.
If the PLUS Loan is not approved, the student may borrow
additional unsubsidized Federal Direct Student Loan funds.
Entrance Counseling
Students are required to complete Federal Student Loan Entrance
counseling prior to borrowing a Federal Direct Subsidized or
Unsubsidized loan. The entrance counseling session
(approximately 20 minutes) will ensure the student understands the
loan terms and conditions and their rights and responsibilities as a
federal student loan borrower.
Entrance counseling can be completed at
https://studentaid.gov/entrance-counseling.
Master Promissory Note (MPN)
The MPN explains the terms and conditions of the student/parent’s
loan(s). It is a legal document in which the student/parent promises
to repay the loan, accrued interest and fees to the U.S. Department
of Education.
The MPN can be completed at https://studentaid.gov/mpn.
Student Loan Exit Counseling
Student Loan Exit counseling ensures the student understands their
student loan obligations and prepares the student for repayment.
Student Loan Exit counseling must be completed by all federal
student loan borrowers when the borrower leaves college,
graduates or drops below half-time enrollment. During the
counseling session you will learn what your federal student loan
payments will look like; review recommended repayment
strategy(s) that best suits your future plans and goals.
Student Loan Exit Counseling can be completed at
https://studentaid.gov/exit-counseling. To complete exit
counseling, you will need your Studentaid.gov login information,
our college’s name, and your updated contact information.
You may schedule an appointment to meet with the financial aid
advisor to complete the exit counseling requirement.
Student Loan Repayment
Before repayment begins, develop a plan that puts you on track to
pay back your loan on time and in full. You have a six-month grace
period before you are required to start making regular payments.
You will have a nine-month grace period if you have got a Perkins
Loan. (Got a PLUS loan? You will go into repayment as soon as
the loan is fully disbursed—which means once it is paid out.
Go to https://studentaid.gov/manage-loans/repayment to learn
about:
● What repayment plan options are available.
● When you must begin making payments.
● How to make your payment.
● How to pay off your loan faster.
● What to do if you have trouble making payments.
Veteran Student Benefits
The School conducts under a hybrid program and is no longer
approved as an institution of higher learning for the training of
veterans and veterans’ dependents entitled to educational
assistance. All policies related to those services have been
removed and are no longer valid.
Scholarships
The Presidential Scholarship
The Presidential Scholarship is a merit-based award that pays up
to $2,370 tuition ($790 per nursing semester) for those prospective
students who enter ATS as a new full-time 1st semester nursing
student (semester without developmental classes). This
scholarship does not need to be repaid and eligibility is reviewed
each semester based on Eligibility Criteria for Scholarship
Continuation below.
Recipients are identified upon entering ATS by meeting all of the
following criteria:
● New students who are not enrolled in any developmental
courses.
● Entering as a 1st semester nursing student
Minimum Eligibility Criteria for The Presidential
Scholarship Continuation
The student must maintain:

29
| Page
● A minimum 3.0 grade point average in the previous
semester.
● Meet Satisfactory Standards of Professional Conduct.
● Register and complete a Full-time academic schedule for the
semester where the scholarship is applying.
If the minimum criteria are not met, the student scholarship will be
terminated. The scholarship can be reinstated if the student meets
the minimum criteria in the following semester(s).
Recipients who meet the minimum criteria at the end of their final
semester may receive the scholarship retroactively (if the amount
does not exceed maximum scholarship amount).
The Bursar will review the recipient's continued or reinstated
eligibility at the end of each semester.
Presidential Scholarship Deferment (Leave of
Absence/Emergency Leave)
If a student, who has been awarded a scholarship, takes an
approved leave of absence or emergency leave, the scholarship
will be placed in deferment for the following semester (if student
has not returned). If the leave is greater than one semester, the
student scholarship will be terminated.
The ATS Scholarship
The ATS Scholarship is a merit-based award that pays $500 per
nursing semester for those students who entered ATS as a new full-
time 1st semester nursing student (semester without
developmental classes) and did not meet the “Minimum Eligibility
Criteria for The Presidential Scholarship Continuation”, but did
meet the minimum eligibility criteria listed below. This
scholarship does not need to be repaid and eligibility is reviewed
each semester based on Eligibility Criteria for Scholarship
Continuation below.
Recipients are identified by meeting all of the following criteria:
● Students who are entered as new full-time 1st semester
nursing students and were not enrolled in any developmental
courses.
● Received the Presidential Scholarship in their 1st nursing
semester
● A minimum 2.5 grade point average (by semester)
Minimum Eligibility Criteria for The ATS Scholarship
Continuation
The student must maintain:
● A minimum 2.5 grade point average in the previous
semester.
● Meet Satisfactory Standards of Professional Conduct.
● Register and complete a Full-time academic schedule for the
semester where the scholarship is applying.
If the minimum criteria are not met, the student scholarship will be
terminated.
The ATS scholarship can be reinstated if the student meets the
minimum criteria in the following semester(s). A student who
qualifies for the ATS Scholarship and regains eligibility for the
Presidential scholarship, will be reinstated in the scholarship with
the higher amount. A student is not eligible to receive both the
Presidential and ATS scholarships simultaneously
The Bursar will review the recipient's continued or reinstated
eligibility at the end of each semester.
Career Advancement Scholarship
ATS will match your Employer Tuition Reimbursement program
up to $2,000. This scholarship is limited to STNA’s/CNA’s who
want to continue their education and become an LPN nurse. ATS
is offering this scholarship towards educational expenses for
students who have completed a state-approved nurse aide training
program and are currently working at a healthcare facility.
Verification Requirements:
● Letter of employment from current employer.
● Letter of reimbursement guarantee from the employer.
Eligibility:
● Acceptance into the ATS Practical Nursing program.
● Proof of completed state-approved nurse aide training program.
Minimum eligibility criteria for scholarship continuation:
● Cumulative GPA of 2.0 on a 4.0 scale
● Enrollment of one or more subjects per semester
A student may apply for this scholarship any time during the
semester.
Nursing Scholarship
ATS will match your Employer Tuition Reimbursement program
up to $1,000. ATS is offering this scholarship towards educational
expenses.
Verification Requirements:
● Letter of employment from current employer.
● Letter of reimbursement guarantee from the employer prior to
beginning of the semester.
Eligibility:
● Acceptance into the ATS program.
Minimum eligibility criteria for scholarship continuation:
● Cumulative GPA of 2.0 on a 4.0 scale
● Enrollment of at least one subject per semester
A student may apply for this scholarship any time during the
semester.
Financial Procedures and Policies
Payment Requirements
Payment in full for semester tuition and any assessed fees is due
by the end of the first day of classes. The payment plan may be
requested with the Bursar office. Financial Aid and Bursar services
are available by appointment.
Minimum Payment Requirements
1) Financial aid application processed by the Department of
Education and on file at the School. Students MUST finish
financial aid verification, if any.

30
| Page
2) Full payment (payment must be received and posted to your
student account by the due date).
3) Good standing in the installment payment plan.
4) Confirmation of payment in the form of scholarships and/or
third-party authorization.
Students are required to monitor their account balances.
All payment concerns/disputes are to be discussed directly with the
Bursar’s office. If a student disputes charges with their bank and a
chargeback occurs, the student is responsible for immediately
recovering the charge back payment and providing a written
statement to the Bursar’s office explaining intentions to honor the
disputed payment. The student must continue to follow minimum
payment requirements. Intentional and/or excessive disputes and
chargebacks may lead to dismissal from the program.
Students who are 15 days past due with payment will be counseled
by school officials and may be pulled from classes. Students who
do not meet the minimum payment requirements listed above after
30 days, may be placed on financial suspension until they clear
their balance.
Payment Options
Tuition Installment Payment Plan
For students requiring more time to pay tuition, they may enroll in
an installment payment plan. The Financial Aid Office will
provide a financial estimate with your expected remaining out of
pocket balance. Students can choose the installment payment plan
or pay 50% of the semester tuition during the first week of classes
with the balance of the remaining 50% of semester tuition to be
paid by the end of the mid-term week. All financial requirements
need to be completed and the first payment paid during the first
month of classes. A $10 late fee will be charged after 30 days past
due.
Financial Billing Agreements
All billing agreements must be in place before the semester starts.
Please consult with your Financial Aid Advisor to confirm that the
school received certifications from the expected agencies.
The School will bill employers who pay tuition for their
employees. Students are to provide the School with a signed letter
of financial guarantee from the employer prior to registration for
classes.
Students who have applied for scholarships must inform the
Financial Aid Office in writing of the amount of the anticipated
scholarship. Approval letters need to be presented before the
beginning of the semester to apply funds to the upcoming semester.
Financial Suspension
During a Financial Suspension students will continue to attend
courses and complete assignments, tests, and quizzes as scheduled.
The student will not receive any grades during the Financial
Suspension. Grades may be restored once the suspension is
cleared. Suspension can lead to termination if a student does not
bring account current within 14 days of the initial suspension date.
Financial Holds
Holds may be placed on a student’s record whenever that student
is delinquent or has failed to pay any debt owed to the School or
failed to return any School property or equipment. Grades,
registration for next semester, transcripts, diplomas, letters of
completion or application to state boards and letters of
recommendation will be issued only when a student’s account is
considered to be in good standing.
Students that did not fulfill their financial obligations during the
previous semester will lose their eligibility to continue with the
installment payment plan until they clear previous obligations.
The School reserves the right to reject the enrollment of any
applicant who had formerly enrolled in a program at the school but
failed to fulfill payment requirements.
Duplicate Check Cashing
In the event a student receives a check from the ATS accounting
office and the check was cashed twice, without authorization, the
following consequences will occur:
● The student will receive a write up for the incident in an
incident report. And may be subject to dismissal from the
program.
● The student will be charged a penalty fee in lieu of filing a
police report against the student for Check Fraud.
● The student will immediately repay ATS all associated fees
and no further accommodations will be made.
ATS Institute of Technology reserves the right to file a police
report against said student for Check Fraud if the student is not in
compliance with the list above.
Right to Cancel
The Enrollment Agreement does not constitute a contract until an
official of the school has approved it. If the school does not accept
the Agreement, all monies paid will be refunded. The student has
the right to cancel the initial enrollment agreement until 5 business
days after the student has been admitted. If the right to cancel is
not given to any prospective student at the time the agreement is
signed, then the student has the right to cancel the agreement at
any time and receive a refund on all monies paid to date within 45
days of cancellation. Cancellation should be submitted to the
authorized official of the school in writing.
Refund Policy
If a student withdraws or is dismissed from the student program,
or if the enrollment agreement or application is otherwise
terminated, a refund will be issued according to the following
schedule:
● A student who withdraws before the first class and after the
5-day cancellation period shall be obligated for any non-
refundable 3
rd
party service fees used through ATS Institute.
● A student who starts class and withdraws during the first full
calendar week of the academic term, after completion of the
first day of classes, shall be obligated for twenty-five percent
of the tuition and refundable fees for that academic term plus
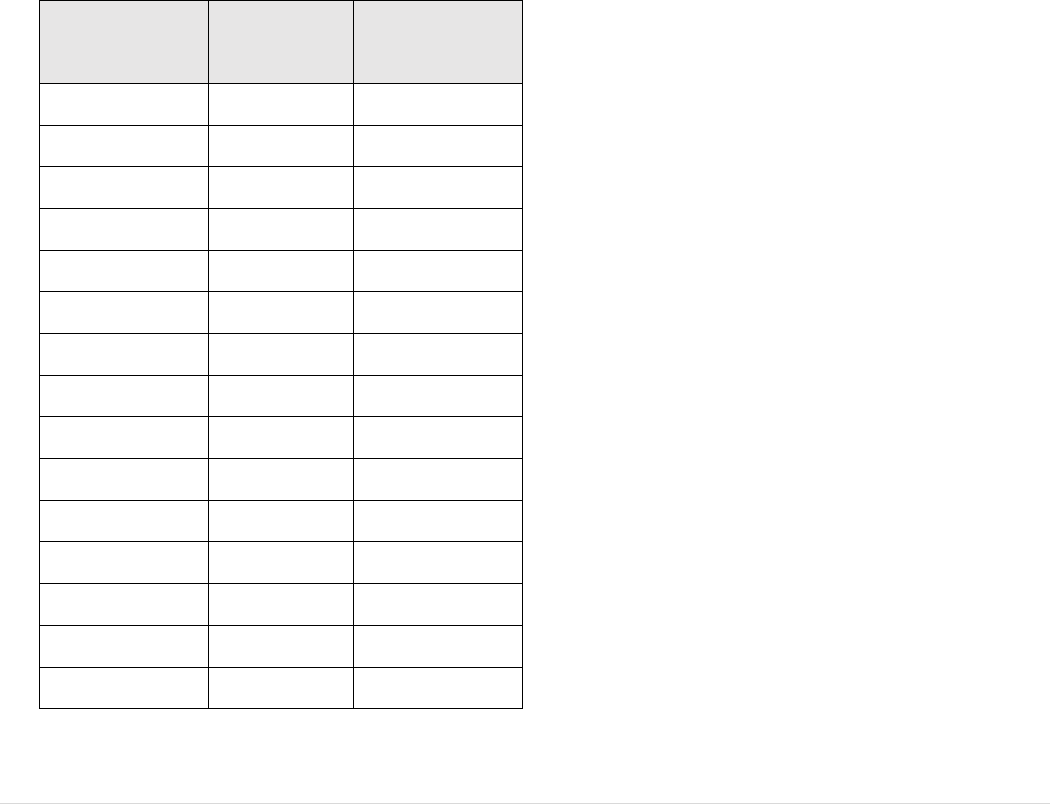
31
| Page
any non-refundable 3
rd
party service fees used through ATS
Institute.
● A student who withdraws the second full calendar week of
the academic term shall be obligated for fifty percent of the
tuition and refundable fees for that academic term any non-
refundable 3
rd
party service fees used through ATS Institute.
● A student who withdraws during the third full calendar week
of the academic term shall be obligated for seventy-five
percent of the tuition and refundable fees for that academic
term plus any non-refundable 3
rd
party service fees used
through ATS Institute.
● A student who withdraws beginning the fourth full calendar
week of the academic term will not be entitled to a refund of
any portion of the tuition and fees.
The school shall make the appropriate refund within 45 (forty-five)
days of the date the school determines that a student has withdrawn
or has been dismissed from a program. Refunds shall be based
upon the withdrawal date
In the case of documented student illness or accident, death in the
family, or other circumstances beyond the control of the student,
the student will be entitled to special consideration that may be less
than that stated by the refund policy.
Week
Withdrawal
Occurred
% of Term
Enrolled
Institution
Refund Policy
1
7%
75%
2
13%
50%
3
20%
25%
4
27%
0%
5
33%
0%
6
40%
0%
7
50%
0%
8
53%
0%
9
60%
0%
10
67%
0%
11
73%
0%
12
80%
0%
13
87%
0%
14
93%
0%
15
100%
0%
Refunds for books, fees, computer software and supplies:
Charges for required purchase of books, fees, computer software,
and supplies can be non-refundable if the student has consumed or
used the books, fees, computer software and/or supplies.
Consumption of books, fees, computer software, and supplies
defined as follows:
● Items that were special ordered for a particular student and
cannot be used by or sold to another student; or,
● Items that were returned in a condition that prevents them
from being used by or sold to new students.
● Documented non-refundable fees for goods or services
provided by third party vendors.
● Semester Course fees after the student receives a clinical
assignment.
A record of the refund determination for books, fees, computer
software, and supplies shall be kept in the student's record.
Refund policy for Indiana residents, See Appendix P: Indiana
Refund Policy.
Credit Balance
Students with a credit balance resulting from federal financial aid
will be refunded within fourteen (14) days of aid being credited to
the student’s account. The Bursar office processes refund checks.
Refunds are placed in the US Mail and addressed to the address on
file with the school. Students may update their address in writing
to the Registrar’s Office.
Return of Title IV Funds (R2T4)
General Requirements
If a recipient of federal financial aid withdraws from a school after
beginning attendance, the school performs an R2T4 calculation to
determine the amount of federal financial aid earned by the
student.
Federal law specifies how a school must determine the amount of
Federal Financial Aid (Pell Grant, FSEOG and Federal Direct
Loans) a student earned if they withdraw* before completing at
least 60% of each semester. If a student withdraws on or before
the 60% point in time, a portion of the federal financial aid
awarded to a student is returned within 45 days of the date the
school determines the student has withdrawn. For a student who
withdraws after the 60% point-in-time, there are no unearned
funds. However, a school will still determine whether the student
is eligible for a post-withdrawal disbursement (PWD) (see below).
*Withdrawal on the date of the student’s last documented class
attendance/activities according to the instructor’s records.
If funds are returned, it may result in the student owing outstanding
tuition or fees to the school in addition to owing funds back to the
U.S. Department of Education. Any grant amount the student must
return is a federal grant overpayment and arrangements must be
made with the school or the U.S. Department of Education to
return the funds.
How the Percent Earned is determined:
Percent earned = number of calendar days completed up to the
withdrawal date* (less scheduled breaks of 5 days or more) divided
by the total days in the semester (less scheduled breaks of 5 days
or more).

32
| Page
● Percent unearned = 100% minus percent earned.
When a student receives federal financial aid in excess of aid
earned the school returns the lesser of institutional charges
multiplied by the unearned percentage, or federal financial aid
disbursed multiplied by the unearned percentage.
The student is responsible for returning any remaining unearned
federal financial aid the school is not required to return. Loan funds
are repaid in accordance with the terms of the Promissory Note.
Pell Grant funds are due after applying the 50% grant protection.
Federal regulations limit the amount a student must repay to the
amount by which the original overpayment amount exceeds
50% of the total grant funds disbursed to or that could have been
disbursed to the student for the payment period.
Any grant amount the student must return is a federal grant
overpayment and arrangements must be made with the school or
the U. S. Department of Education to return the funds.
After Return of Title IV Funds calculation is complete, federal
funds will be returned in the following order:
1) Unsubsidized Federal Direct Stafford Loan
2) Subsidized Federal Direct Stafford Loan
3) Federal Direct Plus Loan
4) Pell Grant
5) FSEOG
Students will be billed, and payment is due immediately for any
tuition balance created when the School is required to return funds
to the U. S. Department of Education. Students have 45 days from
their withdrawal date to repay to the School any federal grant
overpayment. After the 45 days, the student must work directly
with the U. S. Department of Education to resolve their federal
grant overpayment and may not receive additional Federal
Financial Aid until the overpayment is resolved.
The school must report to the U. S. Department of Education any
student who is in federal grant overpayment status.
Treatment of Title IV Credit Balances When
Student Withdraws:
A Title IV credit balance occurs when the amount of federal
financial aid disbursed exceeds the amount of institutional charges.
When a student withdraws with an outstanding Title IV credit
balance, a school will first perform an R2T4 calculation to
determine whether adjustments to the credit balance will occur.
Any existing Title IV credit balance funds for the payment period
will be included in R2T4. The published institutional refund policy
needs to be performed to determine if doing so creates a new or
larger Title IV credit balance. Any Title IV credit balance applied
as follows:
1. Any Title IV credit balance will be allocated first to repay
any grant overpayment owed by the student because of the
current withdrawal. The institution will return such funds to
the Title IV grant account within 14 days of the date that the
institution performs the R2T4 calculation. Although not
included in an R2T4 calculation, any Title IV credit balance
from a prior period that remains on a student’s account when
the student withdraws is included as Title IV funds when
school determine the final amount of any Title IV credit
balance when a student withdraws.
2. Within 14 days of the date that the institution performs the
R2T4 calculation, an institution will pay any remaining Title
IV credit balance to pay authorized charges at the institution
(including previously paid charges that now are unpaid due
to a return of Title IV funds by the institution) or to the
student (or parent for a Direct PLUS Loan). If the institution
cannot locate the student (or parent) to whom a Title IV
credit balance must be paid, it will return the credit balance
to the Title IV programs.
Post-withdrawal disbursement (PWD)
When federal financial aid that a student has earned as of the
withdrawal date has not yet been disbursed to the student, the funds
can be offered to student through a PWD. A PWD, whether
credited to the student’s account or disbursed to the student or
parent directly, must be made from available grant funds before
available loan funds.
● The college will offer any PWD of loan funds within 30
days of the date of the college’s determination that the
student withdrew.
● The college will return any unearned funds and make a
post-withdrawal disbursement of grant funds within 45
days of that date.
● The college will obtain confirmation from a student, or
parent for a Direct Parent PLUS Loan, before making
any disbursement of loan funds from a PWD, whether
those loan funds are to be credited to the student’s
account or disbursed directly to the student (or parent).
● The student or parent must respond to the notice within
14 days. After that period, the college may decide not to
accept the PWD request.
The information provided in this notification will include the
information necessary for the student, or parent for a Direct Parent
PLUS Loan, to make an informed decision as to whether the
student or parent would like to accept any disbursement of loan
funds and will be provided within 30 days of the date of a college’s
determination that a student has withdrawn.
The student can accept or decline federal financial aid as part of
PWD. A PWD of federal grant funds to satisfy outstanding
allowable charges does not require the student’s acceptance. The
college is required, however, to obtain your permission to credit
your account with federal grant funds in excess of allowable
charges.
You can choose to accept only an amount for the open charges or,
if eligible, to accept a larger amount that will result in excess funds
being returned to you. It is important to understand that accepting
a PWD of student loan funds will increase your overall student
loan debt that must be repaid under the terms of your Master
Promissory Note. Additionally, accepting a PWD of grant funds
will reduce the remaining amount of grant funds available to you
should you continue your education later.

