
Introduction
In 2010, the University of Texas at Austin migrated to a
brand-new $32 million data center. Roughly twice the size
of the university’s previous data center — and the result of
two years of intensive planning and design — the new facility
features a consolidated network architecture and eco-friendly
power and cooling systems. It is expected to reach full
capacity in just three to five years.
1
At that point, the university
will need to expand or migrate its data center yet again.
Not coincidentally, 2010 also marked the first year in which
more data traveled across the Internet than during all the
previous years combined.
2
With such an exponential increase
in data traffic, university IT teams will need to spend an
ever-increasing share of their time simply preparing to
handle projected capacity requirements. Year over year, the
challenge of long-term scalability will only become more
acute. And with university IT budgets sometimes falling behind
the pace of change, schools need to find smart, secure ways
to meet growing demand while controlling costs.
1. Information Technology Services at the University of Texas at Austin, “UDC:
Frequently Asked Questions.”
2. James Temple, “Web 2.0 Summit: Data Explosion Creates Revolution,”
SFGate.com, October 19, 2011.
In the search for a more scalable approach to IT infrastructure,
a growing number of schools see cloud-based computing as
a tremendous opportunity to achieve large-scale efficiencies
without sacrificing performance. Yet in order to realize these
benefits and get the maximum return on their investment,
colleges and universities must take into account the various
challenges and considerations unique to each particular
environment. No cloud solution should be one-size-fits-all.
In the following pages, you will learn how you can take the first
steps toward a custom-built cloud-computing solution by:
• Creating a comprehensive cloud strategy
• Designing a cloud-based architectural model
• Making the transition to the cloud
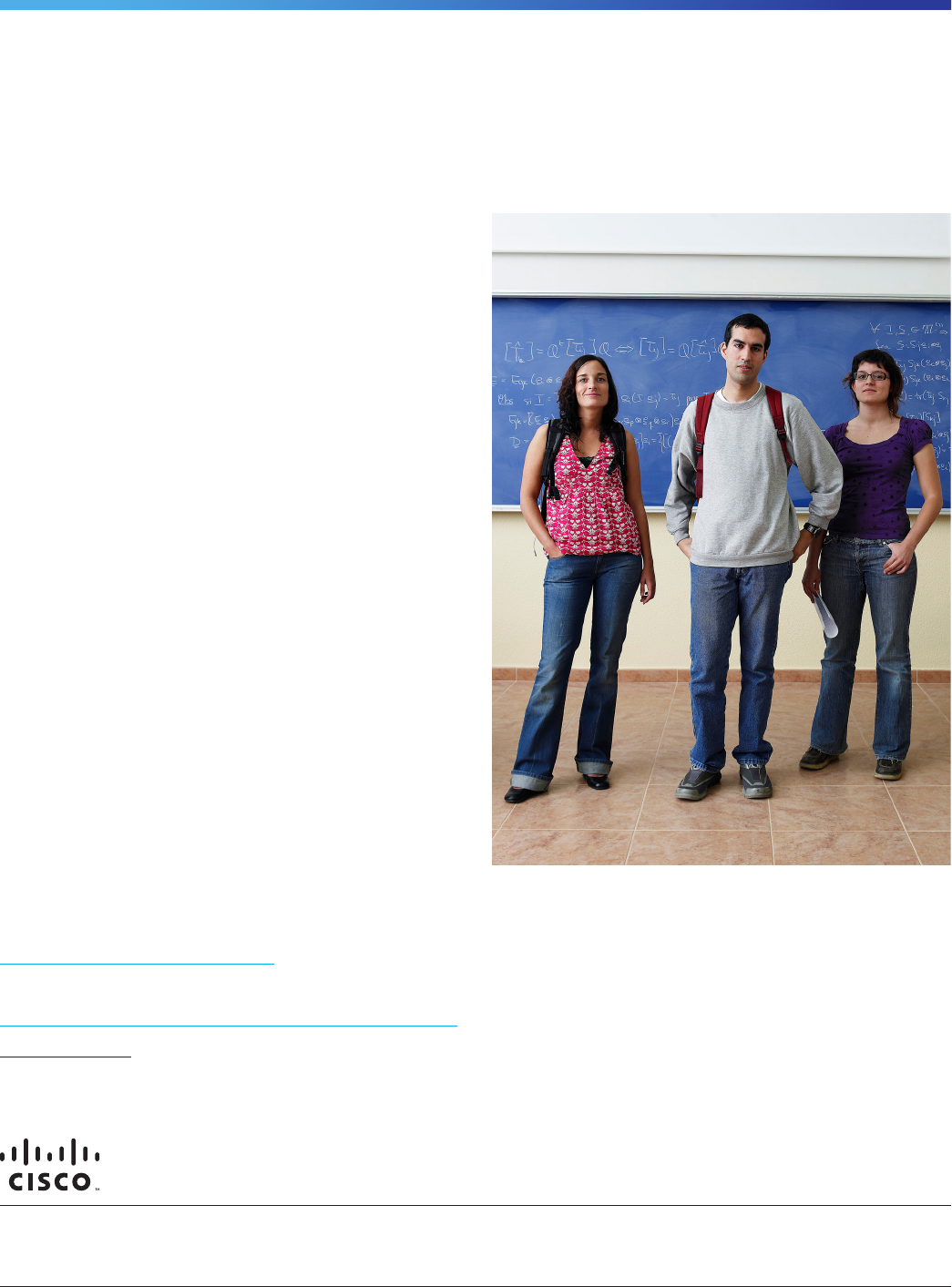
Competing Demands in an Increasingly
Complex Environment
College and university IT organizations are expected to keep
up with a long list of competing demands, such as:
• Deploying applications and delivering web-based student
services at a rapidly accelerating rate, often without a
proportionate increase in budget for hardware, software,
and personnel
Cloud 101: Developing a
Cloud-Computing Strategy
for Higher Education
White Paper
1 © 2012 Cisco and/or its affiliates. All rights reserved.

• Drastically reducing CapEx and OpEx costs while
maintaining the highest levels of security and privacy
• Maintaining a traditional IT infrastructure increasingly unable
to accommodate the growing number of personal devices —
including tablets, smartphones, and laptops — that students
bring into the campus environment
• Offering sufficient bandwidth to accommodate huge swings
in network usage, from the high activity of autumn to the lull
of summer
• Competing against other universities, many of which
attempt to differentiate themselves in the market based on
the services they offer to students