33
| Page
Outstanding charges on a student’s account are charges for which
you will be liable after the application of applicable refund policy.
These are the institutional charges, after any adjustment that
reflects what you will owe for the current term after the
withdrawal. You may also provide permission to credit account for
prior award year charges. Separate student/parent authorization is
not required to use current federal financial aid to cover prior year
charges up to $200 for tuition and fees.
Any credit balance remaining is disbursed as soon as possible but
no later than 14 days from the date of the disbursement of the
PWD.

34
| Page
Practical Nursing Program
Philosophy
The philosophy of the Practical Nursing program reflects the
mission of the school, which is to create and provide a high-quality
educational experience to each individual student seeking to
establish a successful career.
The basic philosophical concepts of the Practical Nursing program
are person, health, nursing, caring, environment/society, and
nursing education.
The person is viewed as a holistic being comprised of biophysical,
psychosocial, emotional, spiritual, intellectual, and cultural needs
or components.
The person is also an individual, a family member, and a member
of the local, regional, and world community.
Health is a dynamic process of adaptation to biophysical,
psychological, social, spiritual, and environmental influences,
whereby the person is able to function in an optimal state.
Nursing is both an art and a science, the goal of which is to care
for individuals so that they may achieve optimal health.
Caring is the very heart of nursing. Consistent with the philosophy
of Jean Watson (1985), caring involves an interpersonal
relationship between the person and the nurse. Through holistic
health care, the nurse assists in promoting and maintaining the
health of the person and family.
Environment/Society directly and indirectly affects a person’s
ability to cope with the student's own needs, as well as those of
others.
Organizing Theme of the Nursing Program
The nursing faculty of the School believes in a nursing curriculum
that focuses on caring as the underlying theme. According to
Watson (1985/88), caring is the most valuable attribute nursing has
to offer. Watson (1985) has identified the following seven
assumptions about the science of caring:
1) Caring can be effectively demonstrated and practiced only
interpersonally.
2) Caring can be effectively demonstrated and practiced only
interpersonally.
3) Caring consists of “carative” factors that result in the
satisfaction of certain human needs.
4) Effective caring promotes health and individual or family
growth.
5) Caring responses accept a person not only as he or she is now
but as what he or she may become.
6) A caring environment is one that offers the development of
potential while allowing the person to choose the best action
for him or herself at a given point in time.
7) Caring is more “healthogenic” than is curing. The practice
of caring integrates biophysical knowledge with knowledge
of human behavior to generate or promote health and to
provide administrations to those who are ill. A science of
caring is therefore complementary to the science of curing.
8) The practice of caring is central to nursing (Watson, 1985,
pg.8-9).
In addition, Watson lists the following ten caritive factors upon
which the science of caring is built.
1) The formation of a humanistic-altruistic system of values.
2) The installation of faith-hope.
3) The cultivation of sensitivity to one’s self and to others.
4) The development of a helping-trust relationship.
5) The promotion and acceptance of the expression of positive
and negative feelings.
6) The systematic use of the scientific problem-solving method
for decision making.
7) The promotion of interpersonal teaching-learning.
8) The provision for a supportive, protective, and (or) corrective
mental, physical, sociocultural, and spiritual environment.
9) Assistance with the gratification of human needs.
10) The allowance for existential-phenomenological forces
(Watson, 1985, pg. 9-10).
The role of the nurse is to provide effective care in a variety of
settings to diverse individuals and families across the lifespan.
This caring role includes being a communicator, a collaborator, an
educator, and a manager.
References
● George, J. B., Editor (1995). Nursing Theories. The Base
for Professional
● Nursing Practice. Norwalk: Appleton and Lange.
● Watson, J. (1985). Nursing’s Scientific Quest. Nursing
Outlook, 29, 413-416.
● Watson, J. (1985). Nursing: The Philosophy and Science of
Caring. Boston: Little, Brown.
● Watson, J. (1988). Nursing: Human Science and Human
Care, A Theory of Nursing. New York: National League for
Nursing.
Practical Nursing Program Information
Program Delivery: Residential, Blended
Diploma Awarded: Practical Nursing Diploma
Length of Program: 3 semesters
Semesters One (1) and Two (2) – 15 weeks
Semester Three (3) – 19* weeks
Semester Credit Hours: 52
Inside Clock Hours: 1179
Recognized Outside Clock Hours: 362.25
Program Delivered in English only
Program Description
The Practical Nursing Program is designed to prepare the student
for the role of a Licensed Practical Nurse who is able to function
interdependently with colleagues in a variety of health care
settings, including acute care hospitals, long-term care facilities,
and community-based agencies. The program is based on nursing
concepts and skills, which enable the nurse to contribute to health
promotion, maintenance, and restoration of clients across the
lifespan.
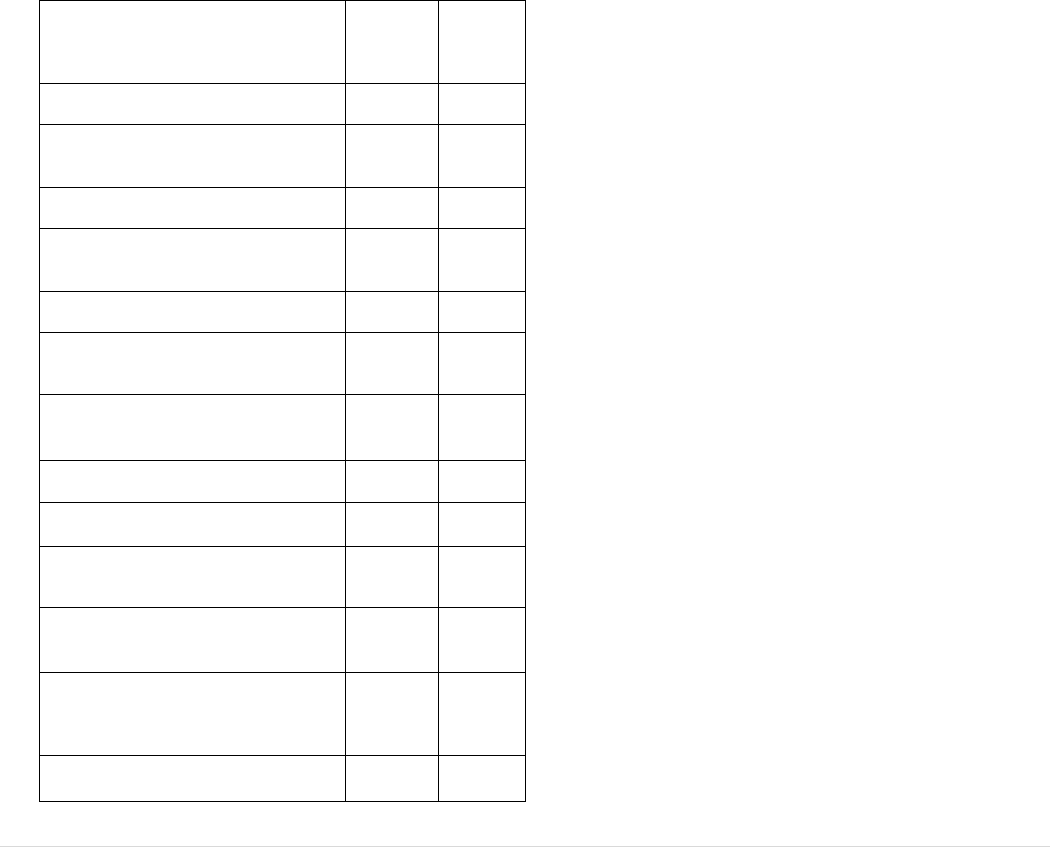
35
| Page
Program Outcomes
Upon completion of the Practical Nursing Program, graduates will
be prepared to:
1) Assume entry-level positions in practical nursing to assist
clients with health needs through use of basic nursing skills.
2) Deliver competent holistic nursing care safely to persons of
all ages in a variety of structured healthcare settings by
demonstrating professional ethical characteristics, use a
caring approach, and establishing effective interpersonal
relationships with clients and families.
3) Demonstrate a commitment to a lifelong process of education
and personal and professional development through
continuing education and participation in professional
organizations.
4) Apply knowledge from the physical, biological,
psychosocial, and nursing sciences, while contributing to
promoting, maintaining, and restoring health to culturally
diverse clients.
5) Engage in professional communication and collaboration as
delegated with all members of the healthcare team.
Program of Study
Academic
Credits
Financial
Aid
Credits
First Semester (15 weeks)
BIO1090 Anatomy & Physiology with
Medical Terminology
6.0
3.5
NUR1090 Art of Nursing
1.5
1.5
NUR1095 Nursing Fundamentals with
Intro to Pharmacology
11.5
9.0
Second Semester (15 weeks)
NUR1109 Nursing Care of the Adult 1
9.5
7.5
NUR1105 Nursing for the Family and
Nursing for Children
4.0
2.8
NUR1100 Critical Thinking Lab
3.0
2.0
Third Semester (19 weeks)
NUR1121 Nursing Care of the Adult 2
9.5
7.5
NUR1128 Nursing Care of the Older
Adult and Nursing for Mental Health
5.5
4.0
NUR1114 Nursing Seminar -
Transition to Practice
1.5
1.5
REV1003 NCLEX-PN Review Course
0.0
0.0
Career Information
After completion of the Practical Nursing Program of Study, the
student is eligible to apply for licensure as a Practical Nurse by
taking the NCLEX-PN. Licensed Practical Nurses (L.P.N.) are
employed in acute care, long-term care, and community-based
health care agencies under the direction of a Registered Nurse.
Practical Nurses function within their legal scope of practice and
use professional standards of care in illness care and health
promotion activities for clients and families across the lifespan.
Course Descriptions for Practical Nursing
Curriculum
Definitions:
Prerequisite courses are a requirement that the student must fulfill
prior to beginning the course for which it is a prerequisite.
Co-requisite courses are courses that must be taken prior to or at
the same time to the course for which it is a co-requisite.
Equivalent courses: failure of an equivalent course is considered
failing a repeated course.
BIO1090 Human Anatomy with Medical Terminology
6 credits
Course Description:
This course studies the structure and function of the human body
using the integrating principle of homeostasis and utilization of
medical terminology for nursing students. Organization of the
human body, organs, and systems are discussed. Emphasis is
placed on the following organ systems/topics: integumentary,
skeletal, muscular, nervous, senses, cardiovascular, lymphatic,
immune, respiratory, endocrine, digestive, urinary, and
reproductive as well as fluid/electrolyte balance, acid/base
balance, pregnancy and growth & development and nutrition.
This course includes additional clock hours outside of theory,
theory application lab hours, and medical terminology activities.
Prerequisites: Placement into the nursing program by achieving
required benchmark on TEAS exam.
Co-requisites: None
NUR1090 Art of Nursing
1.50 credit
Course Description:
This course helps the student adjust to the role as a student nurse,
understand the nursing profession and prepare for successful
practice through demonstration of essential nursing concepts such
as caring, spirituality, presence, compassion, self-care and
advocacy. This course will help the student with communicating
effectively and preparing for the NCLEX-PN through good study
and test taking skills. This course includes additional clock hours
outside of class time.
Prerequisites: None
Co-requisites: None
NUR1095 Nursing Fundamentals with Pharmacology
11.5 credits
Course Description:
This course utilizes research from the National Council of State

36
| Page
Boards of Nursing (NCSBN) activities of safe nursing practice
for the Licensed Practical Nurse (LPN) and the NCLEX PN test
plan to provide a framework for this course. The course focuses
on safe clinical decision making based on evidence-based
practice for all body systems including basic skills,
pharmacology, laboratory, simulation and clinical experiences for
learning. Variations across the lifespan are considered. This
course requires successful completion of concurrent lab and
clinical hours.
Prerequisites: Placement by achieving required benchmark on
TEAS exam
Co-requisites: BIO1090 Human Anatomy with Medical
Terminology
Equivalent: Any combination of previous courses titled “Nursing
Fundamentals” and “Pharmacology”
NUR1105 Nursing for the Family and Nursing for Children
4 Credits
Course Description:
This course focuses on maternity nursing care of the woman during
her maternity cycle and her family including pediatric nursing care
of the child across the lifespan through adolescence. The nurse’s
teaching, caring, communication, and critical thinking roles are
discussed and used with application to the nursing process as
appropriate to the Licensed Practical Nurse scope of practice. The
care of families experiencing issues of psychological, cultural, and
spiritual needs is explored.
This course requires successful completion of concurrent lab
hours.
Prerequisites: BIO1090 Human Anatomy with Medical
Terminology, NUR1090 Art of Nursing, NUR1095 Nursing
Fundamentals
Co-requisites: None
NUR1100 Critical Thinking
3 credits
Course Description:
This course provides students with knowledge to implement the
theoretical perspectives on, and practical reality of, making
judgment and decisions in the best interest of patients and clients.
Theoretical input will be supported by case study exploration and
reflection and allow students to explore the complexity of clinical
decision making and judgment within the healthcare industry. This
course will enhance the student cognitive processes which
underpins safe and effective care delivery in the healthcare setting
that uses formal and informal thinking strategies to gather and
analyze patient information, evaluate the significance of this
information and weigh alternative actions. This course requires
successful completion of concurrent lab hours
Prerequisites: BIO1090 Human Anatomy with Medical
Terminology, NUR1090 Art of Nursing, NUR1095 Nursing
Fundamentals w/intro to Pharmacology
Co-requisites: NUR1109 Nursing Care of the Adult 1
Equivalent: Any course titled “Critical Thinking”
NUR 1109 Nursing Care of the Adult 1
9.5 credits
Course Description:
This course builds on concepts and skills learned in Fundamentals
of Nursing. Students will apply the nursing process when learning
how to care for adult medical-surgical patients and their families
experiencing complicated chronic or an acute alteration in health.
Research from the National Council of State Boards of Nursing
(NCBSN), activities of safe nursing practice for the LPN, the
NCLEX Test Plan and reinforcement of clinical reasoning and
clinical judgment skills are incorporated in this course. This course
requires successful completion of concurrent lab and clinical
hours.
Prerequisites: BIO1090 Human Anatomy with Medical
Terminology, NUR1090 Art of Nursing and NUR1095 Nursing
Fundamentals with Pharmacology
Co-requisites: NUR1100 Critical Thinking
Equivalent: Any courses titled “Nursing Care of the Adult”,
“Nursing Care of the Adult 1”, “Nursing Care of the Adult I”
NUR 1121 Nursing Care of the Adult 2
9.5 credits
Course Description:
This course is a continuation of concepts and skills learned in
Nursing Care of Adult 2. Students will apply the nursing process
when learning how to care for adult medical-surgical patients and
their families experiencing complicated chronic or an acute
alteration in health. Research from the National Council of State
Boards of Nursing (NCBSN), activities of safe nursing practice for
the LPN, the NCLEX Test Plan and reinforcement of clinical
reasoning and clinical judgment skills are incorporated in this
course. This course requires successful completion of concurrent
lab and clinical hours.
Prerequisites: NUR1109 Nursing Care of the Adult 1, NUR1105
Nursing for the Family and Nursing for Children, NUR1100
Critical Thinking
Co-requisites: None
Equivalent: NUR1120 Nursing Care of the Adult II
NUR 1128 Nursing Care of the Older Adult and Nursing for
Mental Health
5.5 credits
Course Description:
This course focuses on nursing care of the older adult and clients
with mental health issues. Emphasis is placed on the role of the
Licensed Practical Nurse and his/her contribution to the nursing
process in meeting the physiological, psychosocial, cultural, and
spiritual needs of older adult clients, mental health clients, and their
families. Critical thinking skills and a caring manner are used in
nursing care delivery, coordination, collaboration, and
documentation. Clinical experience is a component of this course
that allows the student to demonstrate effective communication
skills with the client and clinical staff and the appropriate use of
the nursing process in the delivery of nursing care to the older adult
client and the mental health client. This course requires successful
completion of concurrent lab and clinical hours.
Prerequisites: BIO1090 Human Anatomy with Medical
Terminology, NUR1090 Art of Nursing, NUR1095 Nursing
Fundamentals with Pharmacology
Co-requisites: None

37
| Page
Equivalent: Any course title that includes, “Nursing Care of the
older Adult and Nursing for Mental Health”, “Geriatric/Mental
health Nursing”, “Nursing for Mental Health”, “Geriatric Nursing”
NUR1114 Nursing Seminar - Transition to Practice
1.5 credits
Course Description:
This course builds upon previous nursing courses for the
acquisition and application of nursing theory necessary for safe,
patient-centered nursing care of diverse patients across the lifespan
while integrating legal and ethical responsibilities of the Practical
Nurse. This is a milestone course that prepares students for
practice.
Prerequisites: NUR1090 Art of Nursing, NUR1095 Nursing
Fundamentals with Pharmacology, NUR1100 Critical Thinking,
NUR1109 Nursing Care of the Adult 1, NUR1105 Nursing for the
Family and Nursing for Children
Co-requisites: None
Equivalent: Any course titled “Nursing Seminar”, “Seminar”
REV1003 NCLEX Review Course
0 credits
Course Description:
This learning experience prepares students to pass the
Comprehensive Exit Examination and the NCLEX-PN licensure
examination. Various teaching-learning strategies are used to
assist students in answering questions based on cognitive levels of
application and higher.
Prerequisites: NUR1090 Art of Nursing, NUR1095 Nursing
Fundamentals with Pharmacology, NUR1100 Critical Thinking,
NUR1109 Nursing Care of the Adult 1, NUR1105 Nursing for the
Family and Nursing for Children, NUR1114 Nursing Seminar
Co-requisites: NUR1121 Nursing Care of the Adult 2, NUR1128
Nursing Care of the Older Adult and Nursing for Mental Health
Developmental Courses
(Developmental Courses are not considered for credit)
ENG0930 Reading and Mastering Study Skills
0 credits
Course Description:
This course prepares students for college-level courses and exams
that require the ability to read comprehensively and think
critically. Students will learn in-depth methods of applying reading
concepts, study strategies and critical thinking skills to college-
level content texts. Group discussions and other in-class activities
will allow students to: develop their study and comprehension
skills, analyze critically what they have read or seen, acquire new
vocabulary in context, articulate their inferences, and refine their
ideas for individual writing assignments. Students will learn how
to apply these strategies across the ATS curriculum. Students will
use computers to document their in-class and home assignments
Prerequisites: None
Co-requisites: None
ENG0935 Writing Strategies
0 credits
Course Description:
This course enhances and refines students’ writing skills and
develops their ability to use formal English. Students will learn to
express their ideas clearly and precisely in complete sentences that
comply with the standards of English grammar. Students will
compose intelligible sentences free of serious errors in grammar,
organization, and style. Students will use computers to document
their assignments and practice skills. Students will learn how to
edit their own writing for grammatical correctness and revise
paragraphs and essays for unity, logic, coherence, and
completeness.
Prerequisites: None
Co-requisites: None
MAT0930 Basic College Math
0 credits
Course Description:
This course provides students with basic math skills required for
success in School education. This course covers basic
computational math and high school algebra including, but not
limited to, ratios and proportions, and metric. Students are shown
many methods to sharpen their math skills and are provided
multiple opportunities to practice those skills. Refreshing their
knowledge of learned math will be an important part of the course.
Prerequisites: None
Co-requisites: None
Support Courses
(Support courses are not considered for credit)
SUC1001 Success Strategies
0 credits
Course Description:
This course is designed to introduce the newly enrolled ATS
student to the student role, resources, and strategies to enhance
success in School. The student will learn professionalism required
for the academic and professional roles, resources necessary for
optimal performance as a nursing student, and personal skills such
as time management and studying based on individual learning
style.
Prerequisites: None
FLS1001 Focused Learning Seminar
0 credits
Course Description: This course is designed to support current
nursing students through a remediation/tutoring for course
content. The student will revisit predetermined content topics
based on the didactic instruction for that week.
Prerequisites: None
NUR040 Nursing Exit Seminar
0 credits
Course Description:
This is a required course for any student who fails the
Comprehensive Exit Examination the first time. An individual
focused plan of remediation will be developed by the student and
faculty coach. Class will incorporate various strategies and test
taking techniques to maximize opportunities for success.

38
| Page
Completion of the seminar will occur when the student reaches the
course examination’s established benchmark.
Prerequisites: None
NUR0950
0 credits
Course Description:
This is a required course for any student who failed the
Comprehensive Exit Examination and has been assigned by the
Director of Nursing. An individual focused plan of remediation will
be developed by the nursing coach Class will incorporate support
programs and will incur an additional fee per vendor used. Completion
of the seminar will occur when the student reaches the established
benchmark.
Prerequisites: None
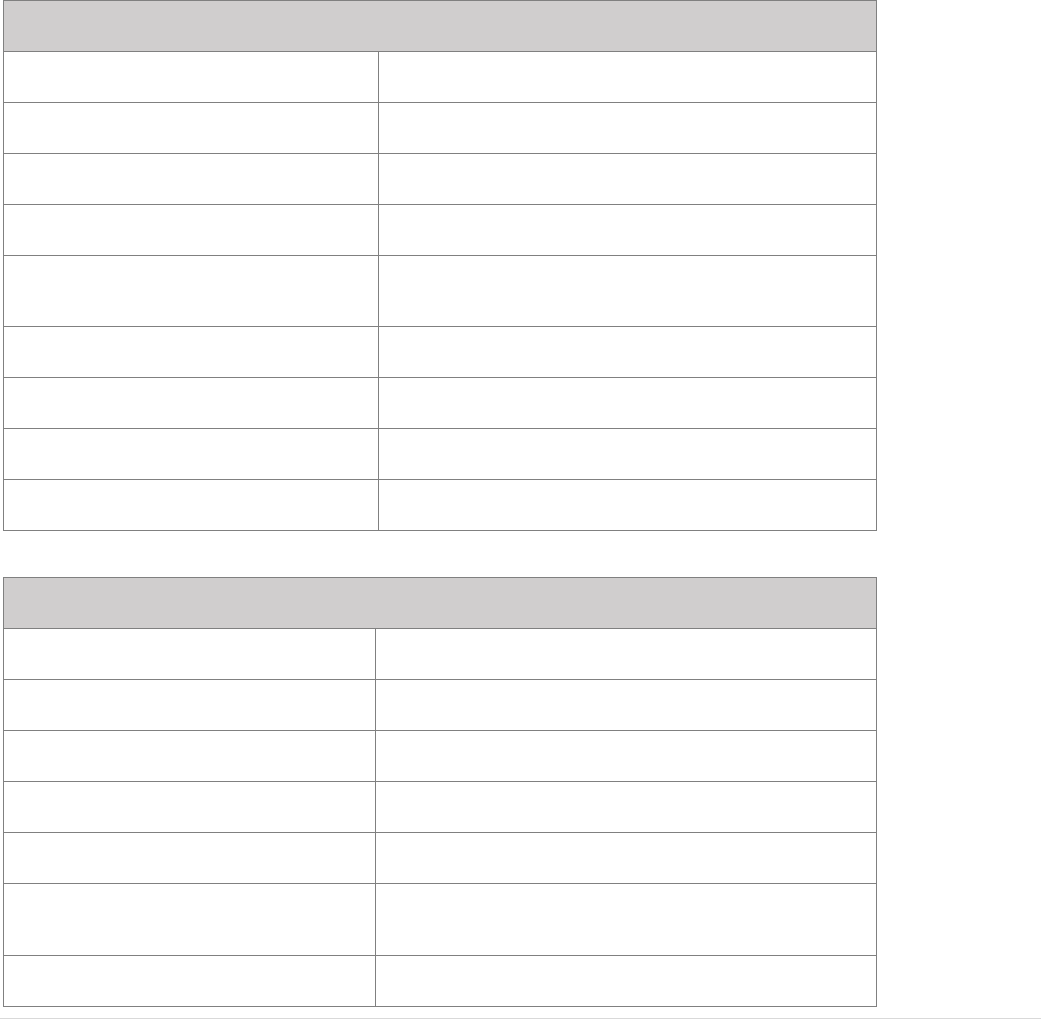
39 | Page
Appendices
Appendix A: Academic Calendar Spring 2024 – Spring 2025
Practical Nursing program offered on a trimester basis. Each semester (fall, spring, and summer) consists of fifteen (15) weeks of academic work
with scheduled breaks between semesters. Students are scheduled for two 15-week sessions and one 19-week session at the end of the program.
Students can add or drop classes without penalty during the first two weeks of the semester. (See Add/Drop Period policy) Students who are
withdrawing from the semester are required to follow the Withdrawal policy outlined in the handbook and review the Refund policy to understand
financial obligations to the school.
SPRING 2024 SEMESTER
January 8, 2024
Spring Semester 2024 Classes begin
January 15, 2024
Martin Luther King Day (CAMPUS CLOSED)
January 19, 2024
Last day to add/drop classes without penalty
February 19, 2024
Presidents’ Day (CAMPUS CLOSED)
March 15, 2024
Last day to submit an official withdraw from classes
with a "W"
April 8, 2024– April 19, 2024
Final Exams, Standardized testing and Remediation
April 20, 2024
Last day of Semester
April 22, 2024 – May 3, 2024
Student Break (NO SCHOOL)
May 17, 2024
Last day for Spring Semester Graduates
SUMMER 2024 SEMESTER
May 6, 2024
Summer Semester 2024 Classes begin
May 17, 2024
Last day to add/drop classes without penalty
May 27, 2024
Memorial Day (CAMPUS CLOSED)
June 19, 2024
Juneteenth (CAMPUS CLOSED)
July 4, 2024
July 4
th
Holiday (CAMPUS CLOSED)
July 12, 2024
Last day to submit an official withdraw from classes
with a "W"
August 5 - August 16, 2024
Final Exams, Standardized testing and Remediation
40 | Page
August 17, 2024
Last day of Semester
August 19- September 2, 2024
Student Break (NO SCHOOL)
August 19- Sep. 14, 2024
Summer Graduates NCLEX review class
September 13, 2024
Last day for Summer Semester Graduates
FALL 2024 SEMESTER
September 2, 2024
Fall Semester 2024 Classes begin
September 2, 2024
Labor Day (CAMPUS CLOSED)
September 13, 2024
Last day to add/drop classes without penalty
November 8, 2024
Last day to submit an official withdraw from classes
with a "W"
November 11, 2024
Veterans Day (CAMPUS CLOSED)
November 21-23, 2024
Thanksgiving Break (CAMPUS CLOSED)
December 2 - December 13, 2024
Final Exams, Standardized testing and Remediation
December 14, 2024
Last day of Semester
December 16, 2024 - January 3, 2024
Student Break (NO SCHOOL)
December 24, 2024
Campus Closed at 1pm
December 25, 2024
Christmas Day (CAMPUS CLOSED)
December 31, 2024
Campus Closed at 1pm
January 1, 2024
New Year’s Day (CAMPUS CLOSED)
January 14, 2025
Last day for Fall Semester Graduates
SPRING 2025 SEMESTER
January 6, 2025
Spring Semester 2025 begins
January 17, 2025
Last day to add/drop classes without penalty
January 20, 2025
Martin Luther King Day (CAMPUS CLOSED)
February 17, 2025
President’s Day (CAMPUS CLOSED)
41 | Page
March 14, 2025
Last day to submit an official withdraw from classes
with a "W"
April 7, 2025 – April 18, 2025
Final Exams, Standardized testing, and Remediation
April 19, 2025
Last day of the Semester
April 21, 2025 – May 2, 2025
Student Break (NO SCHOOL)
May 19, 2025
Last day for Spring Semester Graduates
*ATS reserves the right to change this Academic Calendar without notice.
CAMPUS CLOSED = Students and Staff off
NO SCHOOL - Students off
42 | Page
Appendix B: Faculty and Administration
Administration
Leonard Bykov
President
Yelena Bykov
Chief Executive Officer
Lydia Falbo DNP, MSN, RN
Director of Nursing
DNP, BSN, RN, Rush University
Susan Elliot
Director of General Education
Full-time instructor
MA, BA, St. Xavier University
Rumy Kabir
Director of Instructional
Technology and Online Learning
MA Iowa State University; BS,
Northwestern Oklahoma State
University
Irina Bondar
Financial Aid Director
Gina Anadilla
Operations Manager
BA, California State University
Northridge
Amy Bieganski
Manager of Admissions &
Recruitment
BS, Robert Morris Experiential
College
Elvis Falbo, MSN, BSN
MSN & BSN, Olivet Nazarene
University
SIM Coordinator
Nursing Faculty
Vivian Aguinaldo, BSN, RN
BSN, Arellano University,
Philippines
(Part-time instructor)
Nikki Campobasso, BSN, RN
BSN, Olivet Nazarene University
(Part-time instructor)
Karla Cifuentes, MSN, RN
MSN, Western Governors
University
(Full-time instructor)
Joan Gramata, NP, MSN, RN
MSN, Rush University
BSN, University of Illinois Chicago
(Part-time instructor)
Robin Isabell, BSN, RN
BSN, Indiana University
(Nursing Success Coach)
D’Andrea Lenore, MSN, BSN
MSN,University of Phoenix
BSN, Chicago State University
(Full-time instructor)
Salitha Marsh, BSN, RN
BSN, Benedictine University
RN, City Colleges of Chicago
(Part-time instructor)
Ceaira Moore, BSN, RN
BSN, Governors State University
RN, Prairie State University
(Full-time instructor)
Maria Medina, MSN, BSN, RN
MSN- North Park University
BSN – Far Eastern University
(Part-time instructor)
Elizabeth Nikolic, BSN, RN
BSN, Saint Xavier University
(Full-time instructor)
Wanda Robertson, MSN, RN
MSN, American Sentinel
University
(Full-time instructor)
Deborah Staggers, BSN, RN
BSN, Howard University
(Part-time instructor)
Cheryl Terry, MSN, RN
MSN, Saint Xavier School
BSN, Southern Illinois University
(Full-time instructor)
Van Fabie Tunguia BSN, RN
BSN, RN Herzing University
(Full-time instructor)
Renee Vanorsby, MSN, RN
MSN, Chamberlain University
(Part-time instructor)
43 | Page
General Education Faculty
Alex Klitz
M.F.A, Full Sail University
BA, Roosevelt University
(Part-Time Instructor)
Retention Specialist
Nathan Linscheid
MS, Northwestern University
BS, University of Oregon
(Full-time instructor)
Staff
Dalia Kilyan
Bursar
Joel Freecheck
Admissions Advisor
Makeva Glenn
Financial Aid Officer
Brian Hedges
IT Specialist
Teresa McShane
Financial Aid Advisor
(Part-time)
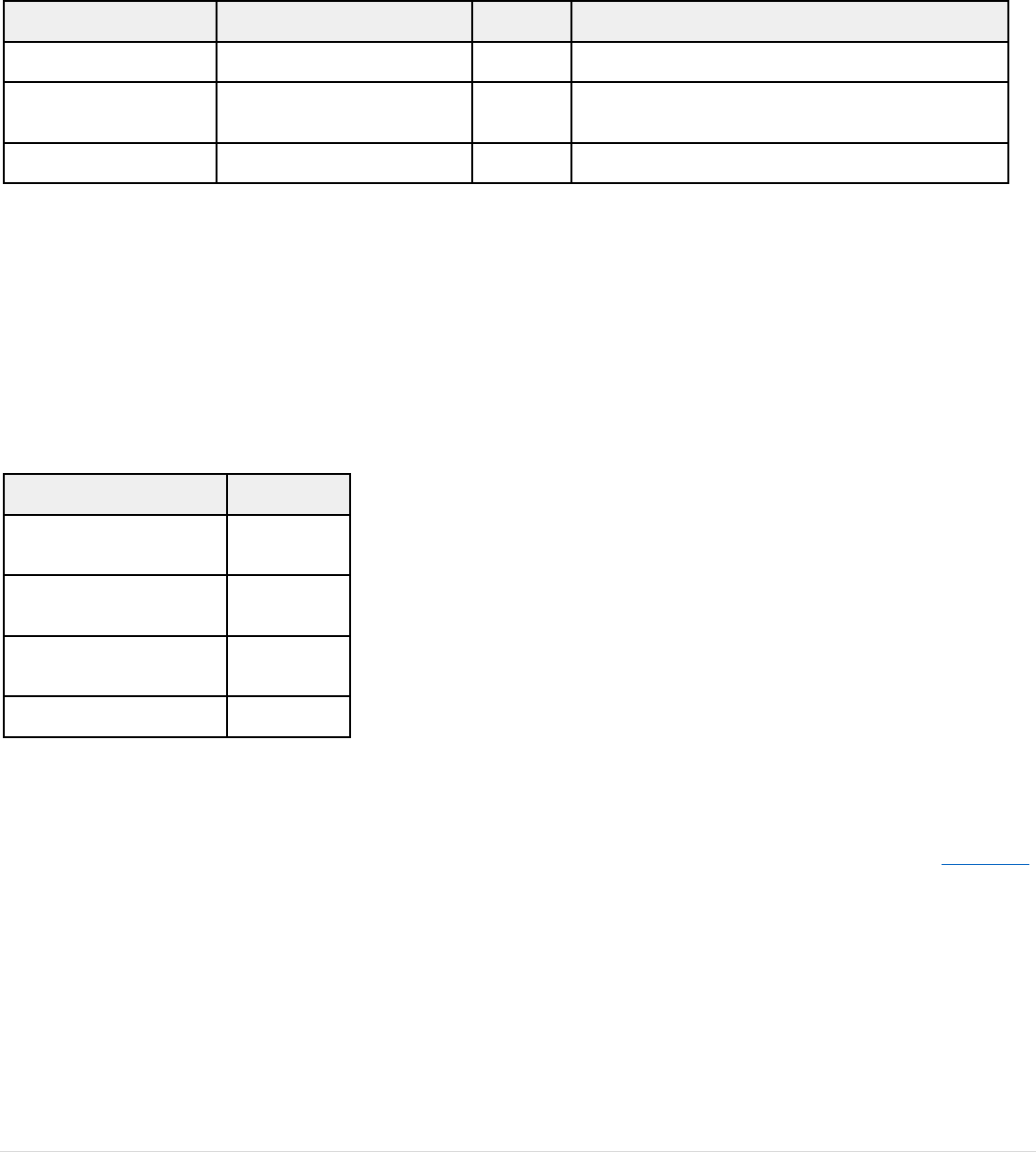
44 | Page
Appendix C: Tuition and Fees
Note: If a student fails a course, they have failed to progress and must now meet the policies and program requirements as outlined in the student
handbook in effect for the cohort they will be placed in, this includes tuition and program fees
Tuition & Fees
Cost Per Semester (3 Semesters)
Total Cost
Description
Program Tuition & Fees
$10,400
$31,200
Tuition & Fees
Course Fee
NA
$800
Course Fee for the REV1003 NCLEX Review course is
charged at the time the student is taking the course.
TOTAL PROGRAM COST
$32,000
Additional cost for Developmental Courses (if required)
If you are required to complete one or more Developmental Courses, your Tuition and fees will be adjusted to reflect scheduled developmental
classes in the following amounts: $2,392 for ENG0930 and MAT0930 courses, $1,316 for the ENG0935 course. If you are scheduled to take each of
the above-listed Developmental Courses, your total program cost will not exceed $38,100 and the breakdown of your Program Tuition & Fees cost
per semester will be $9,325 over 4 semesters. However, see below if you plan to attend or are scheduled on less than a full time basis or if you need
to repeat courses that you did not pass on your first attempt.
The ATS Practical Nursing Program is designed in a sequential order and is offered on a full-time basis. If you plan to attend or are scheduled on a
less than full-time course load or need to repeat courses, you will not be able to stay in your original cohort and you will be billed for the credits you
attempt according to the table below. If you return to full-time status, you will again be charged based on the price per semester.
Financial Aid Credits Tried
Semester Cost
9 - 11.99
$8,400
6 - 8.99
$7,400
3 - 5.99
$2,700
1 - 2.99
$1,700
COST OF ATTENDANCE MAY INCLUDE:
● Estimated Book Fees is $530. Students are responsible for purchasing books from a 3rd party vendor when not included in the inclusive
access materials.
● Inclusive access materials that are available for individual purchase may be purchased by the student when they complete the opt-out form,
which includes the opt-out process.
● The estimated uniform cost is $32. Students are responsible to purchase uniforms and ATS patches in accordance with the Professional
Dress Code Policy. The cost of uniforms and additional supplies may vary depending on purchase location. Additional supplies may include
a stethoscope, watch with a second hand and any other supplies requested by the faculty
● Estimated Clinical Site Parking is $160 per semester: Students are responsible for payment of parking at clinical sites. The school is not
responsible for reimbursement for parking fees. Clinical site parking cost may vary per facility. Some sites may require parking fees or the
use of parking meters.
● Estimated immunization fees are $500, if required based on results of lab testing. Students are responsible for all fees related to
immunizations. If your immunization record is up to date, you may avoid this fee.
MISCELLANEOUS FEES:
● Financial charges may apply for late payments, bounced checks/declined credit cards or double deposited checks
● ID Badge Replacement: $25

45 | Page
● Supplemental ATI exams: $75
● VATI Extension: $100
● Stand Alone Clinical Fees: $345
POST-GRADUATION ESTIMATED COST: Student is responsible for all post-graduation fees related to licensure
● Continental Testing Services $107
● Pearson Vue: $200
● Fingerprinting: $65

46 | Page
Appendix D: TEAS Policy
Students must have a passing Lexile score, pass all of their developmental courses and complete the practice assessment with required remediation
to be eligible to sit for the TEAS exam. Any attempt at TEAS without clearance will result in a voided test score and must be taken when approved
by ATS.
Students who successfully pass the TEAS exam and score under 58% in any individual category, must complete a remediation program chosen and
assigned by ATS. The remediation must be completed in the timeline assigned, prior to entering the first Nursing semester.
Students may have a maximum of two attempts to successfully pass the TEAS exam. If a student is unsuccessful after a second attempt, the student
will be dismissed from the Program.
Students that score below the required benchmark will be given three options to choose:
Option 1: Sit out a semester while working on a TEAS preparation program (as assigned by ATS). Once successfully completed with the required
preparation program, they will be eligible to take the final attempt at the TEAS examination. If the student chooses this option, the student may
request to sit out for one semester. The student will be required to meet the deadlines and assigned preparation program approved by the General
Education Director to be eligible for the final TEAS attempt.
Option 2: Retake Developmental courses in the following semester. Take their final TEAS attempt at the end of the semester.
Option 3. Remediate within the prescribed timeline after the initial TEAS attempt as developed by instructors and/or remediation specialist.
a. Students will complete a TEAS remediation program based upon their TEAS score as assigned by the General Education Director and/or
Remediation specialist. This may include self-study, instructor remediation, and TEAS preparation programs.
b. Students will have to successfully complete TEAS remediation by the given deadline in order to sit for the final attempt at the TEAS exam.
A student dismissed from the school due to not passing the TEAS exam will only be eligible to apply for readmission by submitting proof of college
coursework or equivalent within all areas where the student scored below 45%. Coursework submitted will be evaluated by the General Education
Director and/or the Director of Nursing for approval of eligibility to apply for readmission. Eligibility to apply for readmission does not guarantee
readmittance to the program (see Appendix N: Readmission Guidelines).