Security is an especially pressing issue for institutions of
higher education. With many faculty members pursuing
patent-pending research, and with student privacy
safeguarded by strict regulations, colleges and universities
must be careful to minimize exposure to legal risk and
compliance risk. A secure and reliable networking
infrastructure is therefore a flat-out requirement.
Fortunately, many higher education institutions have found a
way to meet these competing demands — for greater agility,
less risk, and lower cost — by migrating much of their IT
infrastructure to the cloud.
Increased Adoption, Proven Benefits
The trend in higher education is clearly toward cloud services
adoption. According to a 2011 study by CDW, only 5
percent of U.S. college and university respondents were not
considering a cloud migration. 29 percent had developed a
written strategic plan for the adoption of cloud computing,
with 28 percent in the midst of implementation.
3
In February
2011, the Higher Education Funding Council for England
(HEFCE) developed a new program that would invest up
to £10 million in cloud computing, shared IT infrastructure,
and support to deliver virtual servers, storage, and data
management applications for universities and colleges.
4
This should come as no surprise when considering the many
advantages that cloud computing can offer to institutions of
higher education:
3. “From Tactic to Strategy: The CDW 2011 Cloud Computing Tracking Poll,”
July 2011.
4. http://www.hefce.ac.uk/news/hefce/2011/cloud.htm.
• Fiscal advantages. The 2011 CDW survey reports that for
U.S.-based institutions of higher education, the average
savings from migrating applications to the cloud is 21
percent. This makes perfect sense when you consider that
underutilized infrastructure — especially during off-peak
times of the school year — represents a considerable waste
of hardware, power, management, and cooling resources.
By using a virtualization model and shared infrastructure,
cloud implementations promise greatly reduced expenses
in these areas. This increases long-run capital efficiency,
while allowing university IT departments to bypass complex
provisioning processes, minimize “shelfware,” avoid
Cloud 101: Developing a Cloud-Computing
Strategy for Higher Education
White Paper
2 © 2012 Cisco and/or its affiliates. All rights reserved.
The Cloud and Cloud Services Defined
What is the cloud?
A model for delivering on-demand services,
infrastructure, and application software using the
network.
What are the different types of cloud
deployment models?
• Public cloud: Cloud infrastructure shared or
accessible by all, with applications and services
delivered through the Internet.
• Private cloud: Restricted cloud infrastructure
operated by or on behalf of a specic organization,
available exclusively to approved users aliated with
that organization; cloud services are delivered using
a private network.
• Community cloud: Multitenant, private cloud
infrastructure that supports a specic community,
consisting of two or more organizations.
• Hybrid cloud: Combination of two or more of the
preceding cloud types.
Why opt for cloud services?