47 | Page
Appendix E: Readmission - No Exit Appeal Policy
No Exit Appeal Process for students dismissed up to 2 semesters from their last nursing course.
A student requesting to immediately return into the nursing program, following an unsuccessful exit process must complete the following:
1. The student must notify the Registrar’s Office via readmission request form that an appeal is being requested. The notification
must be received within 30 days prior to the semester applying for readmission.
2. The Student will provide the appropriate documentation which will be given in the Registrar’s letter along with the required
submission deadline.
3. The Registrar's office will schedule the student with the Enrollment Appeals Committee (EAC) after the appropriate
documentation is received.
4. The student will be notified of the Enrollment Appeals Committee decision in writing within 3 business days of the committee
meeting. The decision by the Enrollment Appeals Committee is final.
5. If a student appeal is approved, and the student does not return the following semester, the student will be required to follow
the readmission process provided they are not more than 2 semesters from their last nursing course.
6. An appeal granted or denied constitutes the final opportunity for a student to complete the Nursing Program. If a student is
unsuccessful in any requirements, there is no other opportunity to complete the exit process.
7. Students will be required to complete coursework as recommended by the Director of Nursing.
8. In the event a student exceeds 150% of the maximum time frame allowed to complete the program, the student may submit a Maximum Time
Frame appeal. In cases where the appeal is granted, students may continue with readmission.
9. Upon successful completion (passing score and/or C or better) of the required components, the student will proceed with the program exit
examination requirements.
10. Only one attempt of the Exit Exam will be allowed.
Students that are more than 2 semesters from the last date of the last nursing course will not be eligible for readmission.
Readmission into ATS Institute of Technology will be dependent on space available to accommodate additional students. If the number of accepted
applicants exceeds available space, the decision will be based on the student’s GPA and academic history of coursework previously taken at ATS
Institute of Technology and applicants may be deferred to a subsequent semester.
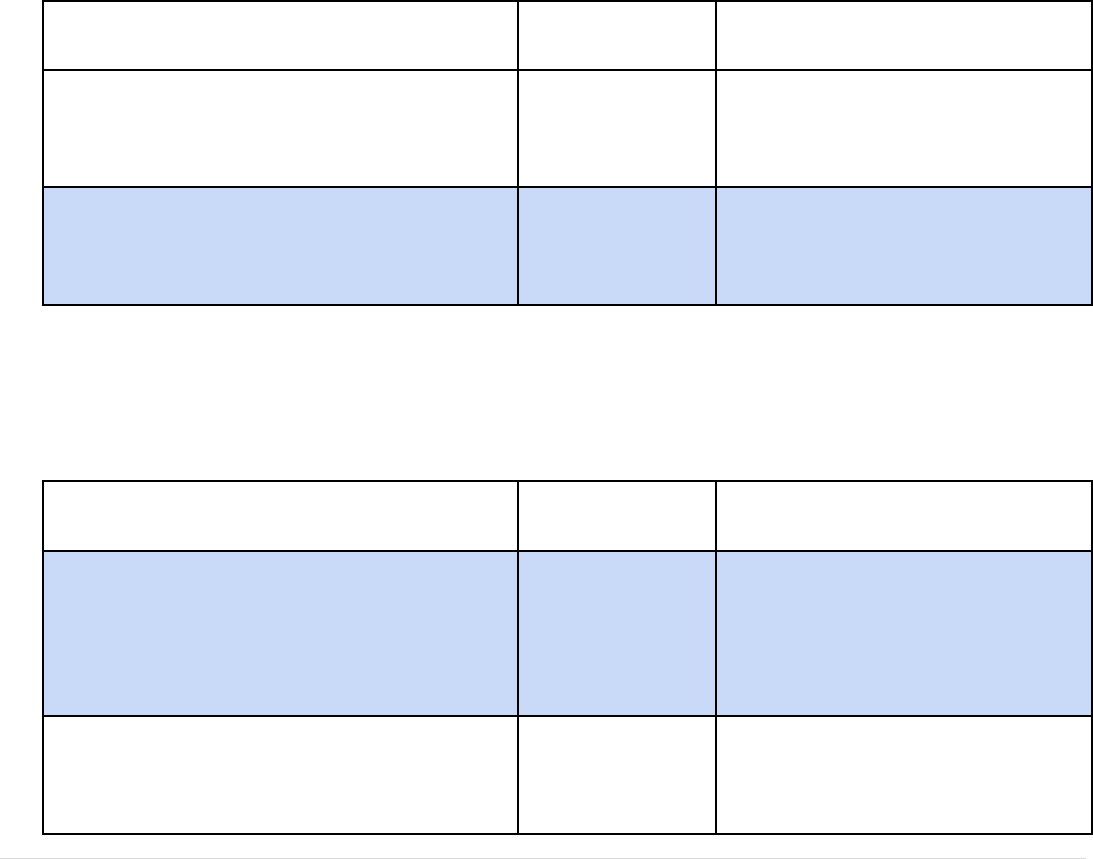
48 | Page
Appendix F: Documentation for Clinical
Medical Compliance Requirements: Students are required to have up to date medical records and CPR in accordance with the requirements
below. Students are responsible for keeping all immunizations, PPD testing, physical exam, medical insurance, and CPR current. Students must
update any medical document with an expiration date to ensure that they are current and on file in the Nursing Department Office for students to
be placed in the clinical setting.
Students beginning in the developmental semester must have all medical documentation completed and accepted by week 10 of the developmental
semester. Students who do not meet the medical compliance requirements by the stated deadlines, will not be automatically enrolled in the Nursing
Fundamentals course in the following semester. Students who complete after the week 10 deadline will be placed on a waiting list and enrolled if
space allows.
Students beginning in the nursing semester must have all medical documentation completed and accepted by the end of the second week of the
semester of acceptance. Students who do not meet the medical compliance requirements by the stated deadline will be removed from the Nursing
Fundamentals course.
All documents with the expiration dates within the next semester must be updated before the start of the semester.
Medical Record Requirements are subject to change in accordance with clinical site requirements and will be required. Failure to complete Medical
Record Requirements will bar a student from registering for courses with a clinical component.
All students required at admission/readmission to complete the following within a required deadline
Medical Compliance Item
Where Can I Get It
Done?
How Long Does It Take?
Criminal Background Check Report through Castlebranch
● Add package code: AW85
● Must sign and return release form for the
background to be completed
Castlebranch
1-3 business days
Drug Testing Report through Castlebranch
● Add package code to Castlebranch: AQ92dt
Order through Castlebranch and will go to Quest to get the
test completed
Quest & Castlebranch
1-2 business days from the time the urine is
submitted
See also policy on Drug Testing in this catalog
To be registered for all mandatory clinical experience, the following is needed for all students:
1. Register at Castlebranch Medical Manager. All documents take at least 48 business hours to approve
a. Add the package code AW85im
2. Complete and upload the documentation required. Review below table to understand steps needed.
Medical Compliance Item
Where Can I Get It
Done?
How Long Does It Take?
CPR Card
American Heart Association for Healthcare Provider BLS -
must have hands on skills testing as no electronic re-
certifications are accepted.
American Heart
Association
AHA can take several weeks to get scheduled for
the face to face skills
Physical Attestation Form (required)
and/or
Form in Medical Packet
2-3 days once submitted for approval
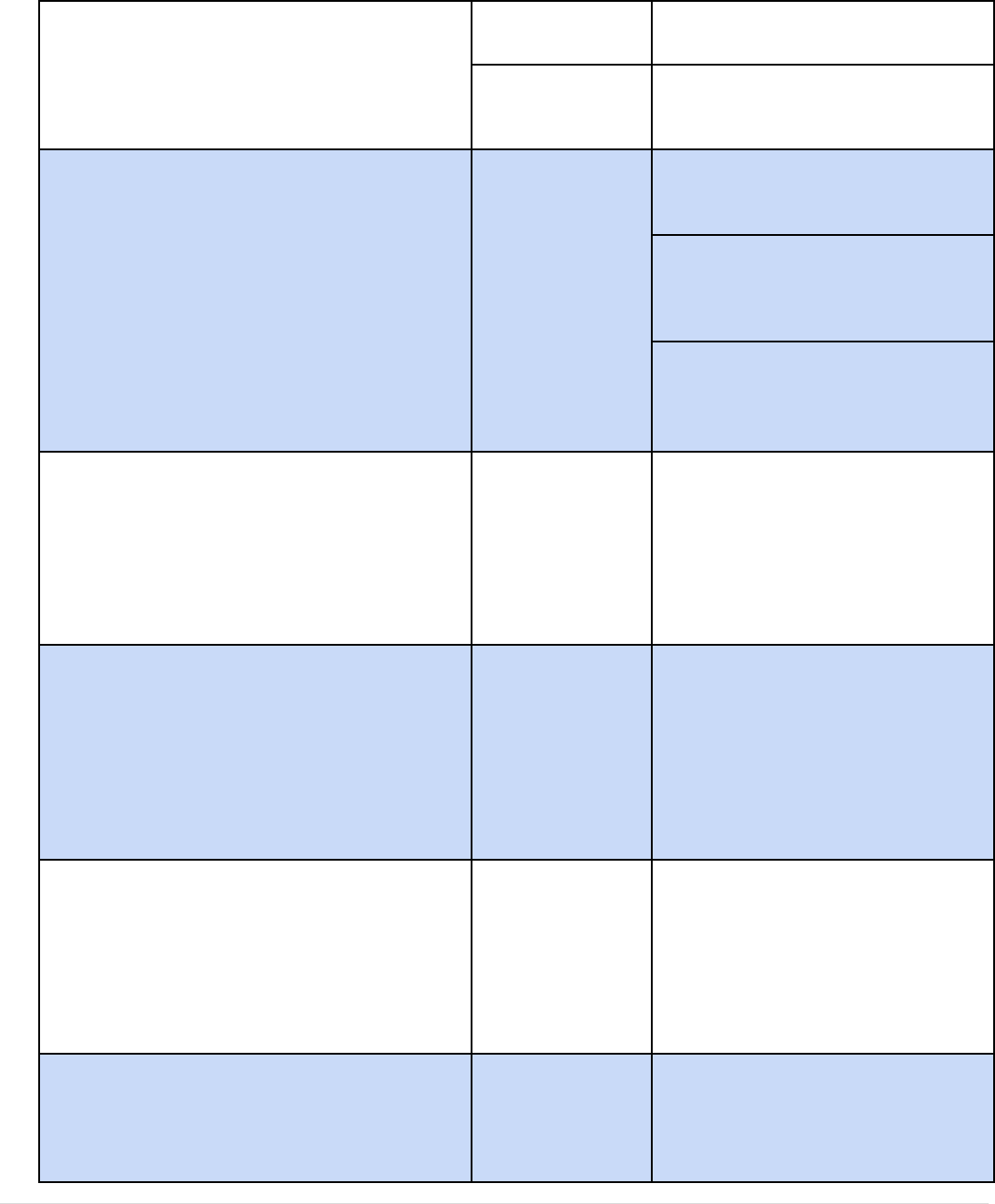
49 | Page
History and Physical (if needed) Signed and dated by
Healthcare Provider
CVS
Walgreens
CVS/Walgreens can usually be scheduled within
1-2 days.
Clinics
Doctor’s Office
Clinics/Doctor’s Office may take up to 1 month
to get an appointment
TB test results – one of the below
● PPD 1 step OR
● Quantiferon Gold Blood Test OR
● T-Spot Blood Test OR
If positive, clear Chest XRay within past 3 years
CVS
Walgreens
Clinics
Doctor’s Office
PPD takes 48-72 hours for results and is placed
at your appointment on your skin with a return in
48-72 hours to be read by the facility
Quantiferon Gold takes 3-5 days from the date of
the blood draw for results and is an order you
receive from the facility to go to a lab to have it
drawn
T-spot takes 2-3 days from the date of the blood
draw for results and is an order you receive from
the facility to go to a lab to have it drawn
Hepatitis B – one of the below
● Proof of 3 vaccinations OR
● Lab report of positive antibody titer OR
● Declination Waiver
Do not need to wait on doctor to order lab draw - can go
straight to QUEST and request the blood draw by asking for
a “Hepatitis B Antibody Titer”
CVS
Walgreens
Clinics
Doctor’s Office
Quest
Approximately 7-10 days from the date of the
blood draw for results
All clinics/offices will write an order for you to
go to the lab and have the blood drawn
M.M.R (Measles/Mumps/Rubella) – one of the below
● Proof of 2 vaccinations OR
● Lab report of positive antibody titer for all 3
components
○ 1 booster shot (if titer is negative or equivocal)
Do not need to wait on doctor to order lab draw - can go
straight to QUEST and request the blood draw by asking for
a “MMR Antibody Titer”
CVS
Walgreens
Clinics
Doctor’s Office
Quest
Approximately 5-7 days from date of blood draw
All clinics/offices will write an order for you to
go to the lab and have the blood drawn
Varicella (Chicken Pox) – one of the below
● Proof of 2 vaccinations OR
● Lab report of positive antibody titer
○ 1 booster shot (if titer is negative or equivocal)
Do not need to wait on doctor to order lab draw - can go
straight to QUEST and request the blood draw by asking for
a “Varicella Antibody Titer”
CVS
Walgreens
Clinics
Doctor’s Office
Quest
Approximately 3-5 days from date of blood draw
All clinics/offices will write an order for you to
go to the lab and have the blood drawn
Tdap
● Tetanus booster administered within 10 years
CVS
Walgreens
Clinics
CVS/Walgreens can usually be scheduled within
1-2 days.
Clinics/Doctor’s Office may take up to 1 month
to get an appointment
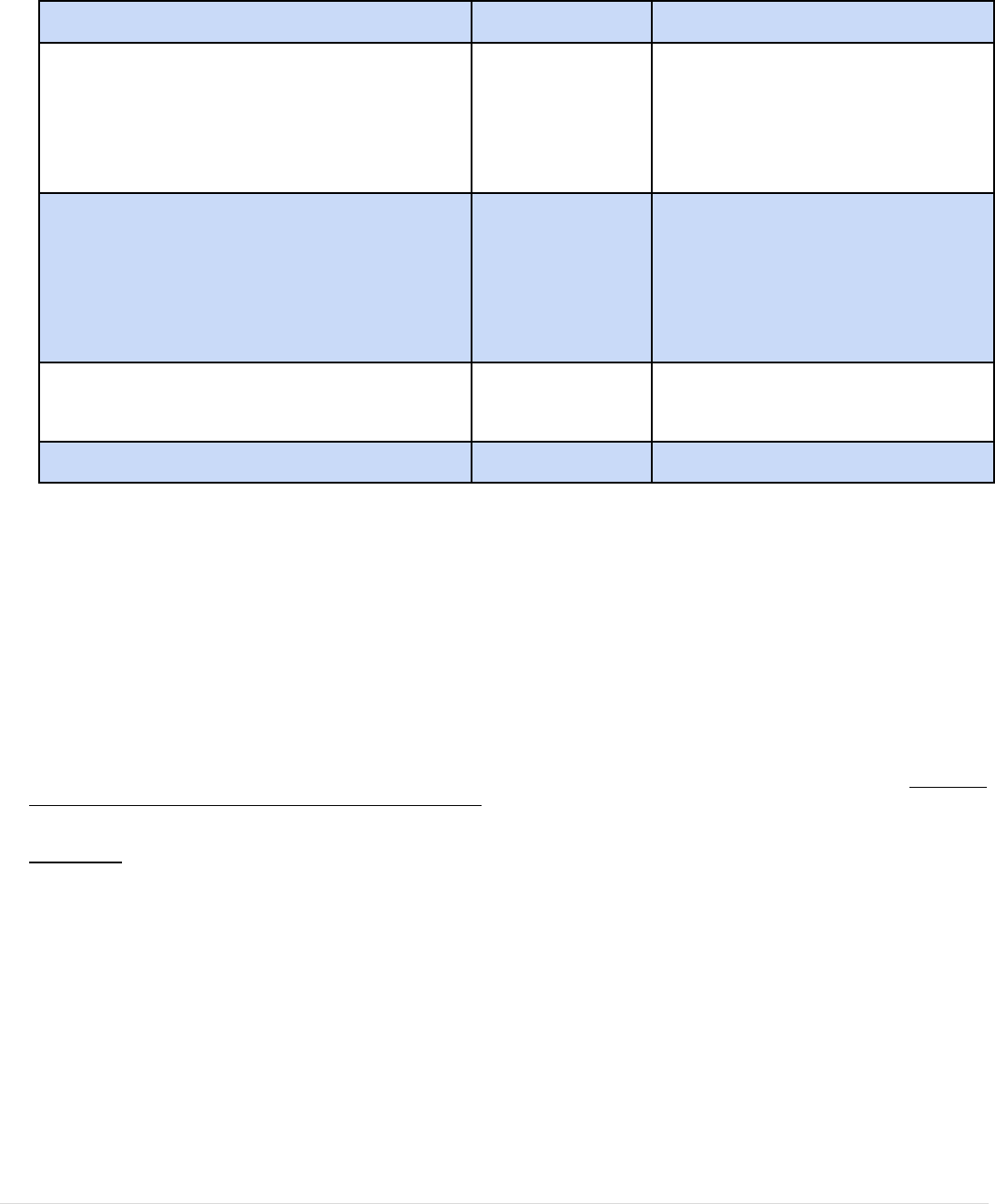
50 | Page
Doctor’s Office
Flu
● Proof of annual vaccination (September - March)
CVS
Walgreens
Clinics
Doctor’s Office
CVS/Walgreens can usually be scheduled within
1-2 days.
Clinics/Doctor’s Office may take up to 1 month
to get an appointment
COVID Vaccine
● Proof of full vaccination series
○ Based on Clinical Site Requirements
CVS
Walgreens
Clinics
Doctor’s Office
Based on availability
Proof of Medical Health Insurance
Form in Castlebranch
2-3 days once submitted for approval
ATS Insurance Responsibility Form
Form in Castlebranch
2-3 days once submitted for approval
Note: Throughout the nursing curriculum, the student must monitor the TB, PPD/X-Ray, CPR certification, COVID boosters and any other medical
document with an expiration date to ensure that they are current and on file in the Nursing Department Office. Students who do not meet the
medical compliance requirements by the given deadline in ATS email communications will not be enrolled in courses with a clinical component.
Students are responsible for all fees related to immunizations and drug testing.
In addition, failure to submit documents within this time frame will result in a late fee charged in the amount of $100.00 dollars.
All ATS Institute clinical sites are requiring students placed in their clinical facilities to be fully vaccinated.
Although ATS Institute does not require the COVID-19 vaccine for students, if a student is not vaccinated for COVID-19, the clinical facility will
make the final determination to grant or deny placement at their facility.
Failure to accurately disclose your vaccination status will cause you to be ineligible for placement at a clinical site and will result in failure of the
course. Attendance at clinical sessions is mandatory to pass courses with a clinical experience requirement.
Students who wish to request a waiver of the vaccine requirement can reach out to the admissions department to receive a waiver form. The clinical
facility, not ATS, will decide to grant or deny a request for a waiver. The purpose of the form is to facilitate your request for a waiver based on a
medical condition which represents a contraindication for the vaccine, or a waiver that is based on religious grounds.
ATS Release
ATS does not require the COVID-19 vaccine for students, a vaccine waiver request does not guarantee approval from the clinical sites that a student
may be placed with. ATS Institute is released from any and all rights, claims, and causes of action arising from clinical placement due to a student’s
COVID-19 vaccine status.

51 | Page
Appendix G: Exit Examination Score Determination
The ATI Comprehensive Predictor is a standardized test that assesses the students’ preparedness for the NCLEX-PN. Acceptable performance is
72% or higher composite score. If the benchmark is changed at any time, it will be posted in an addendum to the catalog and will apply to students
in the incoming and subsequent cohorts.
The school reserves the right to change the exit exam and NCLEX prep provider.
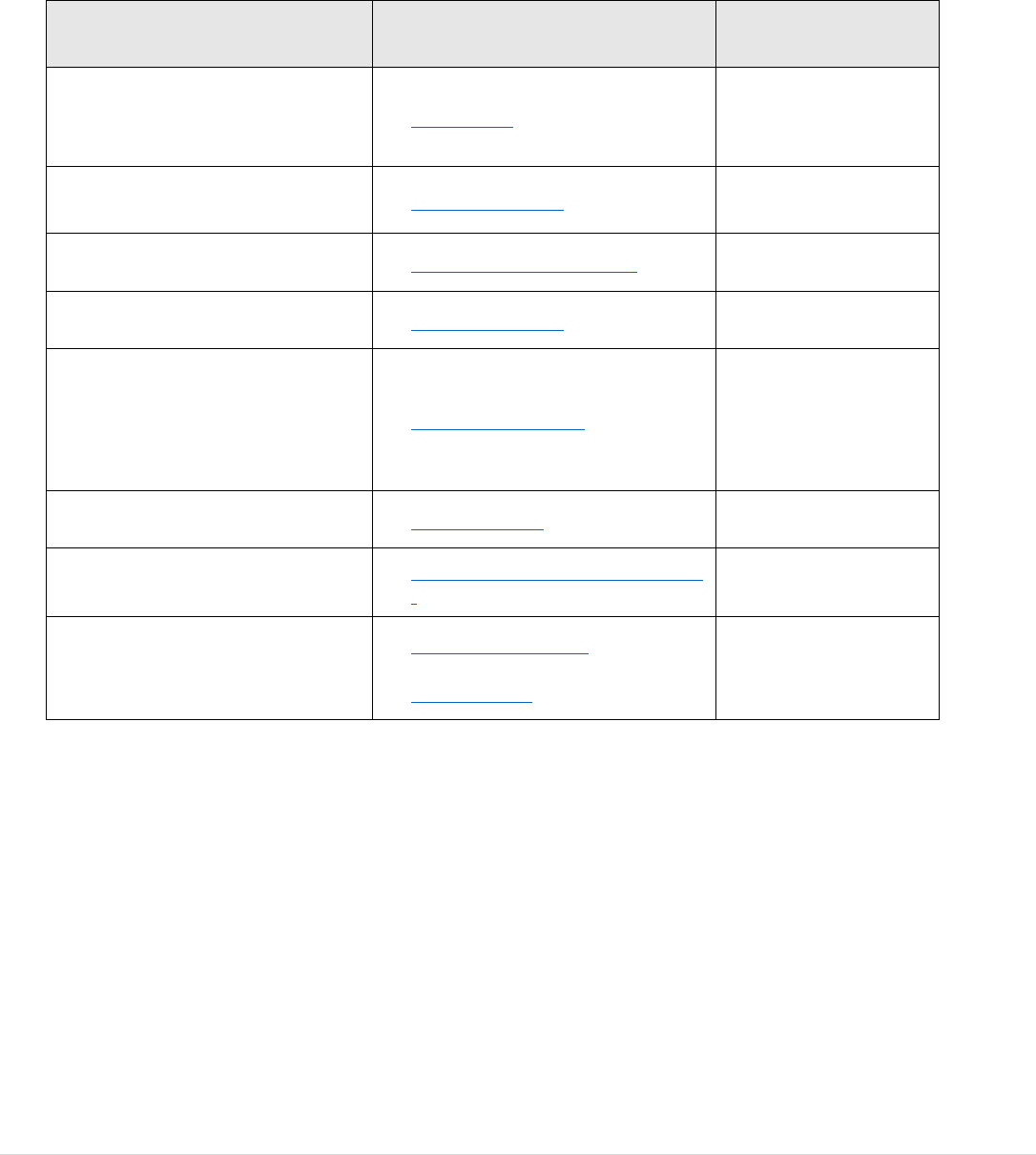
52 | Page
Appendix H: Local and National Community Resources
Whatever you are going through, you do not have to go through it alone. Reach out for support and for yourself or your loved ones. You are not
alone!
Organizations
Website
Phone Number
Alcohol Abuse and Crisis
Intervention
www.aa.org
(800) 234‐0246
Al‐Anon
www.al-anon.org/
(888) 425‐2666
Drug and Alcohol Helpline
www.alcoholdrughelp.org/
(800) 688-4232
Family and Children’s Services
www.acf.hhs.gov/
See website
National Domestic Violence
Hotline
www.thehotline.org/
(800) 799-7233 OR
Text LOVEIS to
(866) 331-9474
Rape Crisis Center
www.rainn.org/
(800) 656-4673
Suicide Hotline
www.suicidepreventionlifeline.org
/
(800) 273‐8255
United Way
www.unitedway.org/
OR
www.211.org/
211
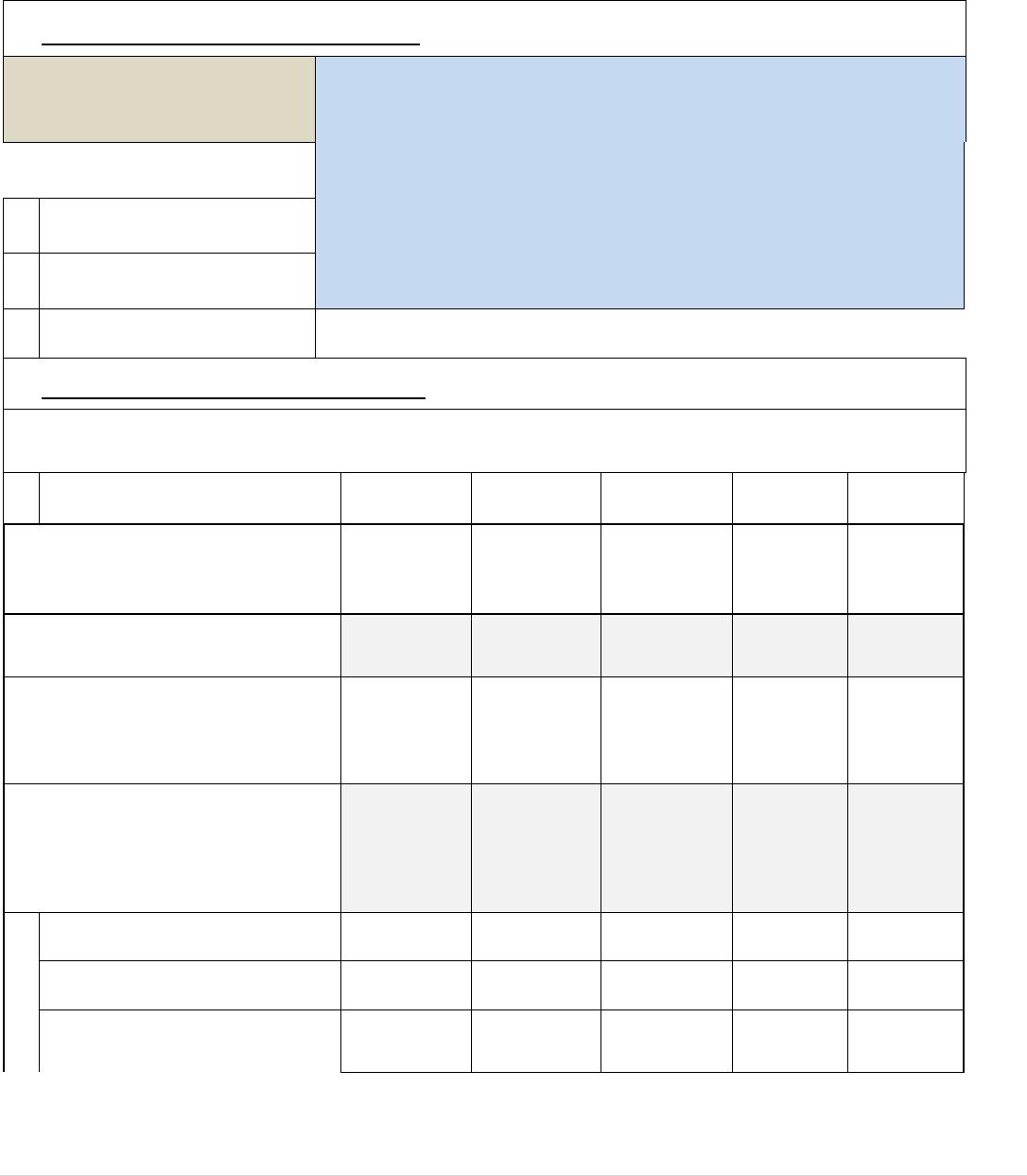
53 | Page
Appendix I: Institutional Disclosures Report
Reporting Period: July 1, 2021 - June 30, 2022
INSTITUTION NAME: MDT
School of Health Sciences, Inc.,
dba ATS Institute of Technology
Indicate all ways the disclosure information is distributed or made available
to students at this institution:
X
Attached to Enrollment Agreement
X
Provided in Current Academic Catalog
X
Reported on School Website
Per Section 1095.200 of 23 Ill. Adm. Code 1095:
The following information must be submitted to the Board annually; failure to do so is grounds for immediate
revocation of the permit of approval.
DISCLOSURE REPORTING
CATEGORY
Practical
Nursing
Program
A) For each program of study, report:
1) The number of students who were
admitted in the program or course of
instruction* as of July 1 of this
reporting period.
233
2) The number of additional students
who were admitted in the program or
course of instruction during the next
12 months and classified in one of the
following categories:
a) New starts
270
b) Re-enrollments
13
c) Transfers into the program
from other programs at the school
0
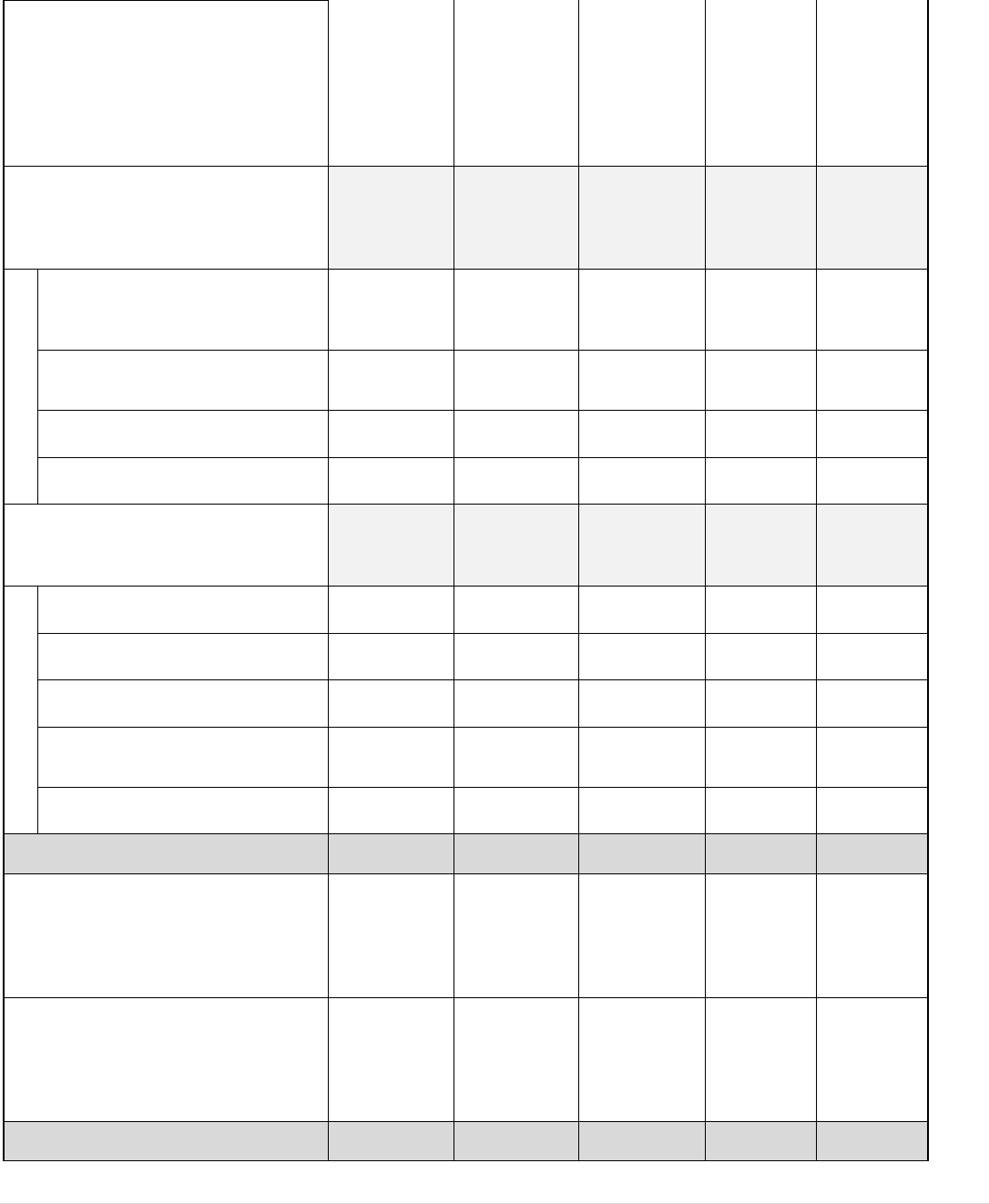
54 | Page
3) The total number of students
admitted in the program or course of
instruction during the 12-month
reporting period (the number of
students reported under subsection A1
plus the total number of students
reported under subsection A2).
516
0
0
0
0
4) The number of students enrolled in
the program or course of instruction
during the 12-month reporting period
who:
a) Transferred out of the program
or course and into another
program or course at the school
0
b) Completed or graduated from
a program or course of instruction
109
c) Withdrew from the school
155
d) Are still enrolled
253
5) The number of students enrolled in
the program or course of instruction
who were: Updated as of 5/15/2023
a) Placed in their field of study
89
b) Placed in a related field
10
c) Placed out of the field
0
d) Not available for placement
due to personal reasons
1
e) Not employed
10
B1) The number of students who took
a State licensing examination or
professional certification
examination, if any, during the
reporting period.
104
B2) The number of students who took
and passed a State licensing
examination or professional
certification examination, if any,
during the reporting period.
81
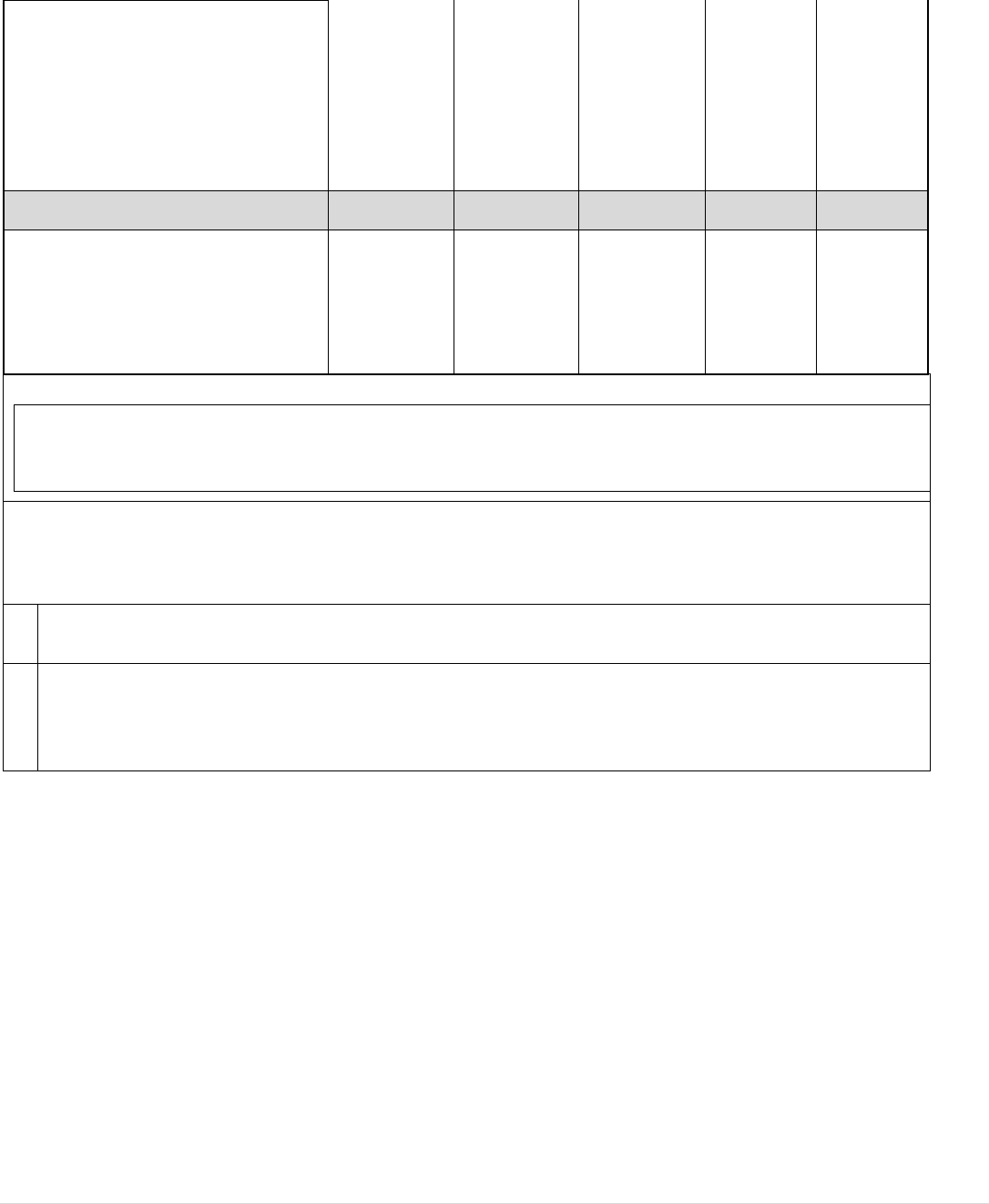
55 | Page
C) The number of graduates who
obtained employment in the field who
did not use the school's placement
assistance during the reporting period;
such information may be compiled by
reasonable efforts of the school to
contact graduates by written
correspondence.
unknown
D) The average starting salary for all
school graduates employed during the
reporting period; this information may
be compiled by reasonable efforts of
the school to contact graduates by
written correspondence.
unknown
*Course of Instruction is defined as a standalone course that meets for an extended period of time and is
directly creditable toward a certificate or other completion credential; individual courses that make up a
Program of Study are not considered courses of instruction.
Note: As indicated in the PBVS Administrative Rules, Section 1095.200, student retention and graduation rates
must be maintained that are appropriate to standards in the field. Furthermore, a State licensing examination or
professional certification examination passage rate of at least 50% of the average passage rate for schools within
the industry for any State licensing examination or professional certification examination must be maintained.
} In the event that the school fails to meet the minimum standards, that school shall be placed on probation.
} If that school's passage rate in its next reporting period does not exceed 50% of the average passage rate of that
class of schools as a whole, then the Board shall revoke the school's approval for that program to operate in this
State. Such revocation also shall be grounds for reviewing the approval to operate as an institution.

56 | Page
Appendix J: Minimum Computer System Requirements Policy
Students enrolling in a program at ATS must have regular access to a device with high-speed internet access that complies with the
Minimum System Requirements as follows:
Recommended
Minimum
PC
MAC
PC
MAC
Operating System
Windows 10,
version 21H1 or
superior
Monterey or superior
Windows 10,
version 21H1 or
superior
Big Sur or superior
Processor
Intel or AMD with virtualization instruction support VT-x/AMD-V
(Intel Core i3 VIII and superior)
Memory
16GB
8GB
Free Hard Disk Space
60GB SSD
30GB
Additional Hardware
WiFi network adapter with WPA2 Enterprise support, Microphone, Webcam
Internet Connection
45 Mbps (download) or better
20 Mbps or better
Internet Browser
Chrome Browser
Microsoft Office
Students may use Google products; Docs, Slides, Sheets, etc
Adobe Acrobat Reader
Students can download the Adobe Reader for free, or Google Docs can read the PDF
document.
Accessibility Technology
(if needed)
ATS LMS contains accessibility features for the following assistive technology needs:
● Speech to text software
● Screen reader software
The following service will be available upon request.
● Magnification devices and software
Anti-Malware
Malwarebytes 3.0 or superior – or equivalent security software
Devices that do not
support our education.
Chromebooks, Linux/GNU-based Operating Systems.
Mobile Device Support
Our LMS is mobile device ready. As a result, the student can use the mobile device to
access the LMS and complete the majority of the required activities. However, the use
of mobile devices may be prohibitive for some of their learning experiences and at
clinical sites. Our clinical virtual experience and exam delivery software (Shadow
Health, SwiftRiver, and, ExamSoft) do not operate on any mobile devices, including
iPhones, iPads, Android phones, and tablets.
57 | Page
Appendix K: Standardized Testing Progression Policy
Note: The testing provider is subject to change.
Students that score below the required benchmark (set by ATS) on Content Mastery Assessments in ATI are at higher risk for being unsuccessful
in the program. This policy is designed to support students through a progression and to assist them with success throughout the program and
ultimately the end of the program assessments. All benchmark scores will be posted in the course syllabus.
Students who entered nursing courses prior to Fall 2023:
Students who did not meet the benchmark score on the Content Mastery assessments prior to Fall 2023, will be placed in Academic monitoring
and required to complete an Individualized Learning Plan in lieu of repeating courses or slowing down progression.
Seminar Course (Transition to Practice) - before the student progresses into REV:
The student must take the following ATI Content Mastery Assessments during midterm and meet the required benchmark score on the following
assessments:
● Pharmacology
● Medical Surgical
1. If the student does not meet the benchmark score on any assessment above, the student will:
a. Meet with the Nursing Coach on a weekly basis to review needed content.
b. Complete the ILP. Failure to complete the ILP will result in failure of the Seminar course.
c. Be retested prior to the end of the Seminar course.
d. If the student does not meet the benchmark score at this attempt the student will fail the Seminar course. While
e. repeating the Seminar course a student will be required to take and pass an assigned clinical rotation. Fee for clinical
f. rotation will apply.
Students who entered nursing courses during or after Fall 2023:
Seminar Course (Transition to Practice):
The student must take the assigned ATI Content Mastery Assessments and meet the required benchmark score of Level 2 to pass the course.
1. If the student does not meet the benchmark score on assessment on the first attempt, the student will:
a. Meet with the Nursing Coach on a weekly basis to review needed content.
b. Complete the ILP. developed by the nursing coach. Failure to complete the ILP will result in failure of the Seminar course.
c. Be retested prior to the end of the semester.
i. If the student does not meet the benchmark score at this attempt the student will fail the Seminar course. While
repeating the Seminar course a student will be required to take and pass an assigned clinical rotation. Fee for clinical
rotation will apply.