The value of cloud services is to help manage — and
make immediately available and useful — information
rather than infrastructure. Since universities are,
after all, centers for the dissemination of information,
this emphasis enables university IT departments to
focus on their unique priorities within the educational
environment.

equipment-obsolescence traps, and comply with green
computing expectations and initiatives.
• Increased efficiency and availability. The cloud model
provides the ability to rapidly acquire, provision, and
deploy new IT platforms, services, applications, and test
environments. With cloud capabilities, months-long IT
hardware procurement processes can be eliminated,
reducing time spent on such tasks to a matter of hours
or even minutes. The cloud model also helps ensure that
university networks are available and secure, regardless
of the circumstances. The result is a more agile and
efficient organization that can swiftly respond to changing
conditions and requirements.
• Simplification and standardization. The cloud consolidates
and simplifies data centers and facilities while standardizing
practices and improving compliance with regard to
security, as well as enhancing access to that most critical
of commodities: information. In addition, IT spending
and practices — which are not often understood or
easily defined — can be unified and clarified under the
cloud-computing model. Cloud implementations enable
universities to build a solution once and then use that
solution many times. This lowers costs, increases reliability,
and reduces time to implementation.
• Innovation. In higher education, the primary purpose of
technology should be to enable and inspire innovation
in the classroom and lab. That means giving educators,
administrators, and students both the applications and the
freedom they need to do their work. With the agility of the
cloud model, IT organizations can try out new applications
with minimal commitment, pay for as much as they use,
and adjust as necessary. The cloud can also offer new
ways for institutions of higher education to explore up-
to-the-minute research opportunities by sharing cloud-
computing resources with other universities.
Management at a Reduced Cost
Considerations Unique to Higher Education
Many higher education IT organizations design migrations
to cloud computing with only their in-house resources and
expertise to guide them. In most cases, this means that
colleges and universities are making the transition without the
benefit of the best practices required for the wide variety of
technologies involved. In fact, a 2011 study shows that only
15 percent of university campuses report having a strategic
plan for cloud computing.
5
This lack of overall strategy is especially surprising when you
consider the importance of security within the campus IT
environment. Security becomes even more of a challenge
as universities begin to use video and wireless to extend
their domestic and global reach so that they can attract new
students to their schools. Nearly one-third of IT professionals
in higher education identified potential security breaches as
the single biggest barrier to cloud adoption.
6
With so many
concerns around security, privacy, and compliance in the
higher education realm, why trust a cloud implementation to a
nonspecialized in-house team?
5.“Colleges Unite to Drive Down Cost of ‘Cloud Computing,’” The Chronicle of
Higher Education, October 16, 2011.
6. Campus Technology, “Higher Ed Optimistic About Cloud Use,” June 2011.
3 © 2012 Cisco and/or its affiliates. All rights reserved.
Cloud 101: Developing a Cloud-Computing
Strategy for Higher Education
White Paper
Cloud Case Study: Enhanced Scalability and Simplified
Management at a Reduced Cost
Berlin’s University of Technology (TU) virtualized
much of its IT infrastructure using the Cisco Unified
Computing System
™
(Cisco UCS
™
). As a result, TU
realizes high scalability through maximum utilization of
resources while simplifying management and gaining a
clear edge over international competitors. Cost savings
have been particularly impressive. For example, TU now
requires only eight cables per blade chassis, achieving
a 90 percent reduction in cabling-related costs.
If institutions of higher education choose to take an in-
house approach, they risk facing common cloud-computing
challenges, including:
• Limited virtualization around the endpoint
computing resources
• Failure to exploit innovative, cost-saving initiatives, such as
business continuity or disaster recovery based in the cloud
• Security inadequately focused at the application or server
layer only
• Lack of customer isolation using secure, scalable,
multitenant services
Some cloud-computing requirements are the same across
all industries. But colleges and universities face particularly
challenging circumstances in the following areas:
• Robust security is critical. Security and data privacy impli-
cations are the foremost concern for many higher education
IT organizations. In the last few years, security has taken on
an added dimension of complexity, due in part to the prolif-
eration of so-called BYOD (bring your own device) programs
at many universities. Many IT teams find themselves simply
overwhelmed by the sheer range of devices requiring at
least some level of on-campus protection.
• The right balance between public and private. Universities
must first determine the right balance between the public
and private cloud, taking all relevant legal and security
issues into consideration, and then pursue a change-
management strategy so that students can understand why
the university favors some applications over others.