58 | Page
Appendix M: Entrance Exam and Placement:
Entrance Exam
Prospective students are required to pass the ACCUPLACER Exam with the required score determined by the school faculty and administration to
proceed with the admissions process.
Entrance Exam Benchmarks:
English - 234
Math - 230
Test results are valid for a period of one year. If the section was successfully completed on different dates, the results will expire after the earlier
test date.
Course Placement
To succeed in the program, it is important for students to have the required level of proficiency in English language and math.
Nursing Courses
Students who receive a 250 in English and a 263 in Math on the ACCUPLACER Entrance Exam will be allowed to sit for the TEAS test. Students
reaching the composite score of at least 45% on the TEAS exam will be placed directly into nursing courses.
Developmental Courses
Students who met minimum ACCUPLACER benchmark scores but did not meet benchmark scores to sit for the TEAS exam will be enrolled in
the corresponding developmental courses or retake TEAS exam for the following admission cycle.
Developmental courses include ENG0930, ENG0935, and MAT0930.

59 | Page
Appendix N: Readmission Guidelines
Readmission Guidelines
1. Students must request their intent for readmission in a written appeal. The readmission letter of intent form is located on the
ATS website. Only submissions submitted via the online form 30 days prior to the beginning of the semester will be accepted for
review. The letter should include a reflection on the reason for the withdrawal as well as the plan to successfully complete the
program.
2. Must meet with the Bursar’s office to verify there are no current account balances.
3. The Admission’s office will schedule the student for required testing and provide the student with the appropriate paperwork needed for the
readmission appeal request.
a. For nursing coursework, the required testing will be determined by the courses the student passed in the program
prior to withdrawal.
b. The student must score the required benchmark on the standardized ATI assessments to be granted consideration
for progression in the nursing sequence.
c. If applicable, students must test and meet the required benchmark levels for all courses noted below. If the student does not meet
the required benchmarks, those classes will be added to their plan of study.
i. Fundamentals
ii. Maternity/Pediatrics
iii. Mental Health
4. Students must ensure all components are completed in CastleBranch to be medically cleared for courses. Students will obtain
access to CastleBranch from the Admissions Department. This includes:
a. New background check
b. Current drug screen
c. Medical Compliance as per appendix F
5. After the required testing, the Admission’s office will schedule the student for a meeting with the Enrollment Appeals Committee
(EAC).
6. The student will be notified of the decision in writing within 3 business days of the committee meeting.
7. If approved, the student will complete the required lab skills review for the nursing course sequence recommended by the testing
results prior to registration. A student unable to perform required skills must take the prior course sequence or will be denied
readmission.
8. The decision by the Enrollment Appeals Committee is final.
9. If a student is granted re-admission, the student is subject to the student handbook in place in the semester of enrollment of the
first class.
10. If a student is readmitted they will be required to meet with the retention specialist and nursing coach per the plan developed for
them for success.
11. In the event a student exceeds 150% of the maximum time frame allowed to complete the program, the student may submit a
Maximum Time Frame appeal. In cases where the appeal is granted, students may continue with readmission.
12. Only one appeal opportunity will be considered. An appeal granted or denied constitutes the final opportunity for a student to
complete the Nursing Program.
Readmission into ATS Institute of Technology will be dependent on space available to accommodate additional students. If the number of accepted
applicants exceeds available space, the decision will be based on the student’s GPA and academic history of coursework previously taken at ATS
Institute of Technology and applicants may be deferred to a subsequent semester.

60 | Page
Appendix O: Repeating Course Guidelines
Developmental Course(s) Failure - Registration Warning
A student who failed one or more developmental courses on their first attempt will be placed on Registration Warning status and must submit a
letter to the Registrar office requesting an automatic enrollment to continue in the practical nursing program.
1. Students must submit a written request for automatic enrollment. Only requests using the Repeat Request Form will
be sent to the Registrar Office for review and approval within 2 business days of the known course failure. The form
should include a reflection on the reason for the course failure as well as progress toward resolution.
2. The Student will be notified via their ATS email within 5 business days of the results of their request for automatic
enrollment. If approved the letter of warning will include details of the requirements needed to complete Academic
Monitoring.
3. If approved, students will be required to meet with the retention specialist for an academic success plan.
These following guidelines pertain to students who fail a Nursing (NUR), Biology (BIO), or REV course.
First Course Failure - Registration Warning
A student seeking a nursing, biology or REV course repeat after the first course failure will be placed on Registration Warning status and must
submit a letter to the Registrar office requesting an automatic enrollment to continue in the practical nursing program.
1. Students must submit a written request for automatic enrollment. Only requests using the Repeat Request Form will
be sent to the Registrar Office for review and approval within 2 business days of the known course failure. The form
should include a reflection on the reason for the course failure as well as progress toward resolution.
2. The Director of Nursing or their designee will review the Repeat Request Form. The Director of Nursing may approve or
deny the request for automatic enrollment.
3. The Student will be notified via their ATS email within 5 business days of the results of their request for automatic
enrollment. If approved the letter of warning will include details of the requirements needed to complete Academic
Monitoring.
4. If approved student will need to meet with the nursing coach for a academic success plan
5. Registration is dependent upon openings in the nursing sequence courses.
Second Course Failure - Registration Suspension
A student who fails a second course as described above, will be placed on registration suspension. The student is not meeting satisfactory
academic progress and will not be registered for the following semester. The student may petition the school by Registration Appeal for a
Registration Probation status - A status assigned to a student who is failing to make satisfactory academic progress and who successfully appeals
the registration suspension.
Registration Appeal Process
A student must submit a registration appeal to remove the registration suspension. If the registration appeal is approved, the student will
be placed on Registration Probation status. The appeals process is as follows:
1. The student must write an appeal using the Registration Appeal Form. Only requests using the form will be sent to
the Registrar’s Office for review. The Registration Appeal form must be received within 2 business days of the
notification of course failure.
2. The Registrar's office will schedule the student with the Enrollment Appeals Committee (EAC) after the appropriate
documentation is received.
3. The student will be notified of the decision in writing within 3 business days of the committee meeting.
4. If a student appeal is approved, and the student does not return the following semester, the registration probation
status remains in place.
5. The decision by the Enrollment Appeals Committee is final.
6. An appeal granted or denied constitutes the final opportunity for a student to complete the Nursing Program. If a
student is unsuccessful in any nursing course following an appeal, there is no re-admission.
Registration Probation
A student on Registration Probation status is required to participate in any advising and tutoring that are considered to be necessary
by the college. The plan of study will be adjusted per committee recommendations and Program Administrator review. This may
include a decreased course load in one or more semesters. Failure to participate per the Individual Learning Plan, Academic
Monitoring, and scheduled meetings may result in dismissal. See Academic Monitoring Policy.
Third Course Failure – Dismissal
A student that fails a third course is academically dismissed from the program. Readmission will be denied for students dismissed for academic
performance and/or not in compliance with the Progression Policy guidelines.

61 | Page
Appendix P: Indiana Resident Refund Policy
The college shall pay a refund to the Indian resident student in the amount calculated under the refund policy specified in this section.
The college will make the proper refund no later than thirty-one (31) days of the student’s request for cancellation or withdrawal.
The following refund policy applies to each Indiana student resident:
The student is entitled to a full refund if one or more of the following criteria are met:
a. The student cancels the enrollment application within six business days after signing.
b. The student does not meet the school’s minimum admission requirements.
c. The student’s enrollment was procured as a result of a misrepresentation in the written materials utilized by the school.
d. If the student has not visited the school prior to enrollment and withdraws within three days of touring the school or
attending the regularly scheduled orientation/classes.
After beginning classes, Indiana student residents who withdraw from the school are entitled to the following refund amounts less
an enrollment fee of ten percent (10%) of the total tuition, not to exceed one hundred and fifty dollars ($150):
a. After attending one week or less, ninety percent (90%).
b. After attending more than one week but equal to or less than twenty-five percent (25%) of the program, seventy-five
percent (75%).
c. After attending more than twenty-five percent (25%) but equal to or less than fifty percent (50%) of the program, fifty
percent (50%).
d. After attending more than fifty percent (50%) but equal to or less than sixty percent (60%) of the program, forty percent
(40%).
e. After attending more than sixty percent (60%) of the program, the student is not entitled to a refund.

62 | Page
Appendix Q: Civility Code of Conduct
Vision for Civility - Shared Responsibility It is everyone’s responsibility in the School of Nursing to have an attitude of civility
and professionalism in fulfillment of the mission, values, and norms of ATS Institute.
Civility will be openly discussed throughout the program.
Civility in nursing education will prepare students for civility in nursing practice.
Graduates will be competent to function effectively within license practical nursing and interprofessional teams, fostering open
communication, mutual respect, and shared decision- making to achieve quality patient care.
Definitions:
• Civility – Authentic respect for others when expressing disagreement, disparity, or controversy; it involves time, presence,
a willingness to engage in genuine discourse, and a sincere intention to seek common ground (Clark, C. M., & Dunham,
M. 2020).
• Incivility – Rude or disruptive behaviors which often result in psychological or physiological distress for the people
involved – and if left unaddressed, may progress into threatening situations (Clark, C. M., & Dunham, M. 2020).
Civility Code of Conduct Pledge
I pledge:
1. To foster open communication and a positive learning environment:
2. I will practice goodwill towards others.
3. I will be open to addressing specific concerns, attitudes and behaviors.
4. I will acknowledge my mistakes and make amends to correct my mistakes.
5. I will explore different perspectives and ideas when considering a situation before making an assessment or determination.
6. I will respect privacy when approached in confidence.
7. I will follow the chain-of-command when communicating concerns or problems.
8. I will refrain from promoting rumors through valid research and proper chain-of- command.
9. I will not listen to or participate in gossiping.
10. I will attempt to resolve my problems with those directly involved. I understand I can include an authority in the discussion to
assist with mediation.
11. I will redirect and report uncivil behavior to leadership.
12. I will be responsible for my attitude and words when discussing concerns. For example: speaking in “I” language, avoiding
blame, using facts with specific examples, and focusing on the topic/point in discussion. Lastly, I am responsible for an
acceptable resolution for all parties involved.
13. I understand that I am responsible for my attitude, behavior and communication in spoken or written word, deed or action. To
be approachable and open to feedback:
14. I will take responsibility for my actions and words.
15. I will take time to reflect on what was said, rather than blaming, defending, or rejecting.
16. I will ask for clarification of the perceived behaviors.
17. I will remember that there’s always a little bit of truth in every criticism.
18. I will stay focused on what I can learn from the situation. To keep patient and caregiver safety and welfare as the primary
concern in all interactions
19. I will be vigilant and monitor for care practices that increase risks of errors.
20. I will remember that no one is perfect and that all humans are vulnerable to making mistakes.
21. I will take responsibility for being “a safety net” when helping co-workers and fellow students, anticipating what they may
need, and pitching in to prevent mistakes (e.g., “I think that glove is contaminated; let me get you a new one.” Or “Here’s a

63 | Page
new needle.”) • I will make it a team principle that “If I witness unethical or unsafe practices, it’s my responsibility to address
it” (first directly with the person involved, then through policies and procedures if needed).
22. I will accept the diversity in our styles—recognizing that you know yourself best and should be allowed to choose your own
approaches.
23. I will promise to be honest and treat others with respect and courtesy.
24. I will treat others as they want to be treated, not assuming they have the same desires you do).
25. I will listen openly to new ideas and other perspectives.
26. I will commit to resolve conflict without resorting to using power.
27. Make decisions together as much as possible. Realize that we’re accountable for the outcomes (consequences) of our actions.
28. Have the right to say no, so long as it doesn’t mean neglecting responsibilities.
29. Student non-compliance with this policy will result in consequences that may include unsatisfactory probation, suspension,
and/or dismissal from the program based on the severity of the breach or repeated infraction.

64 | Page
Appendix R: ATS Exam Guidelines
ATS adheres to a strict procedure for taking and reviewing exams. The procedure to be followed prior to taking an examination or
reviewing an examination is as follows:
1. Students are required to use computers on campus.
2. Students will not be allowed to have any other their personal belongings [including backpacks, purses, bags, notes, sunglasses,
hats, coats, smart watches, and cellphones] in the testing area. These items will have to be placed either at the front of the
classroom, in their cars, or in another room during testing time.
3. All electronic devices should be turned off, including smart watches, tablets, and cell phones.
4. If a student is found to have a cell phone during testing or a review session, the exam/exam review will be ended, and student
receives a zero for the exam.
5. No food will be allowed in the on-campus computer room. A clear water bottle with no label is allowed.
6. Students need to bring a photo ID such as a government-issued or campus-issued ID to the testing area.
7. All students will be required to sign in at the start of the test.
8. Calculators, scratch paper, and pencils will be provided by ATS for on campus exams. Students may NOT use their own
calculator or cell phones for on campus exams/quizzes. The calculator, pencil, and paper must be returned to the testing proctor at
the end of the examination.
9. Only the testing window/tab may be open during the exam. If any additional windows/tabs are opened during the exam, the exam
will be ended, and student receives a zero.
10. Students are to raise their hand if they have a question; if they leave their seat without permission or leave the room, the student’s
exam attempt is ended. In the rare circumstance where a student is sick or if they must use the bathroom, the student may leave
only if accompanied by an ATS employee.
11. After the student finishes the individual test, they are to log off their computer and leave quietly.
12. Students are not allowed to re-enter the exam area or congregate outside the exam room.
13. Campus tests will begin promptly at the designated date and time. All students are expected to be in the classroom/testing room at
the scheduled date and time.
14. If a student is not in the classroom/testing room when the test begins, the student will not be permitted to enter the room
to take the exam.
15. Make up exams will only be granted for emergent situations with proper documentation and instructor [not nursing proctor]
approval prior to taking the exam.
16. Documentation must be submitted to the instructor as soon as possible after the emergent event which will be considered on a
case-by-case basis.
17. Make up exam arrangements must be made through your instructor.
Exam Reviews
All students that earn less than 78% on an exam will receive Academic Monitoring and be required to meet with the nursing
coach/instructor.

65 | Page
Appendix S: ATS Clinical Expectations
1. Professionalism
1. Must always maintain positive and respectful attitude to the faculty, facility, staff and clients. This includes but is not limited
to eyerolling, other negative physical gestures, and/or negative verbal comments, speaking negatively, or complaining.
2. Be physically and emotionally present and engaged during clinical experience. Go above and beyond; help others when
needed without them having to ask. Be enthusiastic about the chance to help, be open to learning something new from the
experience.
3. Be aware of how your body language, actions, and words may be perceived.
4. Patients come first at all times, their safety, health and well-being is our top priority.
5. Clinical paperwork is prioritized after patient care is complete. Clinical paperwork must be completed at the site and handed
in to the faculty at the end of the clinical day.
6. Be completely engaged during your clinical times to achieve the best learning experience possible. This includes spending
time with your patient during all activities such as PT, OT, Rehab, MD Rounds, Nurse Rounds, etc.
7. Answer any and all call lights regardless of whose patient it is. Let them know you are happy to help. Remember to check for
fall risk, etc... before getting a patient up. When in doubt about something, you should always ask.
2. Attendance
Student must arrive to clinical on time to receive patient assignment/ preconference. Clinical starts exactly at the designated time,
students that are tardy may be sent home and it will be considered a clinical absence.
1. Any lack of preparation for clinical, even including paperwork that is not completed will result in an unsatisfactory for the
day.
2. Failing to inform your instructor of your absence at least an hour in advance will result in an unsatisfactory grade for the day.
3. Most clinical rotations starts exactly at 7:00am - tardiness is considered more than 1 minute late.
Start times for the some of the facilities may vary – details will be provided by nursing faculty
4. A student who is unable to attend clinical must notify the clinical instructor at least 2 hours prior to the clinical start time
[by phone, not email]
5. Clinical days or portions of clinical days cannot be missed. Make up clinical day is only granted in extreme cases for students
that miss a clinical because of a sudden illness or personal family emergency. The student is required to present relevant
documentation to their instructor within one week of the absence.
6. Students are required to attend all clinical hours to meet the objectives and pass the clinical course [exceeding more than one
absence will prevent students from meeting this requirement].
7. It is not always reasonable or feasible for faculty members to offer a “make-up” or alternate experience that would meet the
learning objectives.
8. Plan accordingly and make sure you attend all your scheduled clinical days and arrive on time.
9. “No Show/No Call” for clinical may result in clinical failure.
10. Health conditions that need medical treatment require a medical release to return to clinical.
11. If you are pregnant, it is important to immediately provide your instructor with a medical release for full clinical
participation.
3. Dress Code
Must maintain professional appearance/conduct at all times (Please refer to ATS student handbook for reference).
Student must follow dress code for clinical/lab/simulation – consequences if not following dress code include: being sent home
[clinical], written assignment given by instructor [lab/sim]

66 | Page
• Facilities do not allow the use of cell phones and require them to be TURNED OFF while in patient care settings, your
clinical instructor will provide you with specific instructions during the clinical rotation.
• Air buds are not allowed to be worn during clinical
• As you will not have a locker, please limit the belongings that you bring to clinical. Bring only your driver’s license,
credit card/cash, which you can carry on your person.
4. Site Regulations
1. Must wear ID badge, bring stethoscope, bandage scissors, watch with second hand, penlight, black ink pen, clipboard with
paper, copy of care plan and report sheet. Students that DO NOT have these tools will be sent home for not coming prepared.
SIM is a clinical and held to the same preparation standards.
2. Instructor will assign lunch and breaks
3. STUDENTS ARE NOT PERMITTED TO LEAVE CLINICAL FACILITY FOR LUNCH
4. Please bring a non-refrigerated lunch or a small lunch cooler with ice packs. Some clinical facilities may have cafeterias to
purchase lunch.
5. Report to pre-conference as designated by your instructor
6. Report to post- conference as designated by your instructor.
7. All clinical sites are smoke free facilities this includes vaping.
8. No food or drinks are allowed in the nursing station or patient care areas.
68 | Page
Spring 2024 changes for current and incoming Students:
In addition to “Fall 2023 School Catalog”, the following policy changes are in effect and replace/update those original policies with
same name for the Spring 2024 semester for current and incoming students.
Note: When the entire policy is not listed, any part of the policy not listed in the table below remains in place unchanged.
Page #
Current State
Future State
5
Acceptance of Credits on Transfer
● Anatomy & Physiology with Medical
Terminology will be considered for transfer if
completed with a grade representing 80% on the
transcript grade scale or higher within the last 5 years.
Syllabi must be provided for review. If the course did
not include Medical Terminology, the student will be
required to pass Medical Terminology coursework
assigned by ATS.
Acceptance of Credits on Transfer
● Anatomy & Physiology with Medical
Terminology will be considered for transfer if
completed with a grade representing 80% on the
transcript grade scale or higher within the last 5 years.
Credits must reflect at minimum equal to the ATS
Anatomy & Physiology course. Courses that require
two courses for equivalency of transfer must both be
taken at the same institution. Syllabi must be provided
for review.
If the course did not include Medical Terminology, the
student will be required to pass Medical Terminology
coursework assigned by ATS.
6
Course Grading and Quality Points
Future state is added
Course Grading and Quality Points
Failure of any component associated with the course such as
lab or clinical experience will result in the student failing the
whole course.
7
Program Progression Policy
● Students in Math and Nursing Seminar courses
must receive an 80% or higher in both testing and
non-testing scores to successfully pass the course.
Program Progression Policy
● Students in the Math and Nursing Seminar
course must receive an 80% or higher in both
testing and non-testing scores to successfully pass
the course
8
Nursing Clinical Attendance
Tardiness Students are expected to arrive at all
sessions at least 10 min prior to scheduled start time
and complete the entire session.
Arriving more than 10 minutes late will result in an
absence and the student will be sent home for the day.
Absences: Absences due to extenuating
circumstances, See Make-Up Policy
Nursing Clinical Attendance
Tardiness Students are expected to arrive at all sessions
at least 10 min prior to scheduled start time and
complete the entire session.
Arriving more than 10 minutes late will result in an
absence and the student will be sent home for the day.
Absences: Absences approved for make up will be
charged a $100 make-up fee required to pay before
make-up, unless extenuating circumstances are
approved. See Make-Up Policy
9
Make-Up Policy
Students are expected to arrive 10 minutes prior to
exams and clinical experiences.
To avoid disruption during these times, students will
not be allowed entrance after the start of the exam or
clinical. Students who are absent or arrive late for
exams or clinical may be allowed a make-up if an
extenuating circumstance has occurred and faculty
are notified in advance when possible.
The instructor of the course will have the final
decision for an exam or clinical makeup due to
Make-Up Policy
Students are expected to arrive 10 minutes prior to
exams and clinical experiences.
To avoid disruption during these times, students will
not be allowed entrance after the start of the exam or
clinical. Students who are absent or arrive late for
exams or clinical may be allowed a make-up if an
extenuating circumstance has occurred and faculty are
notified in advance when possible.
The instructor of the course will have the final decision
for an exam or clinical or makeup due to extenuating
69 | Page
extenuating circumstances. Only one make-up is
allowed, per course.
Failure to notify faculty in advance can result in a “no
call, no show” and the student will not be allowed a
makeup. All requests for makeup must be initiated by
the student with the faculty as soon as possible and the
make-up must occur within the timeframe given.
Exam Make-up
Once an exam make-up is scheduled, it cannot be
canceled and rescheduled unless another extenuating
circumstance has occurred, and faculty are notified in
advance or no less than 24 hours of rescheduled exam
time. Make-up in these situations must occur within
the time approved by faculty.
A grade of zero shall be given in the event a student
does not attend a make-up exam or rescheduled make
up exam, there is no exception, and this is not
appealable.
Clinical Make-up
It is important to note that makeup is not guaranteed.
In the event a makeup is provided, the date and time
will be determined at the end of the semester by the
Director of Nursing. Clinical make-ups will not be
rescheduled.
Extenuating Circumstances
To qualify for an extenuating circumstance, students
must notify faculty prior to but no later than 48 hours
from the exam/clinical time, via the Emergency Absence
form located in the LMS.
circumstances. Only one make-up is allowed, per
course.
Failure to notify faculty in advance can result in a “no
call, no show” and the student will not be allowed a
makeup. All requests for makeup must be initiated by
the student with the faculty as soon as possible and the
make-up must occur within the timeframe given.
Exam Make-up
Exam makeups are not allowed unless proper
documentation for extenuating circumstances are
approved. If the student is allowed to make up the exam
the following apply:
● Only one exam per course, in a semester will be
considered for makeup. Any additional exam
tardies or absences will be counted as a zero
grade.
● Once an exam make-up is scheduled, it cannot be
canceled and or rescheduled unless another
extenuating circumstance has occurred, and
faculty are notified in advance or no less than 24
hours of rescheduled exam time. Make-up in
these situations must occur within the time
approved by faculty.
● A grade of zero shall be given in the event a
student does not attend a make-up exam or
rescheduled make up exam, there is no
exception, and this is not appealable.
Clinical Make-up
If the student is allowed to make up the clinical the
following apply:
● Only one clinical will be considered for makeup
during a semester. Additional absences will be
not be allowed or considered
● No call/No show from clinical will result in
absence without a makeup
● Clinical make-ups will not be rescheduled.
There is no exception, and this is not appealable.
It is important to note that makeup is not guaranteed. In
the event a makeup is provided, the date and time will
be determined at the end of the semester by the Director
of Nursing.
Extenuating Circumstances
To qualify for extenuating circumstances, students
must notify faculty at least 2 hours prior to the
exam/clinical, but no later than 24 48 hours from the
exam/clinical time via the Emergency Absence form
located in the LMS.
9
Extenuating Circumstances
To qualify for an extenuating circumstance, students
must notify faculty prior to but no later than 48 hours
Extenuating Circumstances
To qualify for an extenuating circumstance, students
must notify faculty at least 1 hour prior to the
exam/clinical, but no later than 24 hours from the
70 | Page
from the exam/clinical time, via the Emergency
Absence form located in the LMS.
exam/clinical time, via the Emergency Absence form
located in the LMS.
● Documented emergency transportation issue
(i.e, car breakdown, train breakdown, etc.., must
have proof provided)
9
Academic Monitoring
If the student is assigned to the Academic Monitoring
Program, the student will be notified by the instructor of
the course and/or the Retention Specialist.
Academic Monitoring
If the student is assigned to the Academic Monitoring
Program, the student will be notified by either the instructor
of the course and/or the , or a school official
See Appendix L: Academic Monitoring Guidelines
14
Violations of the Code of Conducts
● Using physical or verbal abuse, profanity, or
violence in any form.
Violations of the Code of Conducts
● Using physical or verbal abuse, profanity, or
violence in any form. Verbal abuse can
constitute any language deemed violent,
threatening, insulting, belittling, vulgar,
intimidating or any combination of the above.
17
Computer and Internet Use Policies
Purpose and Use:
The School workstations are to be used primarily for
research and academic purposes, with the School
students, faculty, and staff. The students will be
allowed to print research and academic papers. The
staff reserves the right to terminate an internet session
if its use is not research or curriculum orientated.
Moreover, the staff in charge reserves the right to ask
users to end a session and relinquish the computer to
a School student, faculty, or staff member.
Computer and Internet Use Policies
Purpose and Use:
The School workstations are to be used primarily for
research and academic purposes, with the School
students, faculty, and staff. The students will be
allowed to print research and academic papers. The
staff reserves the right to terminate an internet session
if its use is not research or curriculum orientated.
Students printing copyrighted material, personal
items, and/or excessive copies, may be terminated
from the printing session and placed on restricted
printing access. Moreover, the staff in charge reserves
the right to ask users to end a session and relinquish
the computer to a School student, faculty, or staff
member.
19
Professional Dress Code
No visible tattoos and body piercing (except
earrings) are allowed. Undergarments must not be
visible (color or design). White tee shirts should be
plain without any design or words. Solid white
nursing shoes or white leather athletic shoes
(without contrasting colors) must be in good repair
and always kept clean and polished. All shoes must
have no higher than a 1” heel and enclosed heel and
toe. Shoelaces are to be white only (refer to
document “Care and Maintenance of School
Uniforms” in the Nursing Programs Administrator’s
Office).
Professional Dress Code
No visible tattoos and,body piercing (except
earrings), or artificial eyelashes are allowed.
Undergarments must not be visible (color or design).
White or black tee shirts should be plain without any
design or words. Solid white or black nursing shoes
or white or black leather athletic shoes (without
contrasting colors) must be in good repair and always
kept clean and polished. All shoes must have no
higher than a 1” heel and enclosed heel and toe.
Shoelaces are to be white or black only (refer to
document “Care and Maintenance of School
Uniforms” in the Nursing Programs Administrator’s
Office).
24/30
Student Financial Assistance and Payment Options
Policy
Future state replaces these policies
Payment Options
Tuition Installment Payment Plan
During a student financial aid appointment, the financial
aid advisor provides the student with a financial
estimate that outlines estimated financial aid based on
71 | Page
the student's eligibility. ATS provides students who are
expected to pay out of pocket expenses with payment
plan options. All financial requirements need to be
completed and the first payment paid during the first
month of classes. A $10 late fee will be charged after
30 days past due.
If students have questions about methods of payment or
need to modify their payment arrangements, they may
contact the Bursar's office.
Financial Billing Agreements
All billing agreements must be in place before the
semester starts. Please consult with your Financial Aid
Advisor to confirm that the school received
certifications from the expected agencies.
The School will bill employers who pay tuition for their
employees. Students are to provide the School with a
signed letter of financial guarantee from the employer
prior to registration for classes.
30
Financial Procedures and Policies
Payment Requirements
Payment in full for semester tuition and any assessed
fees is due by the end of the first day of classes. The
payment plan may be requested with the Bursar office.
Financial Aid and Bursar services are available by
appointment.
Minimum Payment Requirements
1) Financial aid application processed by
the Department of Education and on file at the
School. Students MUST finish financial aid
verification, if any.
2) Full payment (payment must be
received and posted to your student account by
the due date).
3) Good standing in the installment
payment plan.
4) Confirmation of payment in the form
of scholarships and/or third-party authorization.
Students are required to monitor their account
balances.
All payment concerns/disputes are to be discussed
directly with the Bursar’s office. If a student disputes
charges with their bank and a chargeback occurs, the
student is responsible for immediately recovering the
charge back payment and providing a written
statement to the Bursar’s office explaining intentions
to honor the disputed payment. The student must
continue to follow minimum payment requirements.
Intentional and/or excessive disputes and chargebacks
may lead to dismissal from the program.
Students who are 15 days past due with payment will
be counseled by school officials and may be pulled
from classes. Students who do not meet the minimum
Financial Procedures and Policies
Payment Requirements
Payment in full for semester tuition and any assessed
fees is due by the end of the first day of classes. The
payment plan may be requested with the Bursar office.
Financial Aid and Bursar services are available by
appointment.
Students can access their payment portal through the
SIS with the online payment link uniquely assigned to
each individual student. Students will be able to see the
Payment Agreement and pay online. Billing questions
or concerns can be emailed to the Bursar’s office.
Questions concerning charges, payments, or credit
balances on the student account should be directed to the
Bursar's Office. Notices from the Bursar’s Office
concerning a student account are sent to the student’s
ATS email account. It is a student's responsibility to
ensure all requirements of their account are satisfied by
the payment deadline. Holds may be placed on a
student’s record whenever that student is delinquent or
has failed to pay any debt owed to the School or failed
to return any School property or equipment. Students
who are 10 days past due with payment may be
counseled by School officials.
Minimum Payment Requirements
1) Financial aid application processed by
the Department of Education and on file at the
School. Students MUST finish financial aid
verification, if any. If planning to use federal
funding, students must complete the “Free
Application for Federal Student Aid” (FAFSA)
with the ATS school code (034685) and must
finish financial aid verification, if chosen.
72 | Page
payment requirements listed above after 30 days, may
be placed on financial suspension until they clear their
balance.
2) Full payment (payment must be
received and posted to your student account by
the due date).
3) Good standing in the installment
payment plan (payment must be received and
posted to the student account by the due date).
4) Confirmation of payment in the form
of scholarships and/or third-party authorization.
All payment concerns/disputes are to be discussed
directly with the Bursar’s office. If a student disputes
charges with their bank and a chargeback occurs, the
student is responsible for immediately recovering the
charge back payment and providing a written statement
to the Bursar’s office explaining intentions to honor the
disputed payment. The student must continue to follow
minimum payment requirements. Intentional and/or
excessive disputes and chargebacks may lead to
dismissal from the program.
Students who are 15 10 days past due with payment
will be counseled by school officials and may be pulled
from classes. Students who do not meet the minimum
payment requirements listed above after 30 days may
be placed on financial suspension and/or financial hold
until they clear their balance.
Student Affairs Committee
Future state added
Student Affairs Committee
The Student Affairs committee replaces the academic
integrity committee and includes the review of academic,
behavioral, and disciplinary incidents or appeals.
Appen
dix S
ATS Clinical Expectations
Future state was added
ATS Clinical Expectations
5. Evaluation
A student who is evaluated as unprepared, unprofessional,
and or unsafe will be removed from their clinical course
until their performance or skills are remediated to
satisfactory.
1. Evaluation of clinical objectives will be
supported by faculty observation and
documentation. Faculty will follow the Clinical
Evaluation Rubric.
a. Students not meeting clinical
objectives will be notified by their
clinical instructor during the semester,
and will continually be updated as the
course progresses.
b. If the student demonstrates
unsatisfactory performance, during
their clinical, they will be required to
meet with their clinical instructor to
address how the performance can be
remediated.
2. If the student fails to improve their performance
after remediation, they will be required to attend
a conference with their clinical instructor. The
73 | Page
purpose of this conference is to determine if the
student can successfully complete the clinical
requirements of the course and allow the student
an opportunity to discuss views regarding their
performance and progress in the course thus far.
Should the conference support that the student
be placed on probation they will receive a
notice of intent for probation and must meet
with their Clinical instructor and Nursing
Program Director to review their probation.
a. If a student is placed on clinical
probation, they must complete all
remediation steps assigned to them.
Students are encouraged to meet
regularly with the required instructor.
3. Following these steps, if the student continues
to demonstrate unsatisfactory performance, they
will be given an unsatisfactory in clinical. An
unsatisfactory in clinical performance results in
failure of the course.
4. Students who failed clinical for cause related to
compromising patient safety will not be
considered for re-admittance.
11
Return from Leave Policy
Future state was added
Return from Leave Policy
● Comprehensive testing as assigned by the Director
of Nursing that corresponds to returning to the
plan of study.
● Test and perform clinical skills that corresponds to
returning to the plan of study
● If the exam or clinical skills benchmark is not met,
the student is required to remediate and meet
weekly with the ATS success coach and enroll in
the Focused Learning Seminar for the return
semester.
Student Corrective Action and Disciplinary Policy
This updated policy replaces the Corrective Action, Behavioral Violations, and 3 Step Violations “Write-Up” Policy on page 16
I. Student Corrective Action
The objective of Corrective Action is to address performance or behavior concerns and is not designed to be punitive in nature.
Corrective Action includes verbal warnings and written warnings.
Step 1: Corrective Action-Verbal Warning
A verbal warning is intended to help the student to be successful academically and to correct any inappropriate behavior. If a student
has behavioral or academic issues that are minor in nature but in need of correction the appropriate faculty member will issue a verbal
warning to them.

74 | Page
If the issue occurs outside of the classroom or with another employee, the Student Success Representative will meet with the student
and may issue a verbal or written warning to the student. The Student Success Representative will meet with the student, explain the
nature of the violation or behavioral issue and indicate future expectations of the student.
The student will have the opportunity during the meeting with the Student Success Representative to discuss the issues raised with the
faculty member or others. The Student Success Representative will clarify expectations of student conduct. The faculty member or the
Student Success Representative, as appropriate, will document the fact that a verbal warning was given to the student. This note will
include the date, issues discussed, recommendations made and the response by the student. The student will initial the note to indicate
understanding. The incident note will be retained by the Student Success Representatives office.
Step 2: Corrective Action-Written Warning
If a verbal warning has been given to a student and the student did not correct their behavior or in cases where a faculty member or
other College employee believes, after consultation with the Student Success Representative, that more significant Corrective Action
is appropriate, a written warning and additional sanction may be issued. If the issue is related to Academic Misconduct, the faculty
member will meet with the student regarding their conduct and will, in consultation with the Student Success Representative, issue a
written warning to the student. If the issue is related to Non-Academic Misconduct, the Student Success Representative will meet with
the student regarding their conduct and will issue a written warning or appropriate sanction to the student.
In either case, the warning will include the following:
● a summary of the issues related to the academic issue involved or any violations of the Student Code of Conduct or other
College policy;
● a clear statement of what is expected of the student in the future;
● a warning that Disciplinary Action may be taken if the issue is not resolved by the student; and
● a statement that the student is encouraged to discuss the issues raised by the written warning and request assistance in dealing
with these issues.
The student and Student Success Representative will sign the written warning to acknowledge receipt of it and the student shall be
provided with a copy. The student may attach a written statement to the written warning. If the student refuses to sign the written
warning, the Student Success Representative shall note the refusal and the date in the student signature line. The warning and the
student’s response, if any, shall be retained in the student’s academic file.
II. Disciplinary Action
Disciplinary Action is used when a student has failed to correct behavior after being issued a warning or serious violations of the Code
of Conduct and other School policies that apply to students. If a faculty member or other employee believes that Disciplinary Action is
appropriate, the faculty member or other employee shall provide materials and evidence to the Student Success Representative in
order to review the situation. The Student Success Representative shall implement the steps pursuant to the Implementation
Procedures – Disciplinary Action, below.
Removal from Class or Campus – Emergency Basis
A faculty member may remove a student from the classroom if he or she believes that the student’s presence in the classroom poses an
immediate risk to the health or safety to anyone in the school community or to the security of the school, or if the student’s behavior is
so disruptive that the class cannot continue with the student present. The faculty member must immediately notify the Program
Director and Student Success Director. The Program Director shall review the removal and may implement additional discipline
pursuant to the Implementation Procedures – Disciplinary Action, below. Even if no further disciplinary action is taken against the
student, he or she may request a Disciplinary Review as described in the Implementation Procedures, below.

75 | Page
If a College employee believes a student’s presence on campus poses an immediate risk to the health or safety to anyone in the
College community or to the security of the College, they should immediately notify the Program Director and Student Success
Director. The student may be required to leave campus immediately.
Emergency removal from the campus may not exceed 10 days, during which time the student must be given notice to meet with the
Student Success Representative pursuant to Steps One and Two of the Implementation Procedures described below. An emergency
removal from campus may only extend beyond 10 days if the Program Director determines that an extension is necessary to protect
the health, safety or security of the College community. In such circumstances, unless waived by the student, the Student Success
Representative shall develop a timetable for the Disciplinary Action Review that ensures that the student shall complete the process
within 30 days of their meeting with the Student Success Representative.
Non-Academic Probation
Non-Academic probation is a special condition for continued enrollment at ATS Institute. It is different from academic probation
which relates to grades and continued enrollment at the College. Non-Academic probation is appropriate for serious violations of
College policy or when a student has received a written warning but has not corrected their behavior. Non-Academic probation will
continue for at least one academic semester and shall be reviewed at the end of each semester by the Student Success Representative
and any appropriate faculty members or other College employees. The terms and conditions of the academic probation should be
documented and must include:
● A summary of the issues related to the violation of a College policy prompting the Non-Academic Probation;
● A clear statement of what is expected of the student in the future, and the steps required to successfully complete the Non-
Academic Probation;
● A warning that further disciplinary action up to and including dismissal may be taken if the issue is not resolved by the
student; and
● A statement that the student is encouraged to discuss the issues raised with the Student Success Representative and any
appropriate faculty members and to request assistance in dealing with the issues raised in the written summary.
During the semester of the Non-Academic Probation, the Student Success Representative or faculty member may require periodic
meetings with the student to discuss any concerns and to assess progress of the student.
Suspension
If there has been a serious breach of the Student Code of Conduct or other policy that applies to students, the Program Director may
suspend the student upon advice of the Student Success Representative. A suspension is appropriate when a student has failed to
correct behavior after being issued a warning or when there has been a serious violation of policy. A suspension may be from one day
to one academic year depending on the severity of the situation. A suspension of one to nine days is a “Short-term Suspension.” A
suspension of 10 days or more is a “Long-term Suspension.”
Dismissal
Serious breaches of the Student Code of Conduct or other College policy may result in dismissal. It is the most severe penalty for
Non-Academic Misconduct. A student who has been dismissed from the College will not be eligible to be re-enrolled at the College
and bars the student from campus and partner facilities.
A student may be immediately dismissed from school for the following:
● Being under the influence of alcohol and/or illegal drugs while on the school premises or in clinical. This includes marijuana.
● Engaging in sexual harassment or sexual assault.
● Falsification of documentation
76 | Page
● Bullying and Harassment
A student will be immediately dismissed from school for the following:
● Using, selling, possessing, or distributing drugs or other illegal substance.
● Using physical or verbal abuse or violence in any form.
● Possessing a weapon of any kind on school property
Implementing Procedures – Disciplinary Action
Step One: Notice
A student who faces Disciplinary Action will receive a written notice of the intended Disciplinary Action from the Student Success
Representative. The Notice of Intended Disciplinary Action will include:
● A detailed statement describing the reasons for the Disciplinary Action;
● A description of the proposed Disciplinary Action; and
● A statement describing the student’s right to meet with the Student Success Representative pursuant to Step Two of these
procedures.
Step Two: Meeting with Student Success Representative
A student who faces Disciplinary Action may request a meeting with the Student Success Representative within five days of receipt of
the Notice of Intended Disciplinary Action. Such meeting shall be scheduled within five days of the request. During the meeting, the
Student Success Representative shall explain the evidence against the student and allow the student to respond to the charges. Either
during the meeting, or within five days of the meeting, the Student Success Representative shall notify the student whether the
proposed discipline shall be implemented, modified or not implemented.
Disciplinary Action Review
If Disciplinary Action is implemented, the student may request a review of the Disciplinary Action. Long-term suspension or
dismissal shall not be imposed until the disciplinary review has taken place; all other Disciplinary Action may be implemented prior to
disciplinary review. The student has five days from the meeting with the Student Success Representative to file a request for a
disciplinary review. The student is given an opportunity to provide detailed information related to the misconduct and dispute the
evidence presented. The student must submit the Due Process Appeal Form for committee review. Review under this policy
involves:
The Student Affairs Committee will review any of the following items provided by the student:
a. a prepared, written statement rebutting the evidence
b. material evidence that supports the student’s claim
c. the testimony of any others who may have been involved in the incident
Step Three: Director of Nursing and CEO Decision Final
The Director of Nursing and CEO, in their sole discretion, may accept, modify or reject, in whole or in part, the recommendations of
the Student Affairs Committee. The Program Director and CEO will issue a final decision in writing to the parties, which shall be
final and binding upon the parties.