• Any strategy should firmly position education as the
university’s number-one priority. In the higher education
space, the goal of cloud computing isn’t necessarily to
reduce headcount in IT. Rather, the goal is to give IT the
opportunity to support the university’s primary function of
educating students.
Every cloud implementation should be as unique as the
campus it serves. When undertaking any major technology
initiative, it is necessary to carefully define objectives and
requirements, aligning them with the business needs as
well as the technology architecture and strategy. It is also
imperative to understand the risks and develop plans for
mitigating them. This approach is critical in order to maximize
success and return on investment.
Designing a Custom Cloud-Computing
Strategy with Help from Seasoned Experts
Since an exclusively internal approach to building a cloud-
based system would use already stretched in-house
resources, one solution for ensuring a successful transition
to the cloud is to turn to a professional services group for
assistance in developing a strategy that best suits your
college or university’s needs.
This team of experts will work with university IT teams to
create a wish list for making the transition to the cloud easier.
Items on the wish list may include:
• Choice of vendors, partners, and cloud-computing solutions
• Alignment with business strategy and goals
• A comprehensive, architectural approach
• A full service and solution offering with robust security
• Measurable benefits such as time-to-market
4 © 2012 Cisco and/or its affiliates. All rights reserved.
Cloud 101: Developing a Cloud-Computing
Strategy for Higher Education
White Paper
Cloud Security Checklist
Here is a checklist of security issues and capabilities
to consider when it comes to optimizing the security of
your cloud implementation:
Data safety
Data condentiality
Data privacy
XML signature
Browser security
Cloud integrity and binding
Network security
Flooding and denial-of-service attacks
Regulatory compliance
Data center location
Dedicated security team to ease transition
With a clearly defined wish list, organizations must then
approach the cloud transition in the following four phases:
1. Strategic Preparation
In this initial phase, IT decision makers will determine the
appropriate cloud computing strategy, asking questions
about architecture and security, as well as about objectives.
Colleges and universities should work with experts who have
extensive experience in multiple technology areas, such as
virtualization, service orchestration, automated provisioning,
and the security that underpins network architectures.
The costs, benefits, and operational changes required to
successfully migrate to a cloud–computing model should
also be evaluated, including both the current and desired
services management approach. A thorough analysis helps
align business results with subsequent cloud architectural
development, tools, process integration, and implementation.
Strategic preparation should also target security. University IT
experts should evaluate their cloud services and architecture
security risks, focusing on protecting access and providing
on-demand security options within a services catalog for their
users. In addition, your strategy should take into account your
cloud-computing evolution and post-deployment activities in
every stage: strategy, planning and design, implementation,
and optimization.
2. Planning and Design
When undertaking a transition to cloud computing, strategic
planning and design can help reduce the time to successful
deployment and operation of complex cloud models. This
phase requires expert coordination among the members of
your team, your partners, and other vendors, as well as a
detailed architecture design, data-center–specific expertise,
and security designed from end to end.
The resulting designs and plans — including, for example, an
end-to-end architecture blueprint, a migration roadmap, a
common control framework, a security technology framework,
physical safety and security, and your future cloud services
evolution — should link back to your strategy and lay the
foundation for subsequent implementation and integration.
3. Implementation
In order to reduce risk during a transition to cloud computing,
college and university IT organizations need to have someone
with experience in providing a virtualized architecture, as well
as integrated tools, a facilities plan, orchestration integration,
workload migration, and staging and validation activities
prior to full-scale implementation. This phase also involves
implementing the security technology architecture, the
security portal design, automated audit, and physical safety
and security designs.
Proven methodologies, best practices, and deep knowledge
of the core systems within the cloud environment can facilitate
a smooth migration from your existing environment to a cloud
utility computing architecture, while helping ensure adherence
to plans and enabling on-time delivery of a fully implemented
cloud-computing model. During this implementation stage,
knowledge transfer should be an ongoing process, providing
operational confidence for in-house experts.
4. Optimization
Optimization of the cloud model, which can accelerate
adoption, is the point where you can maximize the true benefits
of cloud computing: lower operating and capital expenses,
increased business agility and responsiveness, and scalability.
This is done through activities such as:
• Architectural reviews
• Security audits
• Cost-reduction exercises
• Process improvements
• Tool customization
• Post-deployment or Day 2 support
Cloud 101: Developing a Cloud-Computing
Strategy for Higher Education
White Paper
Cloud Case Study: Expanded Capabilities with
Virtualized Infrastructure
At the Chinese University of Hong Kong (CUHK), the
IT team required faster and more flexible provisioning
of resources. By virtualizing operations with Cisco
®
Data Center Business Advantage Architecture, CUHK
achieved more efficient allocation of computing
resources and significant expansion of data center
capability within a constrained physical space.