77 | Page
Appendix A: Academic Calendar Spring 2024 – Spring 2025 - updated directly in Catalog
Appendix B: Faculty and Administration - updated directly in Catalog
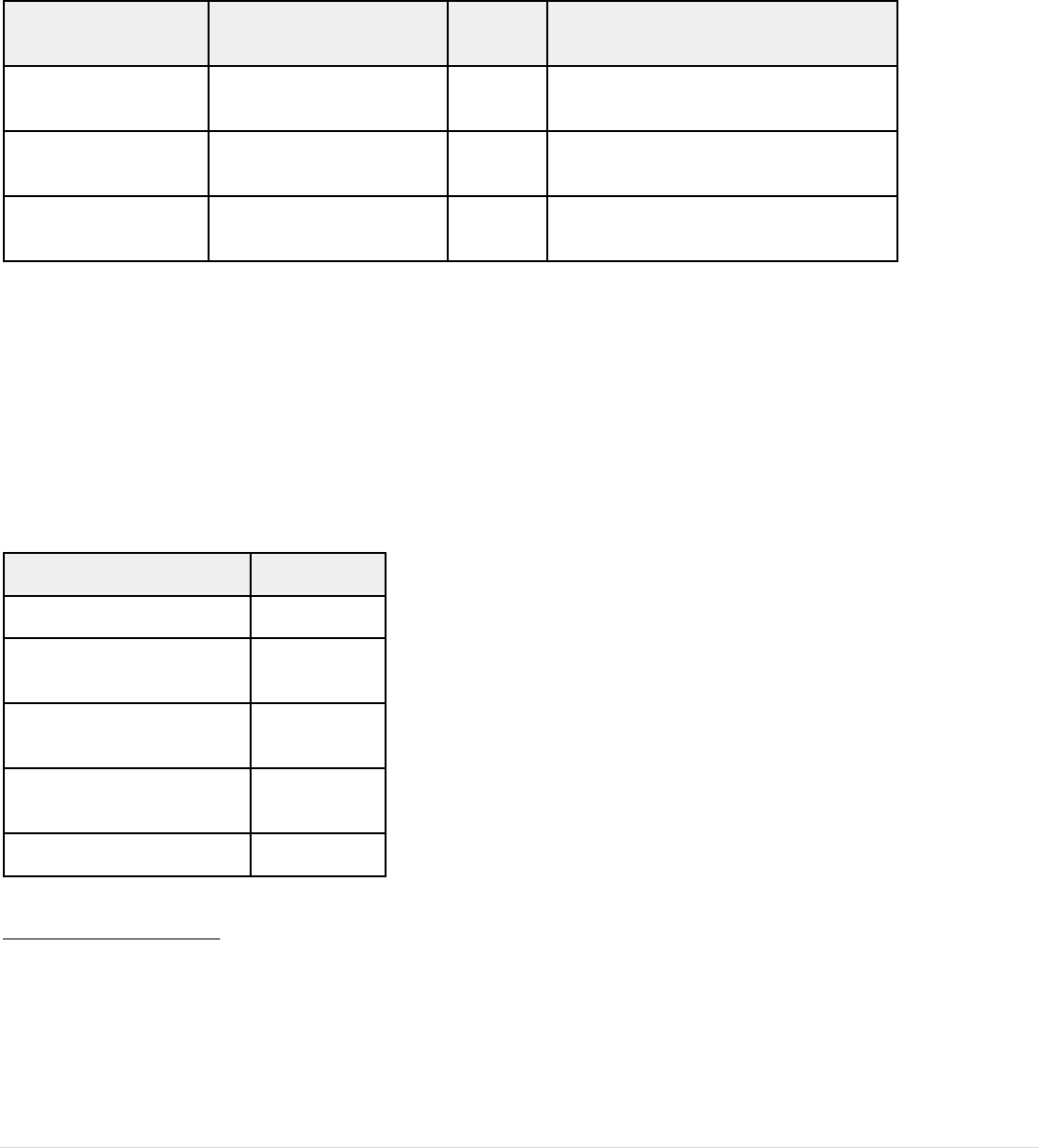
78 | Page
Appendix C: Tuition and Fees
The update replaces the previous Appendix.
Tuition & Fees
Tuition & Fees
Cost Per Semester (3
Semesters)
Total
Cost
Description
Program Tuition &
Fees
$10,400
$31,200
Tuition & Fees
Course Fee
NA
$800
Course Fee for the REV1003 NCLEX
Review course
TOTAL PROGRAM
COST
$32,000
Additional cost for Developmental Courses:
Tuition and fees will be adjusted to reflect scheduled developmental classes in the amount of $2,392 for ENG0930 and MAT0930
courses, $1,316 for ENG0935 course, The total program cost will be no more than $38,100 and the Program Tuition & Fees cost per
semester will be $9,325 over 4 semesters.
The ATS Practical Nursing Program is designed in a sequential order and is offered on a full-time basis. In the case that a student
moves out of their original course sequences and takes a less than full-time load or needs to repeat courses, they will be billed in
accordance with the table below. Once the student moves to their full-time course sequence, they will be charged in accordance with
their original cost per semester.
Financial Aid Credits Tried
Semester Cost
12 or more
$10,400
9 - 11.99
$8,400
6 - 8.99
$7,400
3 - 5.99
$2,700
1 - 2.99
$1,700
Included in the Tuition & Fees:
● Medical Compliance Fees:
● Nursing Lab Kit
● Technology Fee (Software Utilization)
● Books/Resources: subject to change
○ Nursing Fundamentals eBook and resources
○ Art of Nursing/Critical Thinking book and resources

79 | Page
○ Anatomy & Physiology resources
○ Nursing Care of the Adult I eBook and resources
Included in the $800 Course Fee for the REV1003 NCLEX Review course
● ATI Package
○ VATI
○ Live Review
○ Comprehensive Predictor - 1st attempt
MISCELLANEOUS FEES:
● Estimated Book Fees for books not included in tuition is $300. Students are responsible for purchasing books as indicated in each
semester booklist
● The estimated uniform cost is $32. Students are responsible to purchase uniforms and ATS patches in accordance with the
Professional Dress Code Policy. The cost of uniforms and additional supplies may vary depending on purchase location.
Additional supplies may include a stethoscope, watch with a second hand and any other supply requested by the faculty.
● Clinical Site Parking: Students are responsible for payment of parking at clinical sites. The school is not responsible for
reimbursement for parking fees.
● Students are responsible for all fees related to immunizations
● Financial charges may apply for late payments, bounced checks/declined credit cards or double deposited checks
● ID Badge Replacement: $25
● Supplemental ATI exams: $75
● VATI Extension: $100
● Clinical Makeup Fee: $100
POST-GRADUATION ESTIMATED COST: Student is responsible for all post-graduation fees
● Continental Testing Services $98
● Pearson Vue: $200
● Fingerprinting: $65
Appendix L: Academic Monitoring Guidelines
New appendix as of January 2024
Students on Academic Monitoring are required to attend Focused Learning Seminar. This is a mandatory class.
1) Students are emailed at the beginning of the semester notifying them they are on Academic Monitoring and they are required to make an
appointment with a Nursing Success Coach, retention specialist, or advisor as assigned.
2) Students that score below 78% on an exam must meet with their professor for remediation.
3) If a student is referred to a retention specialist for assistance with study skills or to a success coach for content related questions, they are
required to attend these sessions.
Students that do not attend or participate in Academic monitoring and Focused Learning Seminar for more than two weeks will receive a letter of
intent to withdraw and will be withdrawn if no action will be taken by the student.
FLS students who miss a session must make up the missed session by meeting with the FLS instructor individually. Because of the fast pace of the
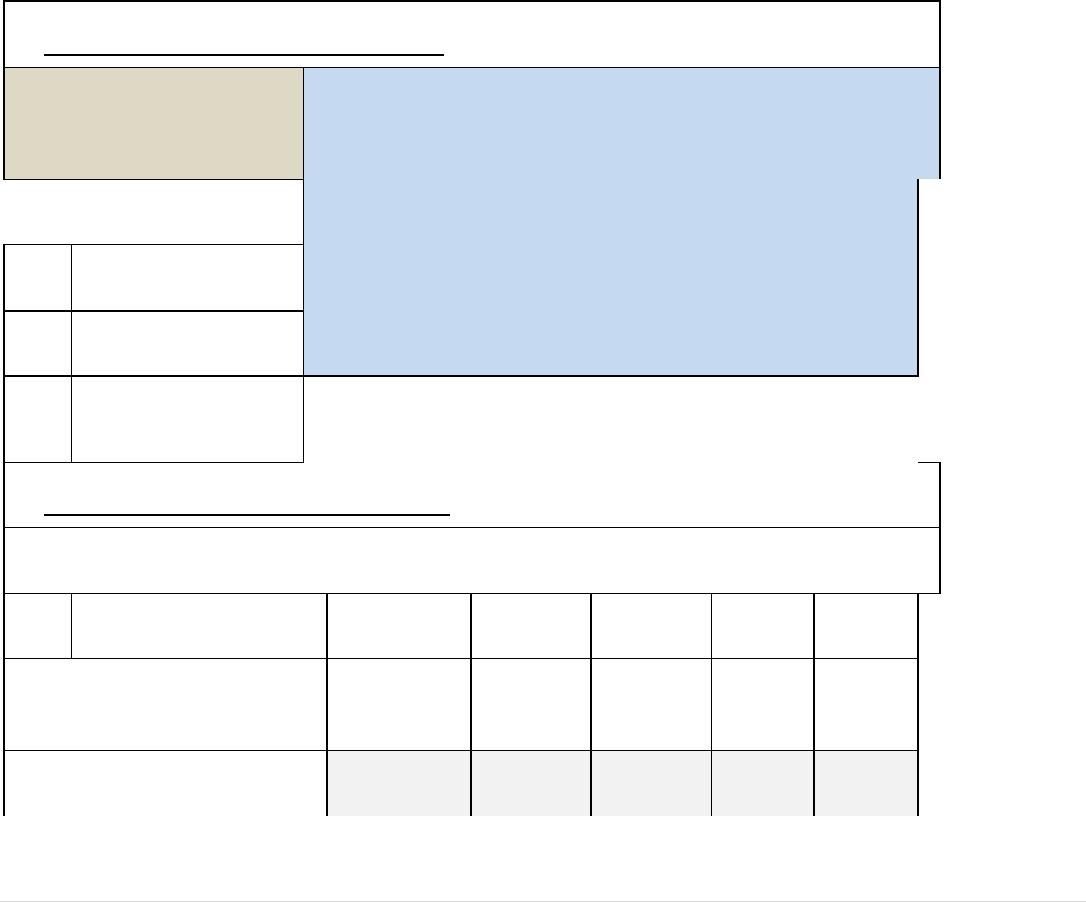
80 | Page
nursing program, it is very important that students who are placed on academic monitoring make an appointment as soon as possible so that any
academic issues can be quickly addressed. Students are expected to comply with all of the components of the Academic Monitoring Policy. Failure
to do so may result in disciplinary action up to and including dismissal from the nursing program
Appendix I: Institutional Disclosures Report
Reporting Period: July 1, 2022 - June 30, 2023
INSTITUTION NAME:
MDT School of Health
Sciences, Inc., dba ATS
Institute of Technology
Indicate all ways the disclosure information is distributed or made
available to students at this institution:
X
Attached to Enrollment Agreement
X
Provided in Current Academic Catalog
X
Reported on School Website
Per Section 1095.200 of 23 Ill. Adm. Code 1095:
The following information must be submitted to the Board annually; failure to do so is grounds for immediate
revocation of the permit of approval.
DISCLOSURE REPORTING
CATEGORY
Practical
Nursing
Program
A) For each program of study,
report:
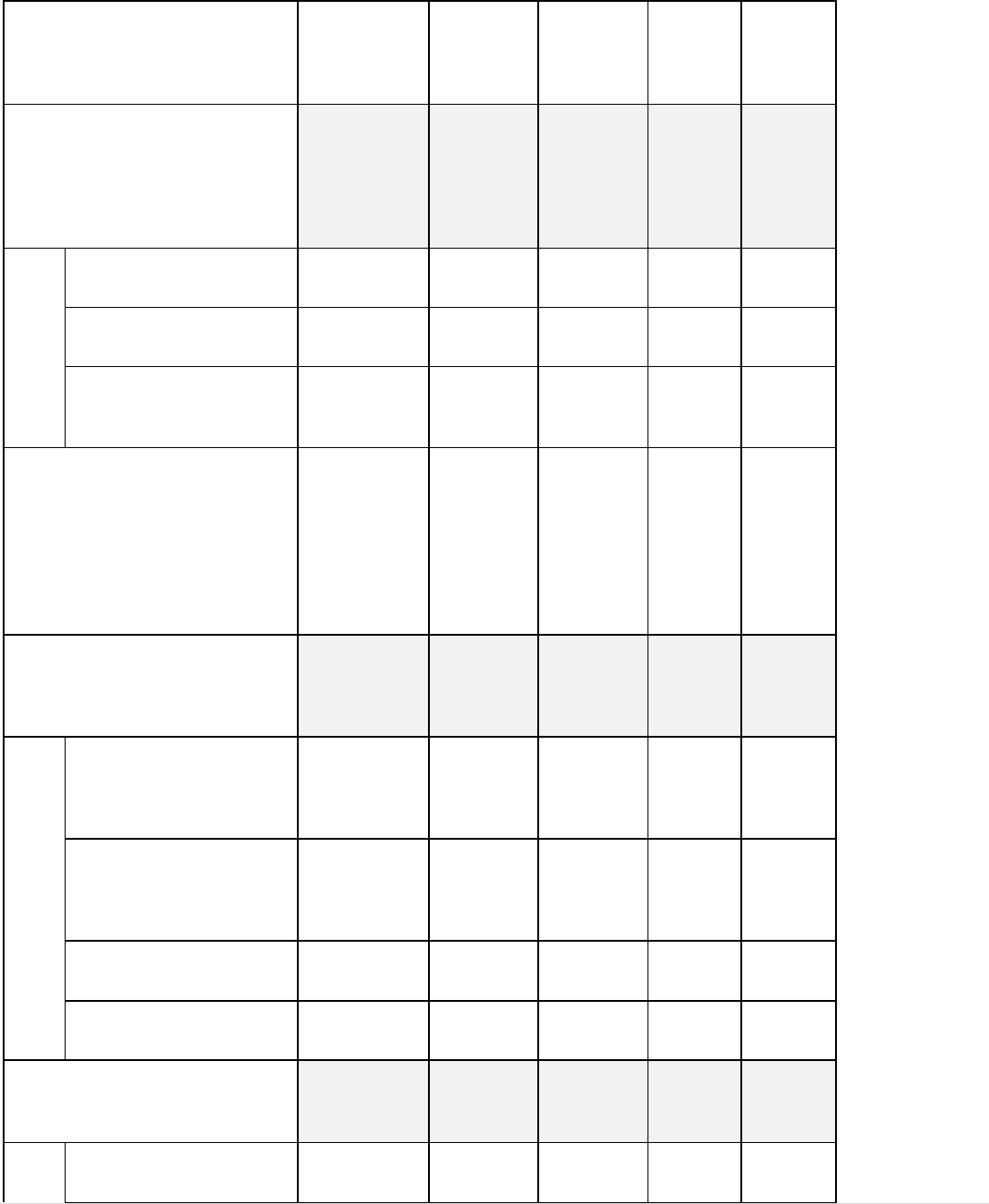
81 | Page
1) The number of students who
were admitted in the program or
course of instruction* as of July 1
of this reporting period.
244
2) The number of additional
students who were admitted in the
program or course of instruction
during the next 12 months and
classified in one of the following
categories:
a) New starts
361
b) Re-enrollments
7
c) Transfers into the
program from other
programs at the school
0
3) The total number of students
admitted in the program or course
of instruction during the 12-
month reporting period (the
number of students reported under
subsection A1 plus the total
number of students reported under
subsection A2).
612
0
0
0
0
4) The number of students
enrolled in the program or course
of instruction during the 12-
month reporting period who:
a) Transferred out of the
program or course and
into another program or
course at the school
0
b) Completed or
graduated from a
program or course of
instruction
88
c) Withdrew from the
school
227
d) Are still enrolled
297
5) The number of students
enrolled in the program or course
of instruction who were:
a) Placed in their field of
study
69
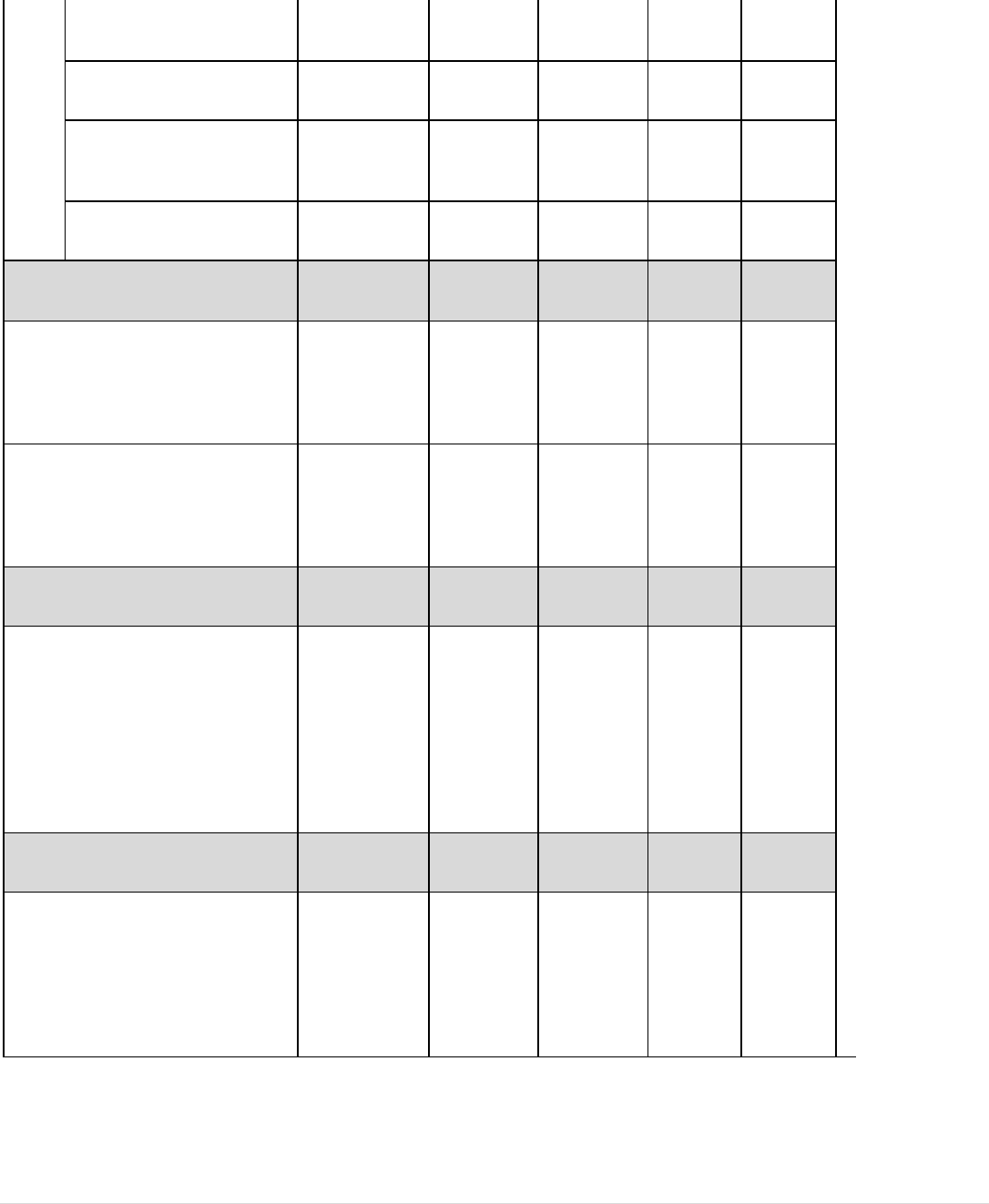
82 | Page
b) Placed in a related
field
9
c) Placed out of the field
0
d) Not available for
placement due to
personal reasons
0
e) Not employed
10
B1) The number of students who
took a State licensing examination
or professional certification
examination, if any, during the
reporting period.
85
B2) The number of students who
took and passed a State licensing
examination or professional
certification examination, if any,
during the reporting period.
79
C) The number of graduates who
obtained employment in the field
who did not use the school's
placement assistance during the
reporting period; such
information may be compiled by
reasonable efforts of the school to
contact graduates by written
correspondence.
unknown
D) The average starting salary for
all school graduates employed
during the reporting period; this
information may be compiled by
reasonable efforts of the school to
contact graduates by written
correspondence.
unknown
83 | Page
Course of Instruction is defined as a standalone course that meets for an extended period of time and
is
directly creditable toward a certificate or other completion credential; individual courses that
make up a
Program of Study are not considered courses of instruction.
Note: As indicated in the PBVS Administrative Rules, Section 1095.200, student retention and
graduation rates must be maintained that are appropriate to standards in the field. Furthermore, a State
licensing examination or professional certification examination passage rate of at least 50% of the
average passage rate for schools within the industry for any State licensing examination or professional
certification examination must be maintained.
} In the event that the school fails to meet the minimum standards, that school shall be placed on
probation.
} If that school's passage rate in its next reporting period does not exceed 50% of the average passage
rate of that class of schools as a whole, then the Board shall revoke the school's approval for that
program to operate in this State. Such revocation also shall be grounds for reviewing the approval to
operate as an institution.