5 © 2012 Cisco and/or its affiliates. All rights reserved.

Applying Best Practices for a
Seamless Transition
Experts you trust can help you navigate these phases, help-
ing you to decide on the appropriate cloud-computing strat-
egy. These experts can also guide you through architecture
and security planning, design, implementation, and optimiza-
tion techniques.
The Cisco
®
Services approach draws on expansive data
center and virtualization expertise, proven best practice
methodologies, and Cisco’s unique intellectual property
to support cloud-enabling technologies. As a leader in
networking products and solutions, Cisco can help your IT
team develop the secure, high-performance network designs
required for cloud services delivery.
Cisco Cloud Enablement Services help:
• Accelerate the development of a financially justified cloud
strategy with a measurable ROI
• Help ensure that infrastructure-as-a-service (IaaS)
infrastructure, management, people, and processes
maximize the success of the transition to cloud computing
• Accelerate the development and implementation of an IaaS
architecture, integrated tool design, and chargeback and
security mechanisms validated by Cisco
• Create a phased migration plan to help ensure the
successful adoption of the new cloud operational model
• Accelerate time-to-value of a data center architecture for
cloud services creation and delivery
Cisco provides a complete set of service offerings to help
your college or university through each step of its cloud
transition. Figure 1 illustrates the specific areas of focus that
Cisco Cloud Enablement Services offer.
Cloud 101: Developing a Cloud-Computing
Strategy for Higher Education
White Paper
6 © 2012 Cisco and/or its affiliates. All rights reserved.
Assess Strategy
Technology and Security
Management Tools
Operational Readiness
Business Case
Chargeback Approach
Program and Architecture
Infrastructure as a Service
(laaS) Design
Technology and Security
Tools Architecture
Service-Level Agreement (SLA)
Design
Chargeback Design
Program and Architecture
Implement
Technology, Security, Tools,
Facilities
Orchestration Integration
Workload Migration
Staging and Validation
Program and Architecture
Accelerate
Time to Value
Worldwide Expertise
Worldwide Presence
Proven Delivery
Capability
Cisco Services for Cloud Enablement
Cloud
Strategy
Service
Cloud
Planning
and Design
Service
Cloud
Implementation
Service
Figure 1 Cisco Services for Cloud Enablement
No matter what type of cloud model you want to deploy —
hybrid, community, private, or public — Cisco, and our pervasive
ecosystem of industry-leading partners, can support it. The
network is the fabric that links clouds and all their components
seamlessly and securely. With our reputation for integrity, our
focus on security, and our extensive suite of offerings, Cisco
can help your institution meet critical imperatives and make the
transition to cloud computing with confidence.
Conclusion
Innovative institutions of higher education seek to understand
why and how to deploy cloud platforms efficiently and
securely. Ultimately, their choices — regarding opportunities,
approaches, and partners — have the promise to transform the
role of IT in universities everywhere.
In the next five years, institutions of higher education expect
to cut 20 percent of their IT budget by moving applications
to the cloud.
7
That represents a major shift in approach
across the industry — and a major opportunity to increase
organizational efficiency, improve agility, and stimulate
innovation. However, to support a smooth transition and
optimal outcomes, college and university IT organizations
must first develop a comprehensive cloud-computing strategy
that addresses the challenges unique to each institution.
To learn how your university can accelerate its cloud initiative
with a comprehensive strategy informed by proven best
practices, schedule a discovery session with Cisco Cloud
Enablement Services today.
For More Information
Cisco Cloud Enablement Services:
www.cisco.com/go/cloudenablement
Cisco Cloud Computing for Higher Education:
www.cisco.com/web/strategy/docs/education/092111Cloud.pdf
7. “From Tactic to Strategy: The CDW 2011 Cloud Computing Tracking Poll,”
July 2011.
Cisco has more than 200 oces worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco Website at www.cisco.com/go/oces.
© 2012 Cisco and/or its aliates. All rights reserved. This document is Cisco Public. Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its aliates in the
U.S. and other countries. A listing of Cisco’s trademarks can be found at www.cisco. com/go/trademarks. Third-party trademarks mentioned are the property of their respective
owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1007R)
Americas Headquarters
Cisco Systems, Inc.
San Jose, CA
Asia Pacic Headquarters
Cisco Systems (USA) Pte. Ltd.
Singapore
Europe Headquarters
Cisco Systems International BV Amsterdam,
The Netherlands
Cloud 101: Developing a Cloud-Computing
Strategy for Higher Education
White Paper
